GitHub Cloud
This article explains how to configure a GitHub integration using OAuth authentication. An alternative method for configuring the integration using a GitHub App will be available soon, see documentation.
This flow uses pre-configured settings that enable you to authenticate with GitHub cloud using your login credentials. This flow is available for multi tenant Checkmarx accounts using GitHub Cloud or GitHub Enterprise Cloud. We offer an alternative Self Hosted flow that involves submitting an OAuth Client ID and Secret. The Self-Hosted flow must be used for:
Checkmarx One single tenant accounts
Repos hosted on GitHub Server or GitHub Enterprise Server
Organizations that prefer to use a Client ID and Secret
Setting up the Integration and Initiating a Scan
To integrate your GitHub organization with Checkmarx One, perform the following:
In the
 home page, click on New > New Project - Code Repository Integration.
home page, click on New > New Project - Code Repository Integration.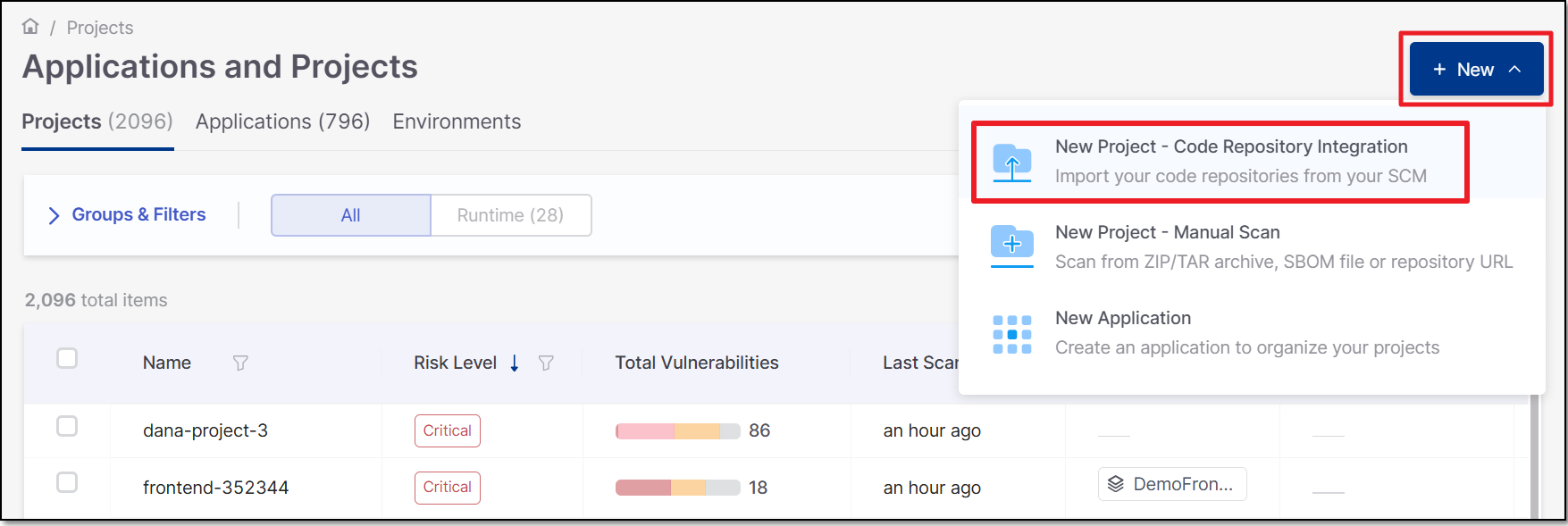
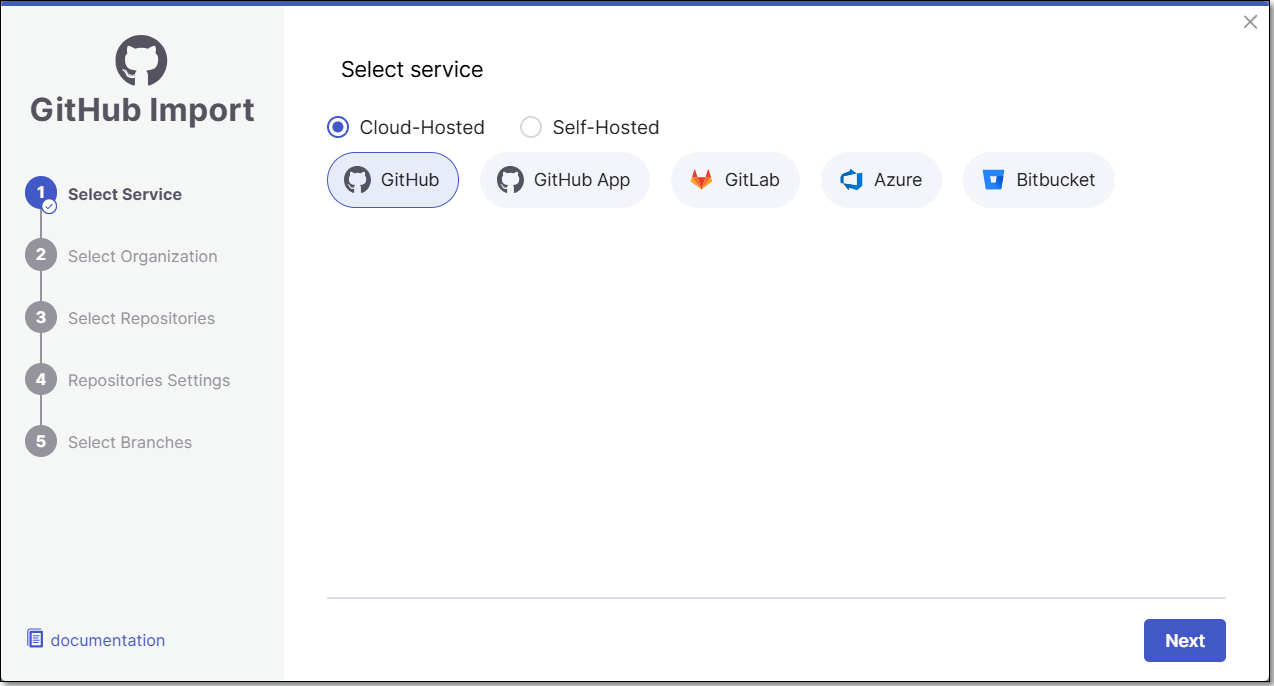
The Import From window opens.
Select Cloud-hosted >GitHub >Next.
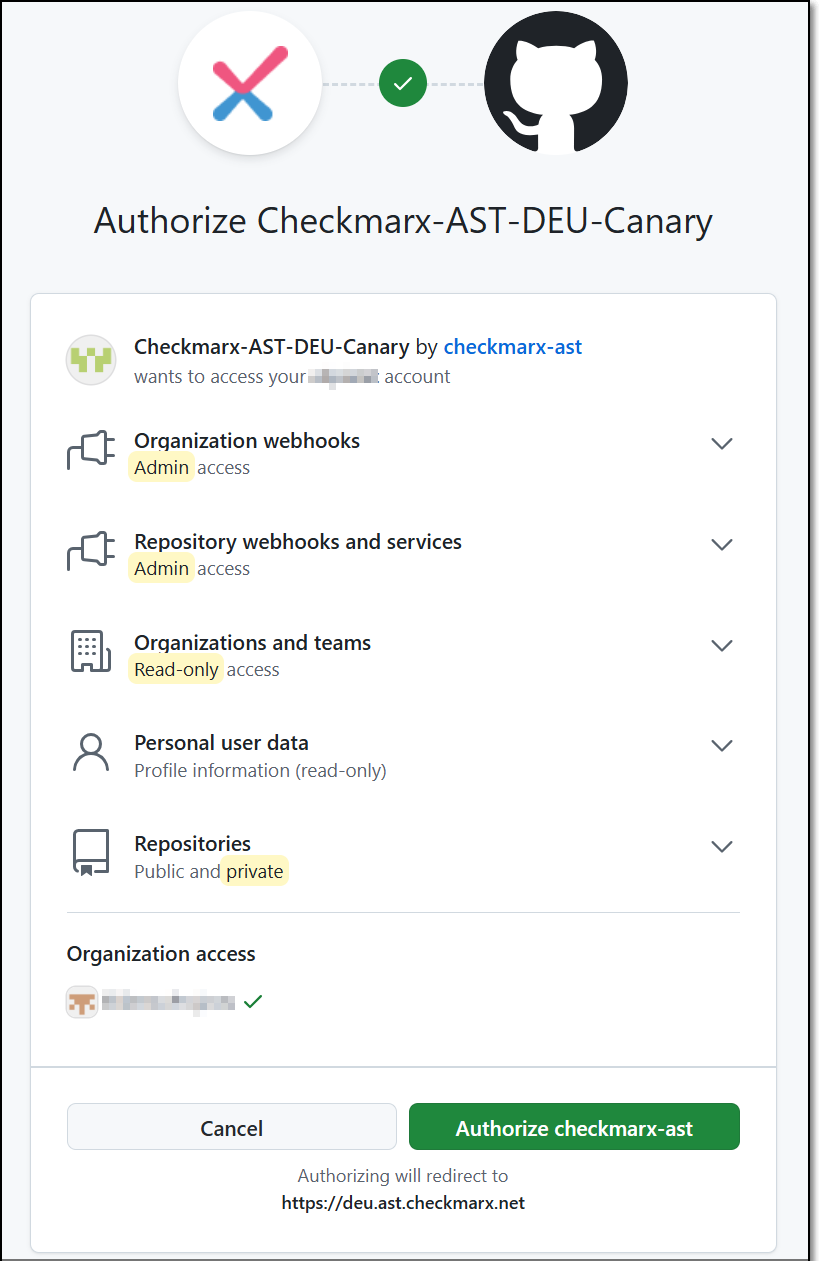
For first-time use, click Authorize checkmarx-ast
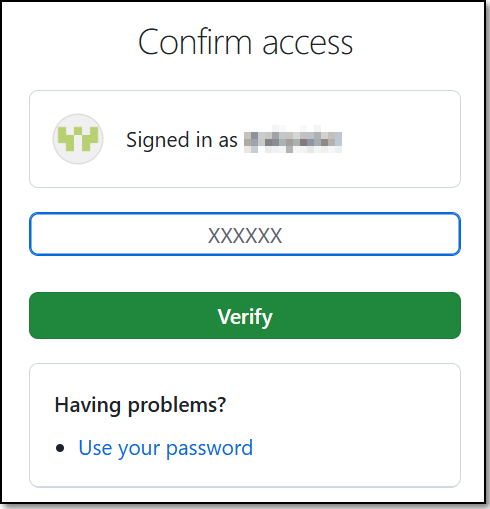
Enter your authentication code to confirm access, and then click Verify.
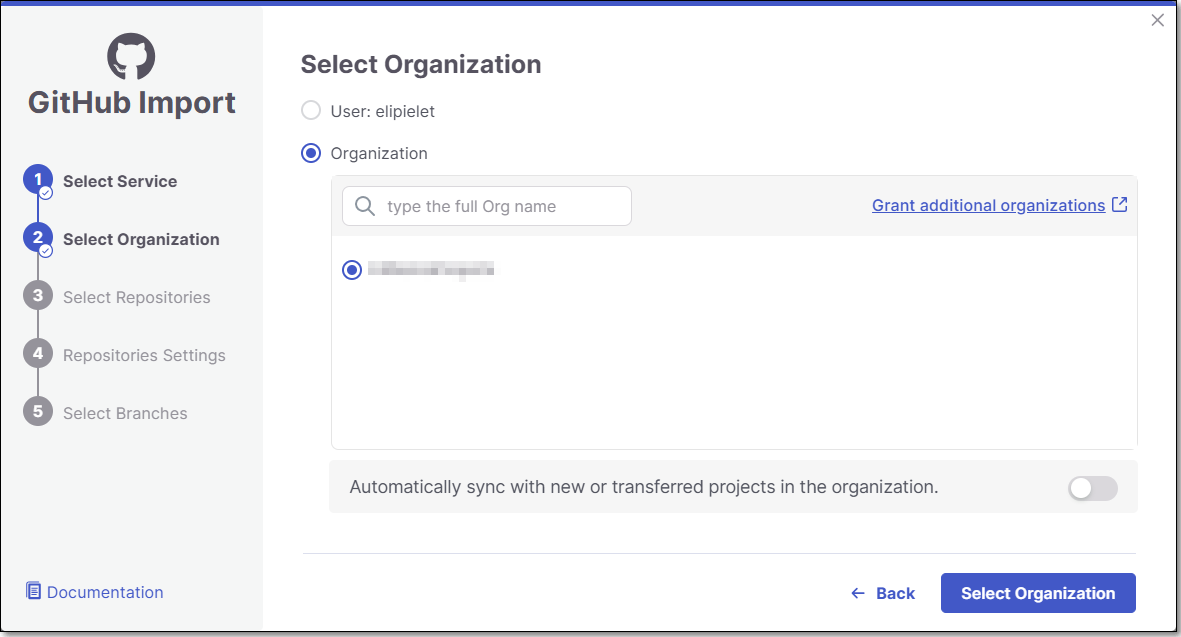
Select the GitHub User/Organization or Group (for the requested repository) and click Select Organization.
The screen contains the following functionalities:
Search bar - Users need to type the full organization name (GitHub limitation). The search is not case sensitive.
Infinite scroll - For enterprises with a large amount of organizations.
You can also decide whether to enable the "Monitor new repositories creation" feature.
For more information about the feature see Monitor New Repositories.
Note
In case you selected GitHub User skip step 5.
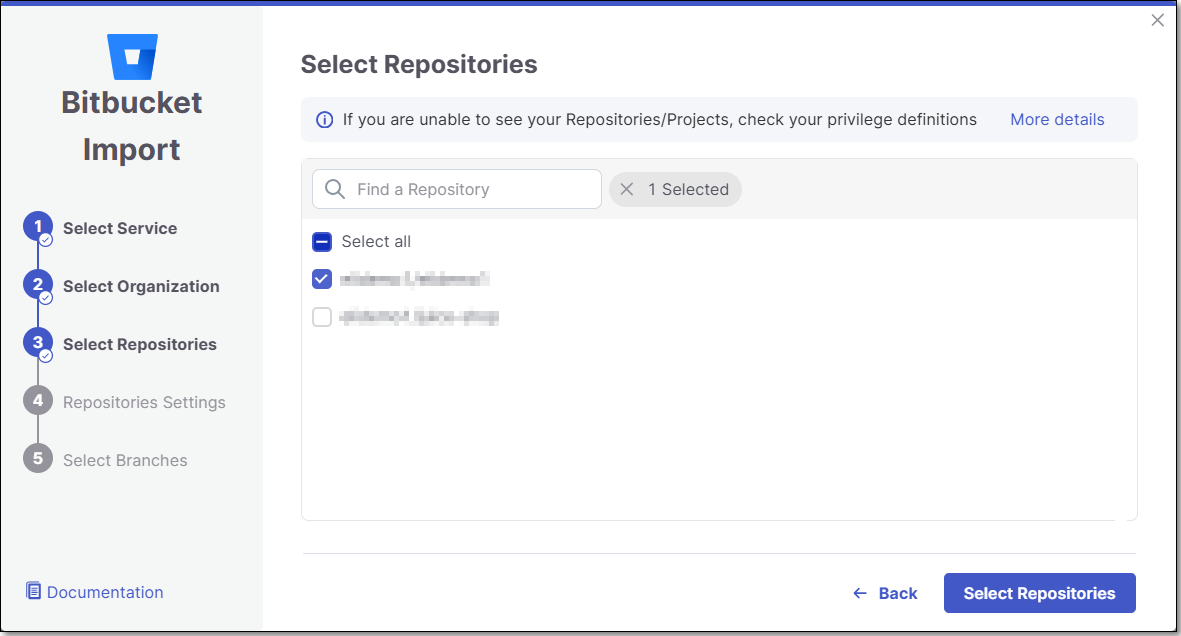
Select Repositories inside the GitHub organization and click Select Repositories.
If the organization contains active repositories, suggested repos will be presented and selected automatically. For additional information see Suggested Repositories.
Note
A separate Checkmarx One Project will be created for each repo that you import.
There can’t be more than one Checkmarx One Project per repo. Therefore, once a Project has been created for a repo, that repo is greyed out in the Import dialog.
In the Repositories Settings step, you can optionally adjust the settings as follows:
If the project has multiple repositories, click All Repositories Settings to adjust the settings for all repositories, or select a specific repository, to adjust the settings for that repository.
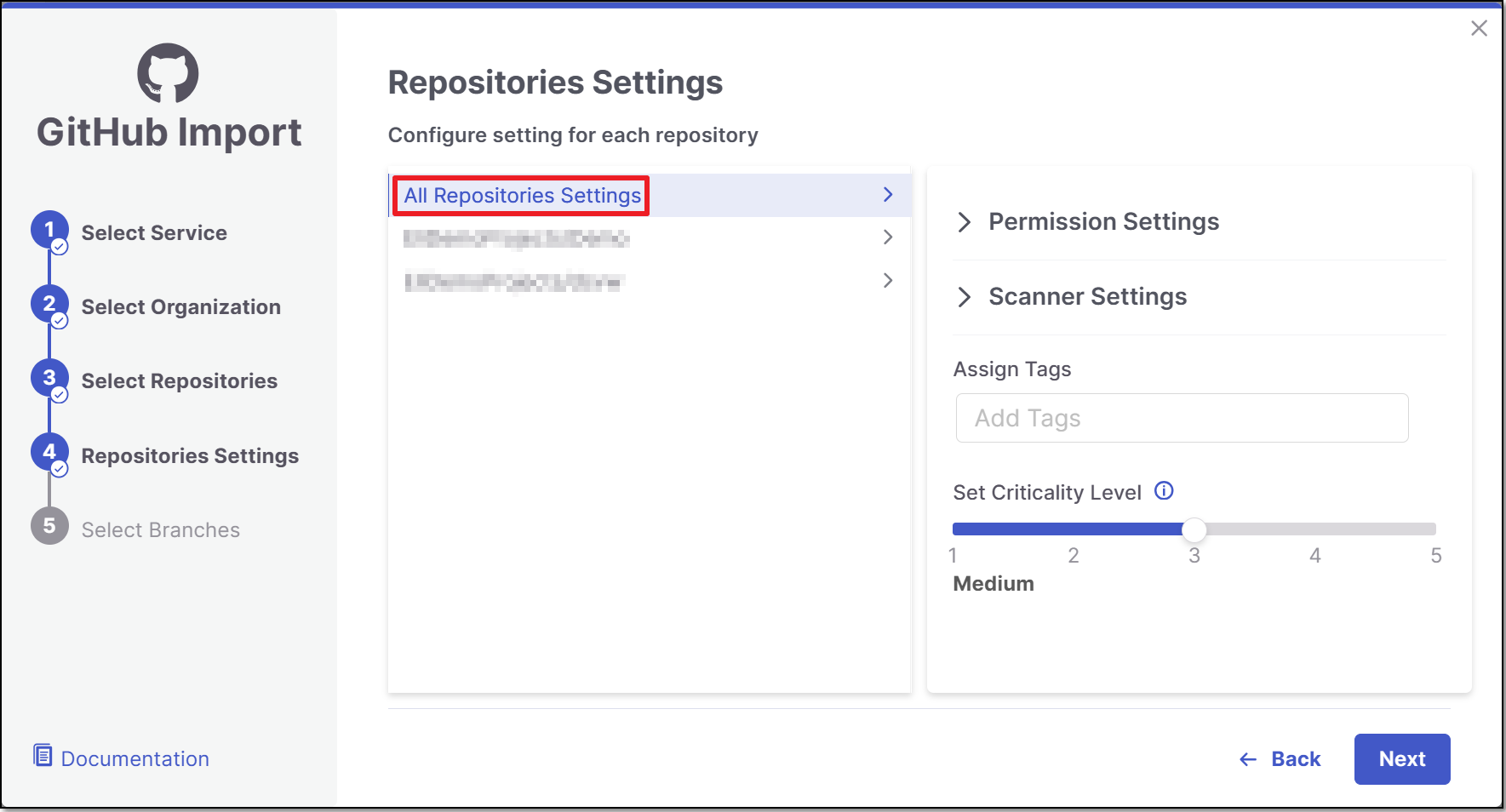
Expand the Permissions Settings and adjust the following settings:
Scan Trigger: Push, Pull request - Automatically trigger a scan when a push event or pull request is done in your SCM. (Default: On)
Pull Request Decoration - Automatically send the scan results summary to the SCM. (Default: On)
SCA Auto Pull Request - Automatically send PRs to your SCM with recommended changes in the manifest file, in order to replace the vulnerable package versions. (Default: Off)
Expand the Scanner Settings and enable the toggle for each scanner you want to use (SAST, SCA, IaC Security, Container Security, API Security, OSSF Scorecard, Secret Detection) for your repositories. At least 1 scanner must be selected for each repository.
Protected Branches (when a specific repository is selected): Specify the branches to be designated as "Protected Branches".
Notice
Specifying a branch as a Protected Branch affects three main areas: scan triggering (for PR and push), policy violation detection, and Feedback App notifications.
You can also use a wildcard symbol "*" to designate which branches are protected. The wildcard can be used before the string, after the string, or both. All branches that match the wildcard pattern will be treated as protected branches.
Notice
Examples:
*→ all branchesrelease*→ branches that begin with "release"*release→ branches that end with "release"* release *→ branches that contain "release" anywhere in the name
Tags - For each protected branch, you can optionally assign Tags. When a scan is triggered for this branch (e.g., push or pull request), these tags will automatically be applied to the scan.
Tags can be key:value pairs or simple values. For example,
env:prodorsecurity.
Add SSH key (when a specific repository is selected).
Assign Tags: Add Tags to the Project. Tags can be added as a simple strings or as key:value pairs.
Set Criticality Level: Manually set the project's criticality level.
Click Next.
In the Select Branches screen you can decide whether to enable the "Scan the default Branch upon the creation of the project" feature.
For each repository, select the protected branches you want to scan during project creation, and then click Create Project.
Tip
If you specified a wildcard pattern in the previous step, it will not appear as an option on this list.
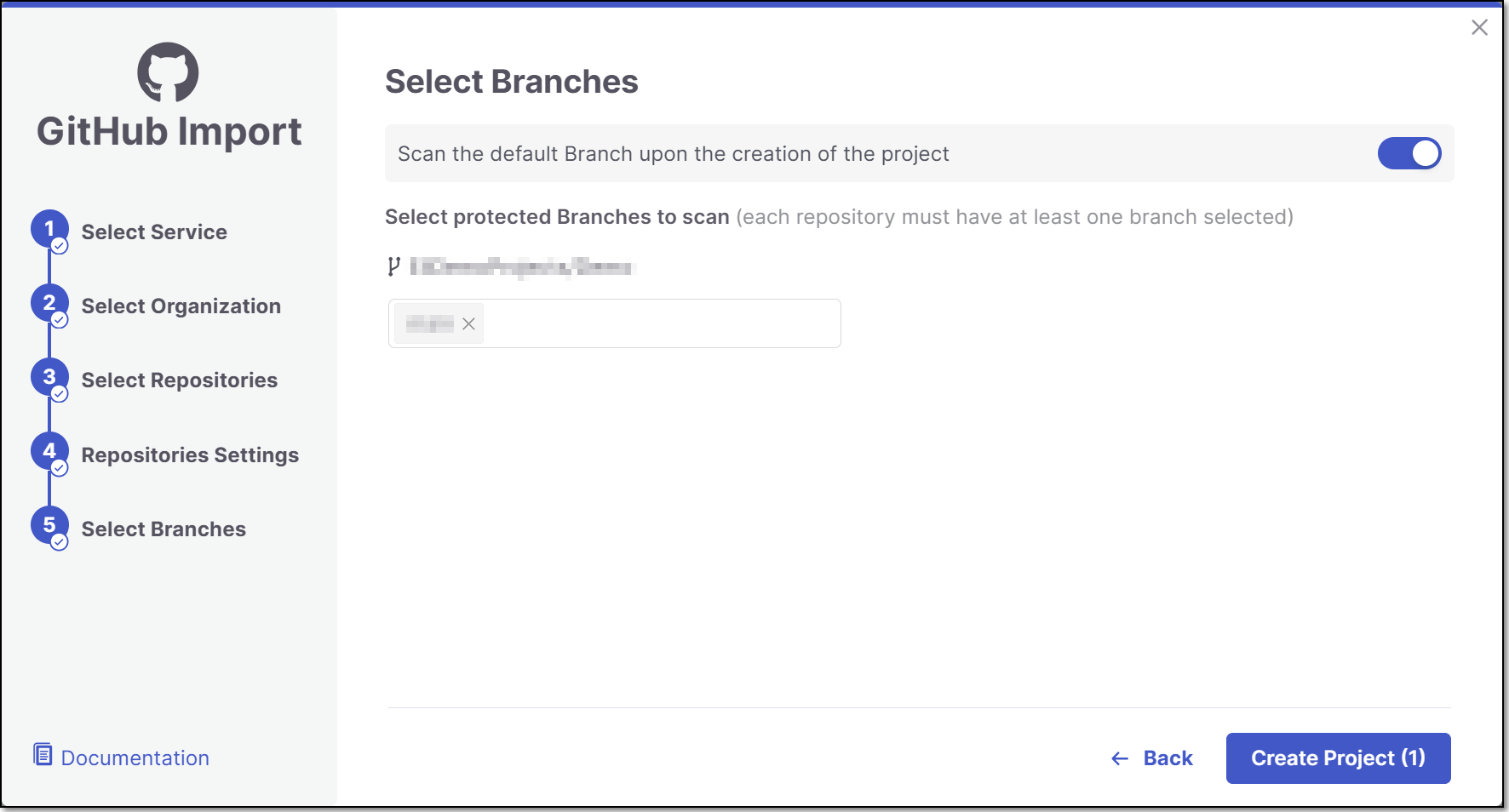
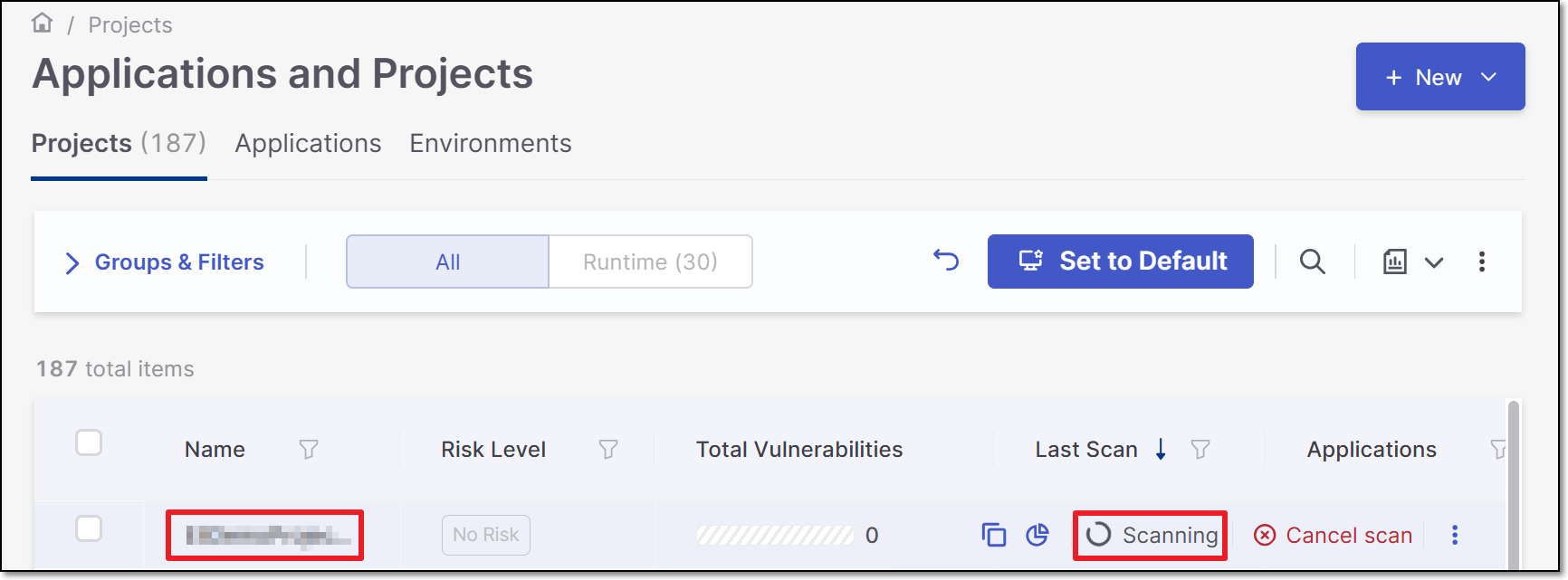
A Project is created for each repository and a scan is initiated for each project. The new projects are displayed on the Projects page,
Note
In order to update the scanners see Imported Project Settings
Note
If a GitHub organization is renamed or moved, the existing connection becomes invalid. In such cases, the organization must be reimported to restore the integration.