- Checkmarx Documentation
- Checkmarx One
- Release Notes
- Current Multi-Tenant Version | 3.59
Current Multi-Tenant Version | 3.59
Note
As of May 3, 2026, the sca-resolver macOS installer binary for version 2.13.3 has been re-signed. The checksum has been updated accordingly to reflect the new artifact.
This change affects all previous sca-resolver macOS installer versions, which are now revoked. Users should update to version 2.13.3.
Note
We released version 2.3.51 of the Checkmarx One CLI, which has a re-signed certificate of the ast-cli binary for macOS. The certificate for previous versions of macOS CLI binaries have been revoked. macOS users should update to CLI version 2.3.51.
New Features and Enhancements
Enhanced Email Body for Exported Reports
General Availability: June 7, 2026
The HTML email body for reports sent by email now includes a structured header and a metadata section tailored to each report type, improving readability and customer-facing presentation.
Analytics Dashboards: Improved Tag Filters
General Availability: June 7, 2026
When filtering the Analytics dashboards by tags, you can now specify which entity (application, project, scan) or combination of entities the filter applies to, enabling more granular and accurate filtering.
SAST Scanned Files Section in Project Report
General Availability: June 7, 2026
Added a new section, SAST Scanned Files, to the Project Report. This section lists each file analyzed during the SAST scan along with the number of vulnerabilities identified by the SAST scanner in that file.
You can specify to include (default) or exclude this section when generating reports via the UI or API. It is available for reports in PDF or JSON format.
This addition improves report completeness for audit, compliance, and governance use cases, and provides a more consistent reporting experience for teams migrating from CxSAST on-prem to Checkmarx One.
Improved Keyboard Accessibility in Import Project Flow
General Availability: June 7, 2026
The Import Project wizard now includes improved keyboard accessibility for the project configuration flow. All service buttons are now fully focusable and operable via keyboard, and focus correctly reaches the Select Service section in sequence.
This update ensures enterprise users can complete project configuration and manual scan setup workflows without a mouse, improving WCAG 2.2 compliance and readiness for accessibility audits.
Persistent Confidential Header Banner
General Availability: June 7, 2026
A persistent, non-dismissible header banner has been added to Checkmarx One. The banner appears at the top of all pages and remains visible throughout the session. Users cannot close, minimize, or remove it.
The banner is disabled by default. Checkmarx administrators can enable it on a per-tenant basis and customize the banner text via Global Settings. The default text is Confidential. Configuration changes take effect on the next session refresh.
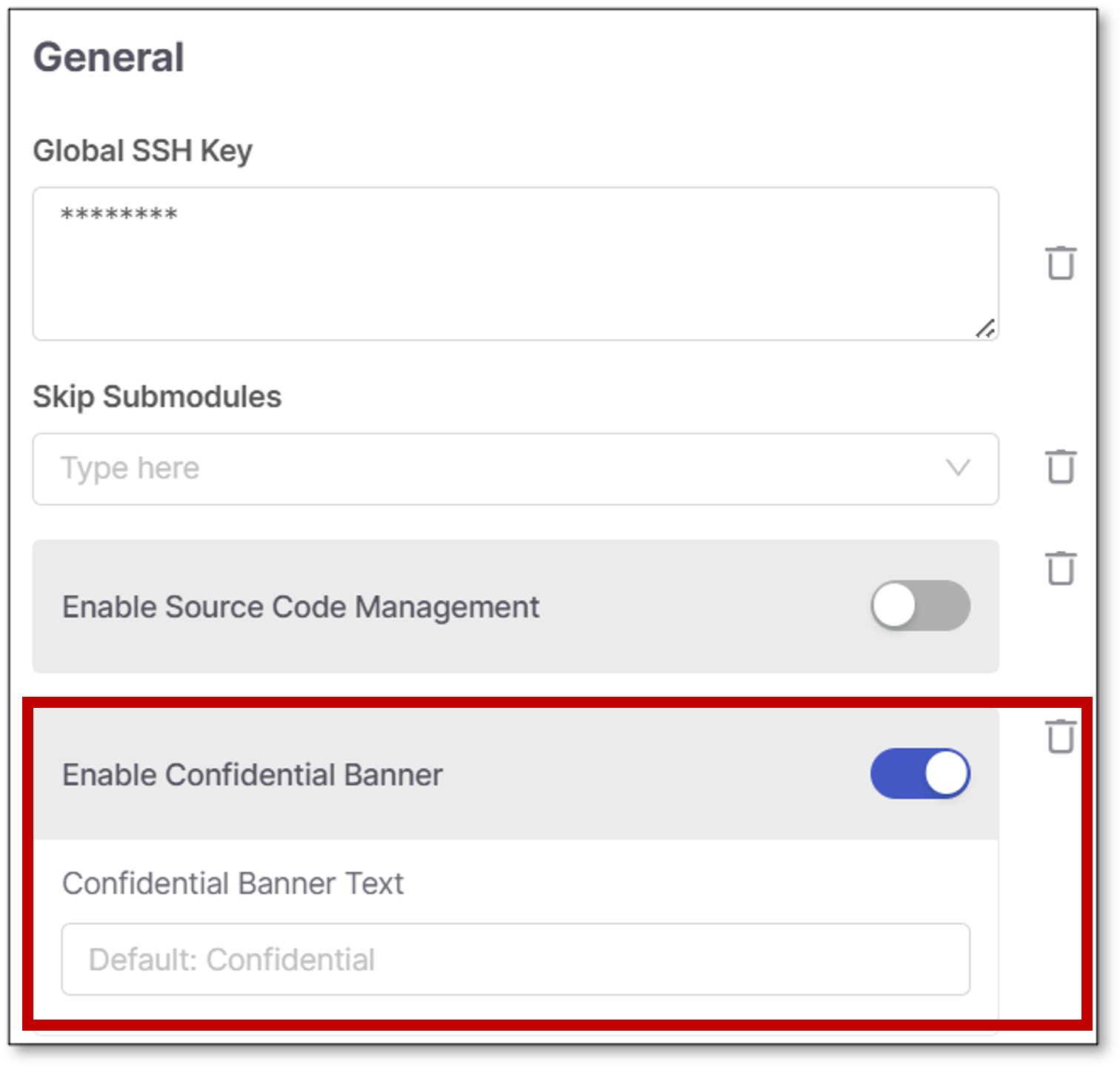 |
This addition supports compliance with internal data classification requirements, ensuring confidentiality status is clearly and continuously communicated to all users.
Added Developer Assist Seats to License Page
General Availability: June 7, 2026
The License page now displays Developer Assist seat usage alongside existing contributing developer information, with a breakdown by IDE.
The exported CSV file has also been updated to reflect both contributing developer and Developer Assist usage data.
Rescan Without Re-uploading Source Code
General Availability: June 7, 2026
Checkmarx One now supports rescanning a project directly from the latest source code already stored on the server, without requiring a new upload. The Rescan option is accessible from the actions menu of each project in the projects table.
Rescans are based on the last successful scan of the project, use the same engines, and automatically apply any updated project settings such as presets, exclusions, or scan mode changes. This feature is also available via API.
By eliminating repetitive file uploads, rescanning saves time, reduces manual effort, and ensures vulnerability assessments always reflect the most current code and configuration.
Improved Net-New Vulnerability Policy Controls
General Availability: June 7, 2026
Policy management now supports configuring Net New Vulnerability rules at the scanner level, with severity thresholds set independently per scanner. Pull request results reflect the specific scanners and severities configured in the rule, reducing noise from scanners not relevant to the evaluation.
In addition, the Break Build option has been moved to the global policy level, outside individual rules.
These update give security teams greater precision in enforcing vulnerability policies.
AI Supply Chain Security (AISC)
General Availability: June 7, 2026
AI Supply Chain Security (AISC) provides visibility into the AI components embedded in your code, helping address the growing challenge of Shadow AI - untracked models, agents, and integrations that introduce risk, unclear data flows, and compliance concerns.
AISC discovers and classifies AI assets directly from source code and configuration, identifying components such as MCP clients and servers, AI agents (for example, LangChain and Semantic Kernel), AI models, core ML libraries (for example, PyTorch and TensorFlow), and AI SDKs (for example, OpenAI, Anthropic, Vertex AI, and Hugging Face).
The feature includes end-to-end capabilities to operationalize this visibility, including scan orchestration for consistent analysis across projects, a dedicated results viewer for exploring detected AI assets, CLI support for CI/CD integration, and policy management to enforce governance and compliance.
With AISC, teams can uncover hidden AI usage, assess risk early, and maintain control over AI adoption across their software supply chain.
For more information, see AI Supply Chain Security.
SCA
Package Upgrade Recommendations
General Availability: June 7, 2026
We have introduced Package Upgrade Recommendations, based on our proprietary algorithms, in the SCA Results Viewer. This provides actionable guidance to help you identify and prioritize safer dependency upgrades.
A new Suggested Fix column in the Packages tab highlights what upgrade options are available for each package (None, Next, Latest), with color-coded indicators distinguishing between full (green) and partial (purple) remediation. Hover over a value to see additional details and click on the value to open a sidebar that shows both the minimal update and the latest version that offer the best remediation options. There is also a link to the AppSec Knowledge Center where you can see a full analysis of the vulnerable package. In the Risks tab, a new Risk Resolution column delivers targeted fix recommendations per vulnerability, enabling more granular remediation decisions.
Aside from the scan results viewer, these insights are also available on the Global Inventory screen as well as in the exported CSV files.
These recommendations reduce the time and effort required to remediate open-source vulnerabilities, helping teams make faster, more informed upgrade decisions.
For more information, see Package Upgrade Recommendations
Improved Delta Scan Accuracy
The Delta Scan feature in SCA has been updated to better determine when a full scan is required. The set of monitored files per package manager has been expanded, and scan arguments and platform configurations are now factored into the delta evaluation - ensuring that relevant changes always trigger a full scan and produce accurate results.
Added Production Dependency Rule to Policy Management
General Availability: June 7, 2026
A new rule, Is Not a DEV or TEST Dependency, is now available in Policy Management under the Package Instance category. It evaluates to true when a package is not classified under either DEV or TEST scope, replacing the need to manually combine two separate rules. This enables more precise and efficient production dependency policy enforcement.
Expanded Support for Private Registry Scanning
SCA scanning now supports an expanded set of private registries, enabling teams to analyze dependencies from credential-protected and on-premises sources. The following capabilities were added:
Support for GitHub registries - A setup wizard on the Integrations screen guides you through submitting your access credentials and creating the integration. Once configured at the account level, you add the relevant connection details to the configuration files in each applicable project.
Gradle and Pip package managers are now supported for scanning on-premises or credential-protected repositories, joining the existing support for NuGet, Maven, and npm.
These enhancements give development teams greater flexibility to secure their full dependency landscape, regardless of where packages are hosted.
Learn how to set up the GitHub integration here.
Learn how to configure Gradle and Pip projects here.
IaC
IaC updates are documented in the IaC changelog.
DAST
Automated Security Testing from Recorded Flows
You can now record a browser flow and automatically turn it into runnable security tests. Your recording is converted into a DAST/API scan that uses your latest authentication details and follows the exact steps you performed with no manual setup.
When you run recordings through the CLI, you can assign a recording name. If you reuse the same name, CheckmarxOne will overwrite the previous recording, ensuring your scans always run against the most current version of your flow.
Editing the API Collection and Authentication Scripts from Settings
Both API and Web environments now let you manage your uploaded API collection and authentication scripts directly in an environment’s Settings, including viewing, downloading, deleting, editing, and adding new files.
Business Flow Management for Recordings
General Availability: June 7, 2026
Define business flows for each environment by organizing your recordings into sequences. You can upload single or multiple recordings, set their order, reuse recordings across flows, and edit or replace them as needed.
If you delete a recording, you will see how many sequences use it, and those sequences will skip that step. During scans, recordings run in the order you set. If a specific recording fails, any recordings that depend on it are skipped, and you receive a clear error with a screenshot so you can fix the issue.
IAM
New Features and Enhancements
DCR (Dynamic Client Configuration) is enabled for all Checkmarx One customers (per-realm in Keycloak) with an increased client limit and basic lifecycle management.
Created a new OAuth client - cx-mcp-client - for MCP/AI Agent authentication.
The colon (:) character is now supported in group names.
Split reader and writer data was implemented.
Email templates were refactored to reduce code duplicates and prepare for new customisations.
API: Added filter by group ID.
Support integration of new GET Users with UI.
CLI and Plugins Releases of May 2026
Note
As of June 14, 2026, Dev Assist remediation can be triggered via natural language chat in your AI Assistant. For more information, see Remediation Via Chat.
CLI Version 2.3.51
The ast-cli binary for macOS has been re-signed and the certificate for all previous versions of macOS CLI binaries have been revoked. macOS users should update to this version
Added file extension
.vmto the list of supported files that are included in the .zip archive that is scanned.
CI/CD Plugins
In May we released the following CI/CD plugin versions:
Jenkins Plugin - 2.0.13-848.v76e89de8a_053 (uses CLI v2.3.51)
General improvements and bug fixes
Plugin | Marketplace | Code Repository | Documentation | Changelog |
|---|---|---|---|---|
Azure DevOps | https://marketplace.visualstudio.com/items?itemName=checkmarx.checkmarx-ast-azure-plugin | |||
GitHub Actions | https://github.com/marketplace/actions/checkmarx-ast-github-action | |||
Jenkins | ||||
TeamCity | https://github.com/CheckmarxDev/checkmarx-ast-teamcity-plugin |
IDE Plugins
No new releases in May
Get Latest Version from Marketplace | Changelog | Documentation |
|---|---|---|
Resolved Issues
Item | Description |
|---|---|
AST-127634 | Container SBOM report generation failed or did not complete successfully. |
AST-154899 | CxLink contained potential security vulnerabilities. |
AST-146678 | The DAST CLI exited with code 2 and reported a failure when ZAP completed with warnings, even though scan results were successfully available in the UI. |
AST-144104 | DAST CLI scans were marked as partial due to failures while uploading logs. |
AST-134417 | A specific project within an application displayed N/A instead of actual results. |
AST-131792 | Scans failed during source fetching with ErrCode=34050 due to branch clone errors. |
AST-98366 | The SAST results viewer mixed results from different queries. |