- Checkmarx Documentation
- Checkmarx One
- Release Notes
- Current Single-Tenant Version | 3.58
Current Single-Tenant Version | 3.58
New Features and Enhancements
Audit Trail – Log Scheduled Scans Events
The Audit Trail now includes full visibility into scheduled scan activity. This enhancement logs all key actions related to scheduled scans, including creation, updates, enable/disable actions, deletions, and execution events (triggered, failed, or skipped). Users can access these events via the New Audit Trail API.
By extending audit coverage to scheduled scans, this feature strengthens governance and compliance readiness, enables accurate forensic analysis, and provides complete traceability for scan automation workflows.
Full File Path for Nodes in SAST Results Viewer
You can now view the full file path for nodes in SAST Results Viewer, making it easier to understand the scope of a vulnerability and improve triage. Clicking a node reveals its full file path. Multiple nodes may originate from the same file or from different files.
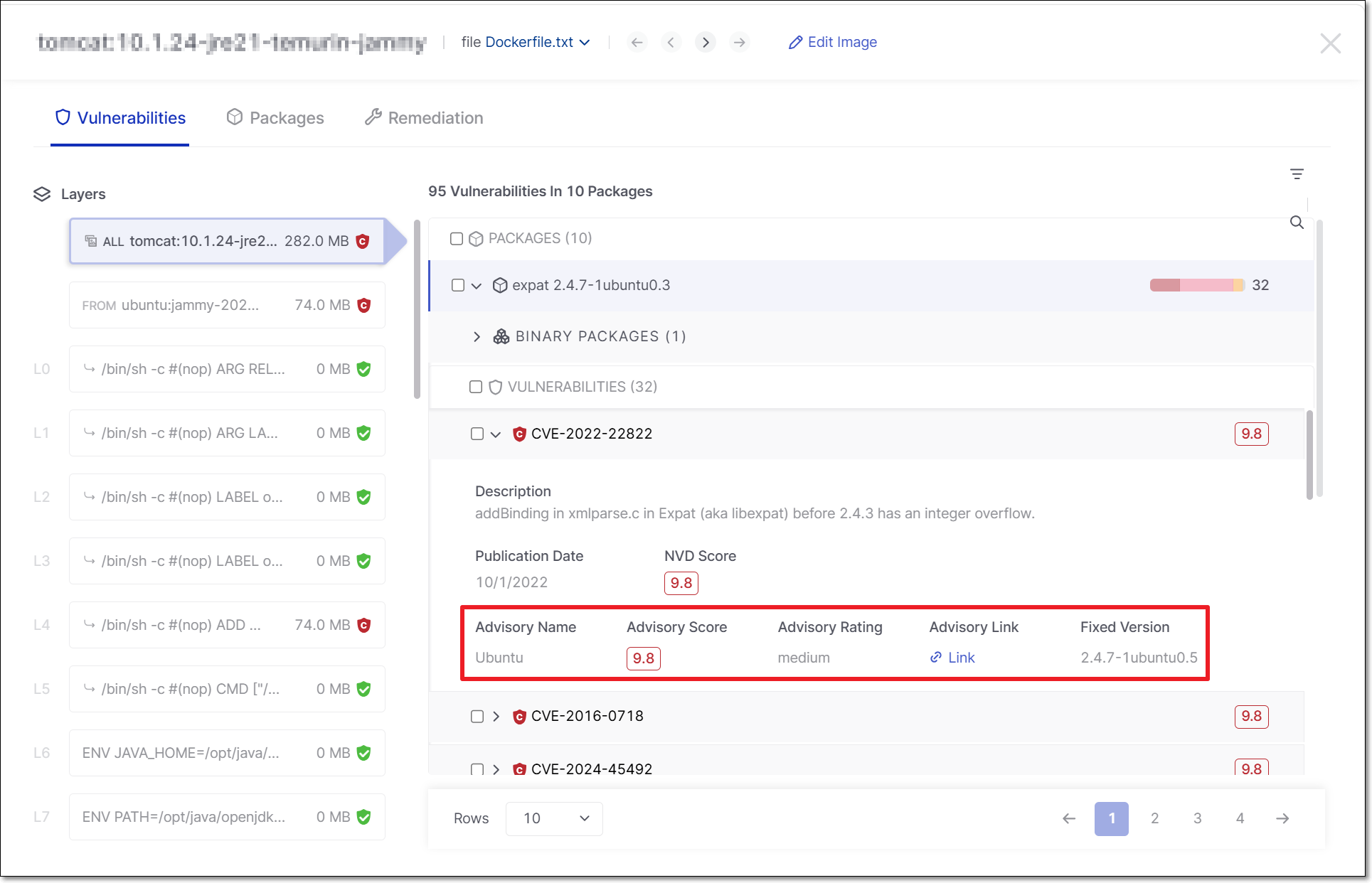
Container Security: CVSS Score and Fix Data for OS Package Vulnerabilities
Container scan results now include CVSS score, affected version range, fix version, and advisory rating for OS-level package vulnerabilities, based on official distribution sources (e.g., OVAL, Alpine SecDB, Red Hat advisories). The NVD score serves as the primary severity score, while advisory scores and ratings from individual vendors are shown as supplementary context and may not always match the NVD score.
This data is available across the UI, API (GraphQL, gRPC), CLI, and exports.
With this enhancement, you can quickly determine whether vulnerabilities are fixable, prioritize issues based on authoritative NVD severity scores, and make more informed risk and patching decisions for base image vulnerabilities.
 |
Microsoft Teams Integration Update for Feedback Apps
The Microsoft Teams integration used by Feedback Apps has been updated to replace the deprecated Office 365 Connectors with Microsoft’s supported Teams webhook mechanism.
This change ensures continued delivery of feedback notifications to Teams channels following Microsoft’s connector retirement. Customers will need to update their Teams webhook configuration after deployment using the new Microsoft Teams Workflows webhook URL.
AI-Powered Image Detection and Correlation in Cloud Insights
Cloud Insights now leverages AI to enhance container image detection and correlation in three key areas:
Identifying 3rd party images
Extracting commit hashes and source URLs
Matching runtime images to Checkmarx Projects
View Vulnerability Delta Between Production and Latest Scan
Cloud Insights now highlights changes in vulnerability counts between the image currently in production and the latest project scan. A new Image → Latest Scan column in the Cloud Insights Inventory clearly shows the delta, helping teams identify risk increases before code is deployed.
You can filter projects by security trend and sort by total delta to quickly pinpoint areas where risk is rising. This makes it easier to assess the impact of upcoming releases, prioritize remediation efforts, and prevent vulnerable code from reaching production.
For more information, see Cloud Insights.
Smart Documentation Suggestions in Checkmarx One Support Ticket Flow
Checkmarx One now suggests relevant documentation articles in real time as users begin typing in the Subject field when creating a support case in the UI.
Suggestions include the article title, a short summary, and a direct link to the documentation, helping users quickly find answers and potentially avoid opening a ticket.
For more information, see Contacting support.
Risk Management: Assign Users and Groups
Checkmarx One Risk Management now supports assigning findings to specific users or groups, enabling clear ownership and more efficient remediation workflows.
A new Attribution column allows authorized users to assign or remove users and groups per finding. Assignments are limited to users within the tenant and require appropriate permissions, ensuring only relevant users can be selected. Changes are reflected in real time across all consuming systems.
To support governance, a new permission - manage-vulnerability-assignees - is introduced and must be combined with existing update permissions to modify assignments. Assigned users can optionally receive email notifications, helping ensure timely awareness and action.
This feature improves accountability, reduces duplicate work, and streamlines risk management by ensuring each finding has a clear owner.
For more information, see Risk Attribution.
Added Support for ADO Organization-Scoped PAT
For Azure DevOps (ADO) Code Repository integrations the use the "Self-Hosted" flow, we now support organization-scoped Personal Access Tokens (PATs). This removes the need to use Global PATs, which grant excessive permissions and are planned for deprecation by Microsoft.
Users can configure integrations by providing a PAT scoped to a specific organization, with validation performed against that organization during setup. Only the organization associated with the PAT is displayed. If you would like to include multiple organizations in a single configuration, you can create a separate PAT for each organization and, in the setup wizard, click Add Organization to submit the additional PATs.
Notice
The existing integration using the global PAT continues to function as long as it remains supported by Microsoft.
This update improves security, flexibility, and long-term compatibility.
For more information, see Azure DevOps Self-Hosted.
Support REST API Project Import for ADO
The REST API for creating new Code Repository Integration projects now supports Azure DevOps (ADO) (in addition to existing support for GitHub). For more information, see API documentation.
Improved SAST Scan Efficiency for Unchanged Code
SAST now includes Skip Scan for Unchanged Code Sources, a new optimization that automatically detects when a scan would produce identical results and skips re-execution, reusing the results from the previous scan instead.
When source code, engine version, query configuration, and SAST settings are all unchanged since the last completed scan, the new scan is marked as canceled with the reason "No code changed" noted in the scan log. This applies to scans triggered via the UI, API, or CI pipelines.
SCA
Added Support for Python 3.14
Checkmarx One now supports dependency resolution for Python 3.14 for scans run in the cloud as well as via SCA Resolver. This enables accurate SCA scanning of Python 3.14 projects, helping to maintain continuous visibility into security and license risk for customers who are adopting the newer Python version.
Added Support for .NET 10 (LTS)
Checkmarx One now supports dependency resolution for .NET 10 (Long-Term Support), enabling teams to scan NuGet dependencies in .NET 10 projects. As an LTS release, .NET 10 is the preferred target for enterprise and production workloads, making reliable SCA coverage essential for maintaining a secure open-source supply chain over its multi-year support lifecycle.
Added Support for Java 25 (LTS)
Checkmarx One now supports dependency resolution for Java 25 (Long-Term Support), enabling teams to scan Maven and Gradle dependencies in Java 25 projects. As an LTS release, Java 25 is the preferred target for enterprise and production workloads, making reliable SCA coverage essential for maintaining a secure open-source supply chain over its multi-year support lifecycle.
Preserve Exploitable Path Info in Recalculated Scans
When a scan recalculation is run, we now preserve Exploitable Path and Package Usage data from the original scan. Previously, scan recalculation would overwrite exploitability and usage data even when the the underlying source code and dependencies had not changed. With this improvement, risk assessment remains accurate and consistent after recalculation.
Additional OSS License Support
We added support for identifying the following licenses that apply to OSS packages: AFL-3.0, CPAL-1.0, OSL-3.0, APSL-2.0, Watcom-1.0 and LPPL-1.3c.
Python and NuGet Support for Automated Remediation Workflows
SCA remediation now supports Python and NuGet packages. You can download a remediated manifest file (e.g., requirements.txt for Python and *.csproj for NuGet) with secure package versions directly from the UI or via the export service API. In addition, the Auto Pull Request feature will automatically generate pull requests targeting vulnerable Python packages in the correct repository and branch. Each pull request contains only the secure version changes, along with any associated manifest files required for full remediation.
This expansion brings Python and .NET developers into parity with existing Auto-PR workflows, giving teams both automated and manual remediation paths to address open-source vulnerabilities across a broader range of ecosystems.Learn more about Exporting Remediated Manifest Files and SCA Auto Pull Requests.
IaC
IaC updates are documented in the IaC changelog.
DAST
Upload Selenium Scripts in Environment Setup
You can now upload Selenium scripts in the Authentication step in the Environment Setup Wizard. Selenium scripts are executed whenever ZAP launches a browser through Selenium- for example, during an Ajax Spider scan or while performing manual exploration.
These scripts have full access to the active browser instance, allowing them to interact with it directly. This includes running JavaScript, navigating to URLs, filling out forms, clicking buttons, and modifying localStorage or sessionStorage.
Aligned CLI with UI
The CLI is now fully aligned with the UI. For more on DAST CLI commands, see here.
Support for Custom States in DAST
Added support for custom states in DAST. Custom states are states that you define to help organize and triage your scan results. For more information on Custom States, see here.
URL Inclusion Enhancements
DAST now helps you include all required URLs for full scan coverage and successful authentication.
DAST scans start from the main URL you define, but many applications use additional domains or paths. If these URLs are not included, authentication may fail or parts of the application may not be scanned. DAST now prompts you to include authentication URLs during setup and shows all discovered but non‑included URLs in the authentication report, error messages, and configuration settings so you can easily add the paths that matter.
Insights in DAST
Insights provide important scan‑related information that isn’t classified as a vulnerability. They flag conditions that can affect scan accuracy or indicate external issues such as authentication failures, blocking mechanisms, or repeated server errors.
If a High‑level Insight is detected, the scan stops and is marked Failed to prevent misleading or incomplete results. A full list of the available insights is viewable here.
CLI and Plugins Releases of April 2026
CLI Version 2.3.48
General improvements and bug fixes.
CI/CD Plugins
In April we released the following CI/CD plugin versions:
Improvements and Bug Fixes
Status | Item | Platform | Description |
|---|---|---|---|
NEW | General | Azure DevOps, GitHub Actions | General improvements and bug fixes |
Plugin | Marketplace | Code Repository | Documentation | Changelog |
|---|---|---|---|---|
Azure DevOps | https://marketplace.visualstudio.com/items?itemName=checkmarx.checkmarx-ast-azure-plugin | |||
GitHub Actions | https://github.com/marketplace/actions/checkmarx-ast-github-action | |||
Jenkins | ||||
TeamCity | https://github.com/CheckmarxDev/checkmarx-ast-teamcity-plugin |
IDE Plugins
In April we released the following IDE plugin versions:
Improvements and Bug Fixes
Status | Item | Platform | Description |
|---|---|---|---|
NEW | General | Eclipse, Visual Studio | General improvements and bug fixes |
UPDATED | Remediation Agent | JetBrains, VS Code | Changed the behavior so that when connection to the Checkmarx MCP is not available, the remediation agent seamlessly offers remediation for all types of risks based on the IDE's LLM. When this occurs, we provide a notification indicating that the recommendations are not based on Checkmarx's specialized models. |
Get Latest Version from Marketplace | Changelog | Documentation |
|---|---|---|
Resolved Issues
Item | Description |
|---|---|
AST-139508 | Searching within code (Ctrl+F) in the results view did not work reliably. |
AST-137663 | Scans failed with a “failed to open file for writing” error. |
AST-136230 | Renaming a project to an existing project name incorrectly returned a success message. |
AST-134821 | Opening query details removed the query from a custom preset in preset management. |
AST-133691 | The “Timestamp Disclosure - Unix” finding was missing evidence. |
AST-131338 | The “Secret Without Expiration Date” query included a misleading description. |
AST-131004 | IaC Web Audit sessions timed out unexpectedly. |
AST-130062 | IaC queries produced errors due to unhandled %s placeholders in expected and actual values. |
AST-127589 | IaC produced inconsistent results between main.tf files and plan.json. |
AST-127417 | IaC queries triggered a database error: ON CONFLICT DO UPDATE command cannot affect row a second time. |
AST-127003 | A false positive was reported for “Bicep - Web App Not Using TLS Last Version.” |
AST-141629 | The export tool generated an empty results mapping file when remarks were empty, resulting in no results appearing in Checkmarx One. |
AST-137638 | The “Cloud Metadata Potentially Exposed” DAST finding was incorrectly reported. |
AST-135547 | Generating DAST scan reports failed when scans contained a large number of vulnerabilities. |
AST-135474 | The Results Summary REST API returned incorrect results for certain flows due to missing recalculation. |
AST-128323 | Retrieving SCA results intermittently returned zero results to the flow publisher, impacting Jira Feedback integration. |
SCA-26326 | Recalculation logic used the latest project scan instead of the latest branch scan. |
SCA-25959 | Python dependencies were not detected in certain scans. |
SCA-25442 | Scans failed when API responses exceeded the supported size limits. |
AST-143848 | Project settings rules did not allow changing the “Allow Override” option. |
AST-142454 | The logout button disappeared when the side panel was expanded and the username was too long. |
AST-141686 | The link-client |
AST-140507 | Bulk deletion of projects was not possible. |
AST-137306 | The logout button only responded when clicking directly on the text. |
AST-136066 | Contributors with the Developer role were not counted when using the new GitHub App integration. |
AST-142281 | GitHub PR decoration displayed an incorrect number of new issues. |
AST-141889 | The AWS ECR integration documentation contained errors. |
AST-139870 | The OSS Realtime Scanner did not return vulnerabilities for |
AST-137651 | A shutdown hook was unexpectedly triggered on the EU2 cluster for the |
AST-134386 | DAST PDF and JSON reports displayed incorrect vulnerability counts. |
SCA-26532 | The |
Item | Description |
|---|---|
AST-146204 | Updated deprecated Bitbucket API (api.bitbucket.org/2.0/workspaces) to the supported /user/workspaces endpoint. |
AST-143848 | Fixed issue where “Allow Override” could not be modified in Project Settings rules. |
AST-142284 | Resolved incorrect file path formatting (extra \) in GitLab scan result decorations. |
AST-141885 | Fixed GitLab repository retrieval failure caused by use of the search_namespaces attribute. |
AST-136441 | Addressed scan failures related to “Remote backend is unreachable.” |
AST-145285 | Fixed UI issue in the Jira Feedback configuration page. |
AST-141684 | Resolved SAST result viewer filtering crash for long input strings (504 Gateway Timeout). |
AST-132371 | Fixed DAST YAML configuration upload returning a 500 error without a clear message. |