- Checkmarx Documentation
- Checkmarx One
- Checkmarx One Scanners
- SCA Scanner
- SCA Results Viewer
SCA Results Viewer
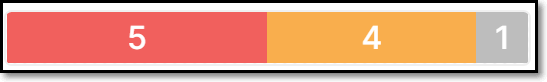
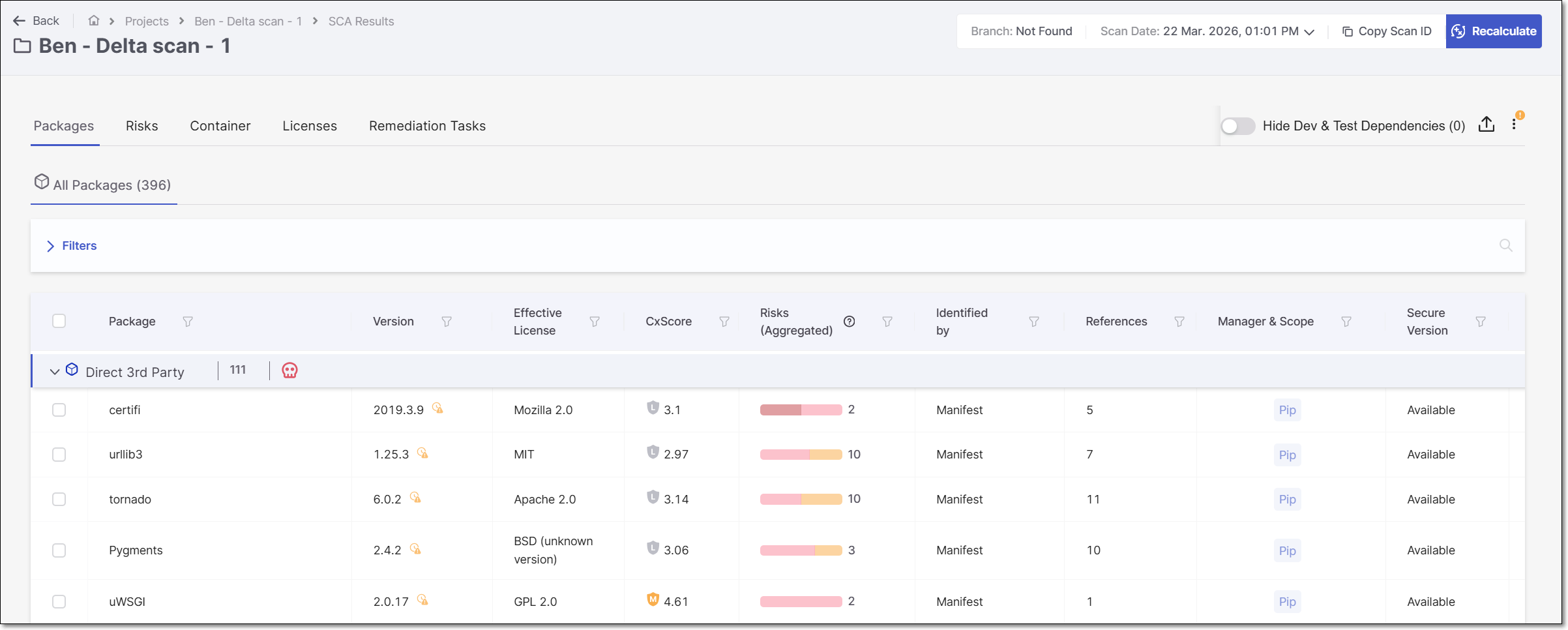
The SCA Results page displays the SCA results for the most recent scan of your Project. This includes a list of all 3rd party packages identified in your Project, as well as the specific risks associated with those packages, such as vulnerabilities, legal risks, and outdated versions.
 |
To access the SCA Results Viewer, navigate to the Projects page, hover over the  icon in the desired project's row, and click on SCA results in the window that appears.
icon in the desired project's row, and click on SCA results in the window that appears.
This screen includes a Header bar with general information about the Project and scan. It also shows detailed scan results, divided into the following tabs:
Packages – shows info about the packages used by your project and the risks that are associated with those packages, including: security vulnerabilities, license violations, and outdated versions. This tab includes two types of pages:
All Packages – shows a list of all packages that were identified by this scan
Package Details – shows detailed info about the risks associated with a specific package.
Tip
If a package needs recalculation (e.g., the Package was snoozed or muted), a red dot indicator will be displayed on the Packages tab.
Risks – shows info about all of the security vulnerabilities that were identified in the open source packages used by your project, including: severity level, CVE references, remediation recommendations etc. This tab includes two types of pages:
All Risks– shows a list of all vulnerabilities identified in your open source dependencies.
Risk Details – shows detailed info about a specific vulnerability.
Container (for projects with container images) – shows info about packages identified in your container images as well as the vulnerabilities associated with those packages.
Warning
This tab, which is part of SCA results viewer, is only in use for accounts that are still using the original Container scanner. For accounts that use the new Container Security scanner, the results are shown in the separate Container Security Results Viewer.
Container Packages – shows a list of all of the packages identified in the container images.
Container Vulnerabilities – shows a list of all of the vulnerabilities associated with the container packages.
Licenses - shows info about all of the licenses that are associated with the open source packages used by your project.
All Licenses – shows a list of all licenses associated with the open source packages identified in this scan.
License Details – shows detailed info about a specific license. Click on a row in the All Licenses tab to access this page.
Remediation Tasks - shows info about specific remediation tasks that Checkmarx recommends implementing for your Project.
All Remediation Tasks – shows a list of remediation tasks that are recommended for this Project.
Task Details – shows detailed info about a specific task. Click on the How to fix button in a task row in the All Remediation Tasks sub-tab.
Header Bar
The header bar shows general info about the Project and the scan that is currently displayed on the page.
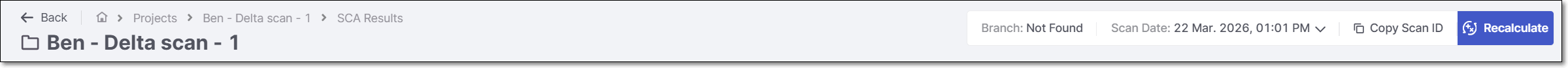
The following tables describe the information displayed in the Header bar and the available Action buttons.
Item | Description | Possible Values |
|---|---|---|
Project Name | The name of the project. | e.g., webgoat5 |
Scan Date | The date and time that the scan was run. | e.g., Feb 23, 2021 11:51 AM |
Copy Scan ID | When you hover over Scan ID, the unique identifier of the scan generated by Checkmarx SCA is shown. There is a button to copy the ID to your clipboard. | e.g., 95fc1f60-a4aa-4835-acfd-95aa315d4890 |
 (When relevant) | A warning symbol is shown when there have been issues with the scan |
Actions
Icon | Action | Description | Options | |
|---|---|---|---|---|
 | Recalculate Scan | Click to reevaluate the risks associated with the dependencies in your project. See Recalculating SCA Scan Results | ||
| Scan Report | Click on this button to download a file containing an overview of the security of your project as well as specific vulnerabilities, legal risks, and outdated versions identified by the scan. | Report sections:
File formats:
| |
Software Bill of Materials | Click on this button to download a file containing detailed info about each of the open source packages used by your program, and the associated risks. You can specify how the SBOM will be formatted, CycloneDX v1.6 or SPDX v2.3. Learn more about Checkmarx's SBOMs here. | File formats:
| ||
Remediation Manifest | Click on this button to start the process of remediating the Project’s manifest files. For more information see Export Remediated Manifest File. | N/A | ||
 | Resolving Info | Display info about the package resolution process.
| ||
Scan Details | Display details of the scan process. For each step in the scan run, the start time and duration are shown. | |||
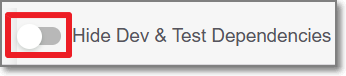 | Hide Dev Dependencies toggle | Toggle this switch on in order to hide results for dev packages. For more information, see below. |
Checkmarx SCA is able to distinguish between development dependencies and production dependencies for several package managers. On the Scan Results page, the number in parenthesis next to the Hide Dev & Test Dependencies toggle indicates the number of dev & test dependencies in the Project. Toggle the Hide Dev & Test Dependencies switch ON if you would like to hide vulnerable packages that were identified as dev and test dependencies.
Notice
This filter can also be applied to the following REST APIs: Results Summary and All Scanners Results.
Identifying Dev Dependencies
The following table shows how dev dependencies are identified for specific package managers.
Package Manager | Dev Dependency Specification |
|---|---|
NPM | In the manifest file (package.json or bower.json), using the devDependencies attribute. For example, "devDependencies" : {
"my_test_framework": "^3.1.0".
"another_dev_dep": "1.0.0 - 1.2.0"
} |
Yarn | |
Bower | |
Composer | Packages under the require-dev section in the composer.json file. |
Identifying Test Dependencies
Any package with the word "test" in the file path is identified as a test dependency.
Remediation using a Manifest File
Note
This remediation method is effective only for remediating risks in direct dependencies. An alternative method (currently in BETA and supported only for npm) addresses remediation of transitive dependencies as well. The alternative method is accessed from the Remediation Tasks tab on the SCA Scan Results Viewer page, as described in Remediation Tasks Tab.
Remediation is generally done by exporting the remediated file and manually replacing the manifest file in your project. However, if your project is hosted in a private GitHub repository, you can remediate your project directly from the UI by sending a pull request. If you have the required permissions, you can then merge the pull request into your project.
To remediate your project, do the following:
Go to the SCA Scan Results Viewer page for the scan of the Project that you would like to remediate.
Hover over the Export
 icon at the top right corner of the page and click on Remediation Manifest.
icon at the top right corner of the page and click on Remediation Manifest.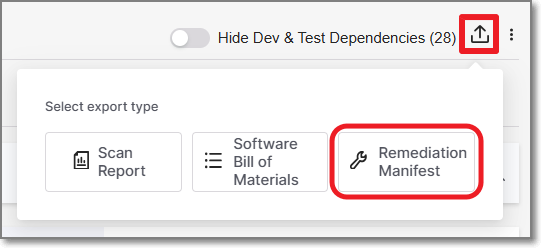
The Remediate manifest message appears, displaying a list of all the manifest files that can be remediated. A checkbox is displayed next to each file in the list.
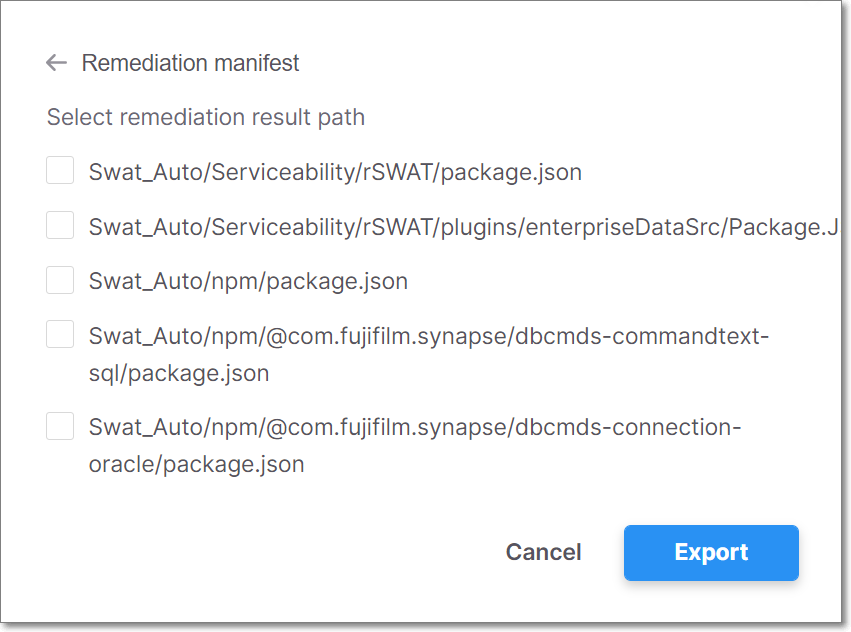
Notice
For a project in a private GitHub repository, an Open Pull Request button is displayed next to the download icon.
Notice
If a manifest file cannot be remediated, for example it already contains the latest packages or the latest packages have still not been fixed for the known vulnerabilities, the manifest file will not be displayed.
Select the checkbox for each manifest file that you would like to remediate.
If you want to remediate your project manually, select the checkbox and click Export to download the remediated manifest file and use it to update your project.
If you want to remediate your project directly in GitHub, use the following procedure.
Click Open Pull Request next to the package manager file that you require. A pull request is sent to your project’s GitHub repository. The Open Pull Request button is replaced with a View Pull Request button.
To view the pull request, click View Pull Request. GitHub opens to your project, displaying CxSCA-Remediation. Under Packages updated by CxSCA-Remediation, there is a list of the remediated open source packages, the updated version numbers, and the fixed vulnerabilities.
You can merge the remediated open source packages into your project by clicking Merge pull request, displayed in GitHub. The next scan of your project should show fewer (or no) vulnerabilities.
Packages Tab
The Packages tab shows detailed info about the packages that were identified in your source code and the vulnerabilities that they contain.
The Packages tab contains sub-tabs that show two types of pages:
All Packages – shows a list of all packages that contain vulnerabilities that were identified by this scan.
Package Details – shows detailed info about a specific package. Click on a row in the All Packages sub-tab to access this page.
Notice
Alternatively, you can access this page by clicking on a package in the Global Inventory & Risks > Packages page.
You can navigate between the various tabs that you have opened.
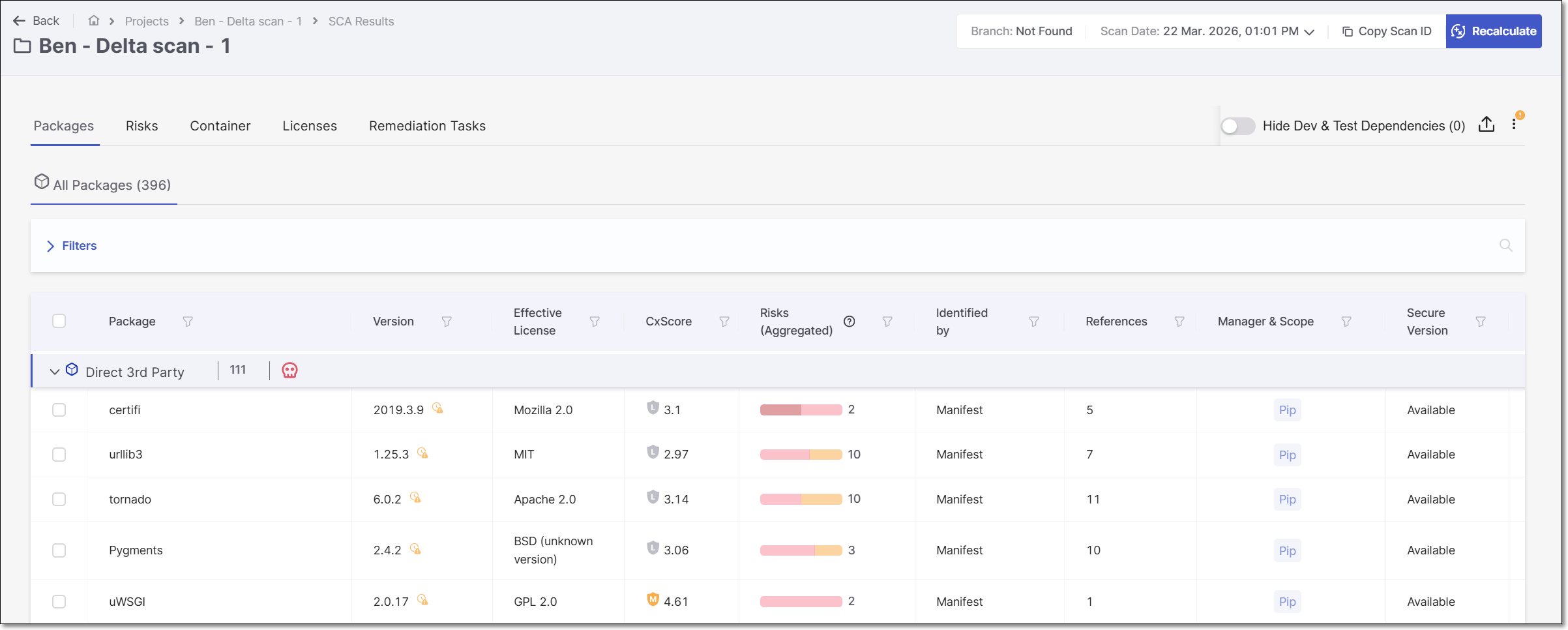
All Packages Page
The All Packages sub-tab shows separate tabs for the different types of packages (Direct 3rd Party Packages, Transitive 3rd Party Packages, Private Packages and Saas Providers). Each tab shows the overall number of packages of this type as well as the number of policy violations for that category.
Notice
For a package that is referenced both directly and transitively, the total number of packages shown at the top of the All Packages tab counts that package only once. Therefore, the total number of packages may be fewer than the total of the Direct packages plus the number of Transitive packages.
Clicking on a category heading expands that section, to show a list of packages of that type that were identified by this scan of your Project. For each package, info is shown about the risks related to that package. You can search for specific packages using the search box.
You can also sort by column headers and set filters for each column.
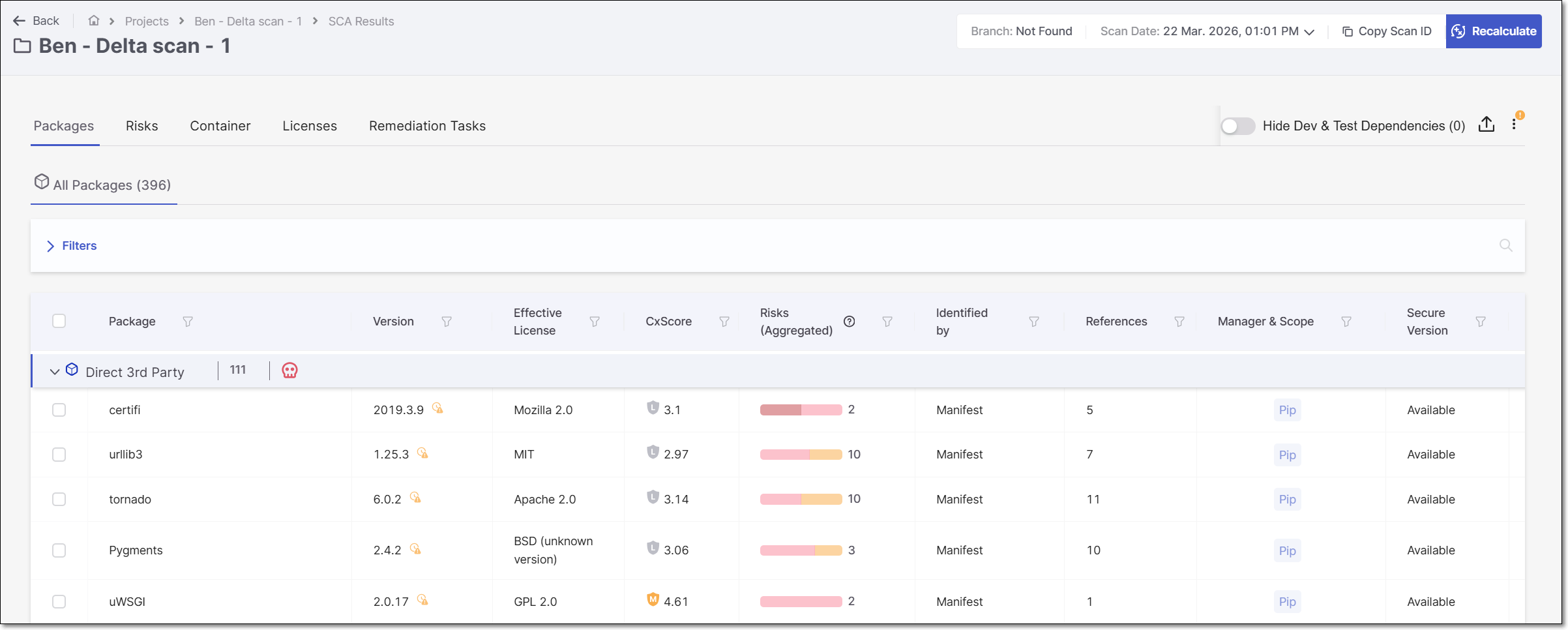
The following table describes the info shown for each package identified by this scan.
Item | Description | Possible Values | |
|---|---|---|---|
Package | The name of the package. This column also shows the Clicking on the icon takes you to that item in the Remediation Tasks Tab . | e.g., dom4j:dom4j | |
Version | The version of the package that you are using. This column also shows the Hover over the icon to view addition info about the more recent versions. | e.g., 1.6.1 | |
Effective License | Shows the Licenses that are associated with the package. For multiple licenses, hover over the display to show all licenses and the associated legal risks. | e.g., GPL 2.0, Apache2.1 | |
CxScore | A composite risk metric that combines vulnerability severity with real-world exploitability to prioritize remediation. For more information, see CxScore. |
| |
Risks (Aggregated) | A color coded bar graph indicating the number of vulnerabilities of each severity level. Hover over the bar to view a breakdown of the results by Vulnerability, Legal Risk and Suspected Malware. For malicious packages the TipYou can apply complex filters to show only packages that contain risks of a specific type and of a specific severity. You can also apply filters to show only packages of a specific state (e.g. Monitored, Muted or Snoozed). TipThe color coded bar graph is shown for Monitored packages only. If a Package is muted or snoozed, the respective icon will be placed instead of the bar. | e.g.,
| |
Identified By | Indicates how the package was identified. |
| |
References | Shows the number of paths that reference this package. TipPackages that are referenced both directly and transitively, are included in the Direct 3rd Party section and the number of direct (D) and transitive (T) paths are given. | e.g., 1D, 12T | |
Dependency | Shows labels that Checkmarx applied to the package. There is a label indicating the package manager used for package resolution. Additional labels are applied to special types of dependencies. |
| |
Secure Version | Indicates whether or not a remediated version (i.e, a version with no vulnerabilities) of this package exists. |
| |
AppSec Knowledge Center | Link to the AppSec Knowledge Center page for each package. | |
Package Details Page

The Package Details sub-tab shows detailed info about a specific package. The top info pane gives general info about the package, and the separate cards below it show detailed info about various aspects of the risks posed by the package. If the package requires recalculation (e.g., the package was snoozed or muted), a red dot indicator will be shown on the sub-tab.
Info Pane
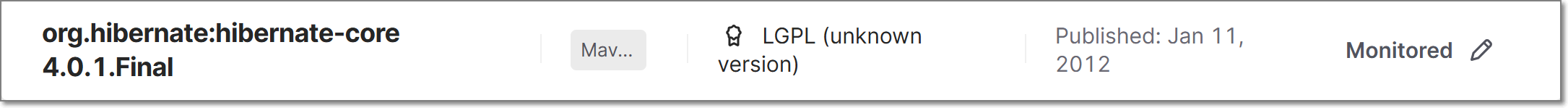
Item | Description | |
|---|---|---|
Package | The name and version of the package. | |
Remediation Task
| A link to the recommended remediation task in the Remediation Tasks tab. (Only shown when available) | |
Dependency Type | The type of package manager used for this package. | |
License(s) | Shows all licenses that you have that are associated with this package. | |
Published | The date that this version of the package was published. | |
State | The state of the package. Clicking on the state opens a side panel with a drop down list to choose the state from. WarningChanges in package state are a serious matter; Saving changes can only be implemented with a comment explaining your consideration. Options are:
The side panel includes a History tab where you can view a log of previous state changes and comments. |
Package Details Sections
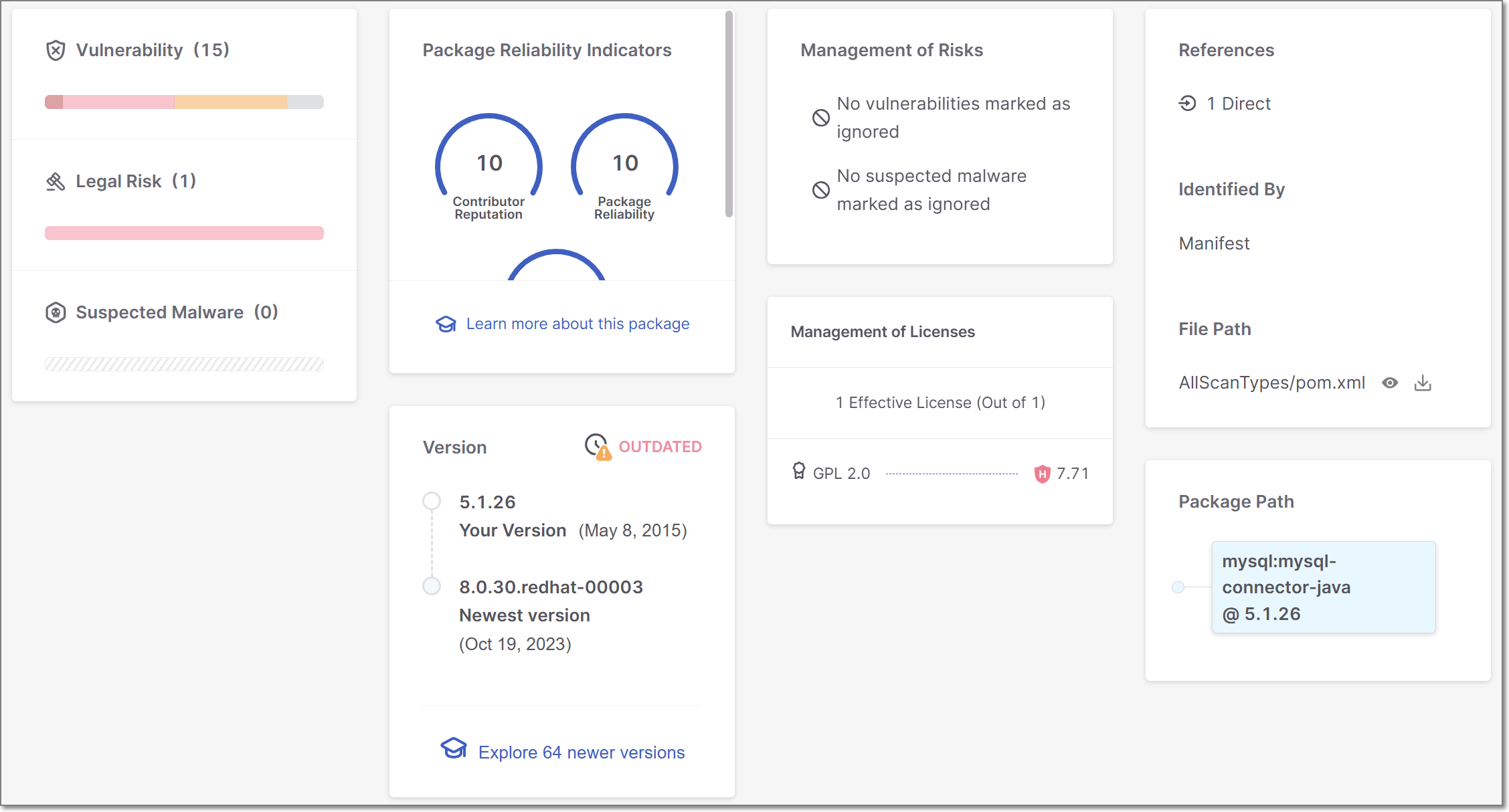
Item | Description |
|---|---|
Watch Out! (for malicious packages) | This warning card will be displayed if this version of the package is known to be malicious. |
Vulnerability | The total number of vulnerabilities in this package, followed by a color coded bar graph indicating the number of vulnerabilities of each severity level. |
Legal Risk | The total number of Legal Risks in this package, followed by a color coded bar graph indicating the number of Legal Risks of each severity level. |
Suspected Malware | The total number of Suspected Malware risks affecting this package, followed by a color coded bar graph indicating the number of Suspected Malware risks of each severity level. |
Package Reliability Indicators | Shows gauge widgets representing three risk categories (Reputation, Reliability and Behavior). The scores are given on a scale of 0-10, with 10 indicating the highest level of security. |
Version | Shows the version you are using, the newest version, the number of newer versions released since you last updated and an overall assessment of whether there is a need to update your version. |
Learn More About This Package | Shows a link to the AppSec Knowledge Center for more information about this package. |
Management of Risks | Shows if any vulnerabilities and Suspected Malware risks have been marked as ignored. |
Management of Licenses | Shows the number of Licenses that have been marked as Effective Licenses. In addition, a link is given to view detailed information about this license in the risk details tab. |
References | Shows the number of manifest files that refer to this package and indicates whether it is a direct or transitive dependency. |
Identified By | Indicates how the vulnerable package was identified. Possible values are:
|
File Path | The file path to the manifest file where this package was identified is shown. Click on the icons to view or download the file. |
Package Path | The selected package is displayed in blue. If this is a transitive dependency (i.e., it is accessed via other packages), then the full path by which the package is accessed is shown above it. You can click on any package shown in the path in order to open a new tab showing details for that package. If there are multiple paths to this package, then you can click on the forward and back arrows at the bottom of the pane to view each of the paths. TipFor packages that were identified by binaries (and not by a manifest file), no data is shown for the package path. TipFrequently you can fix the vulnerabilities by updating the transitive packages with their latest versions. |
Package Usage (for projects with Exploitable Path activated) | Shows the places in your code where the vulnerable package is called. Results are grouped by file path. Expand an item to see the line number and node of each place where the package is called. |
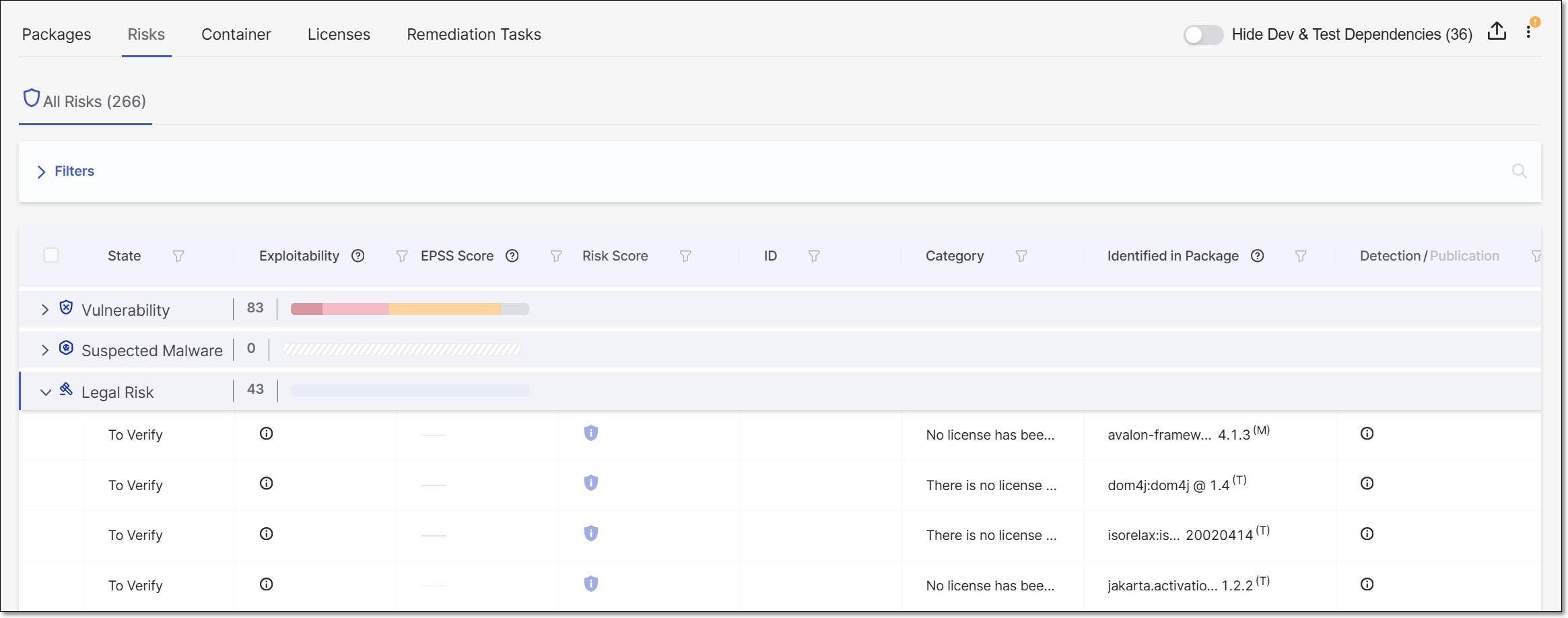
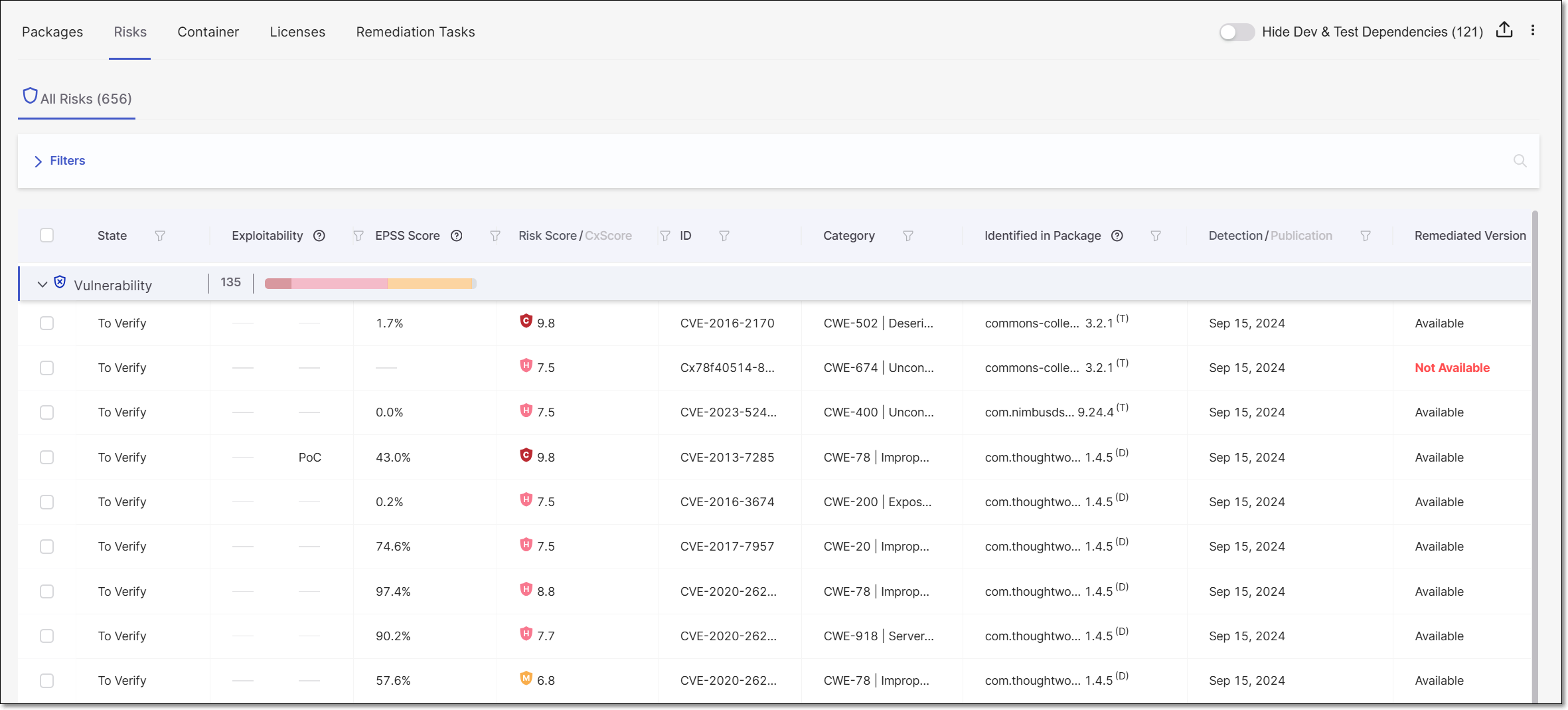
Risks Tab
The Risks tab shows info about all of the Risks that are associated with the open source packages used by your project. This includes vulnerabilities (e.g., CVEs), as well as suspected malware (e.g., malicious packages), legal risks and outdated packages.
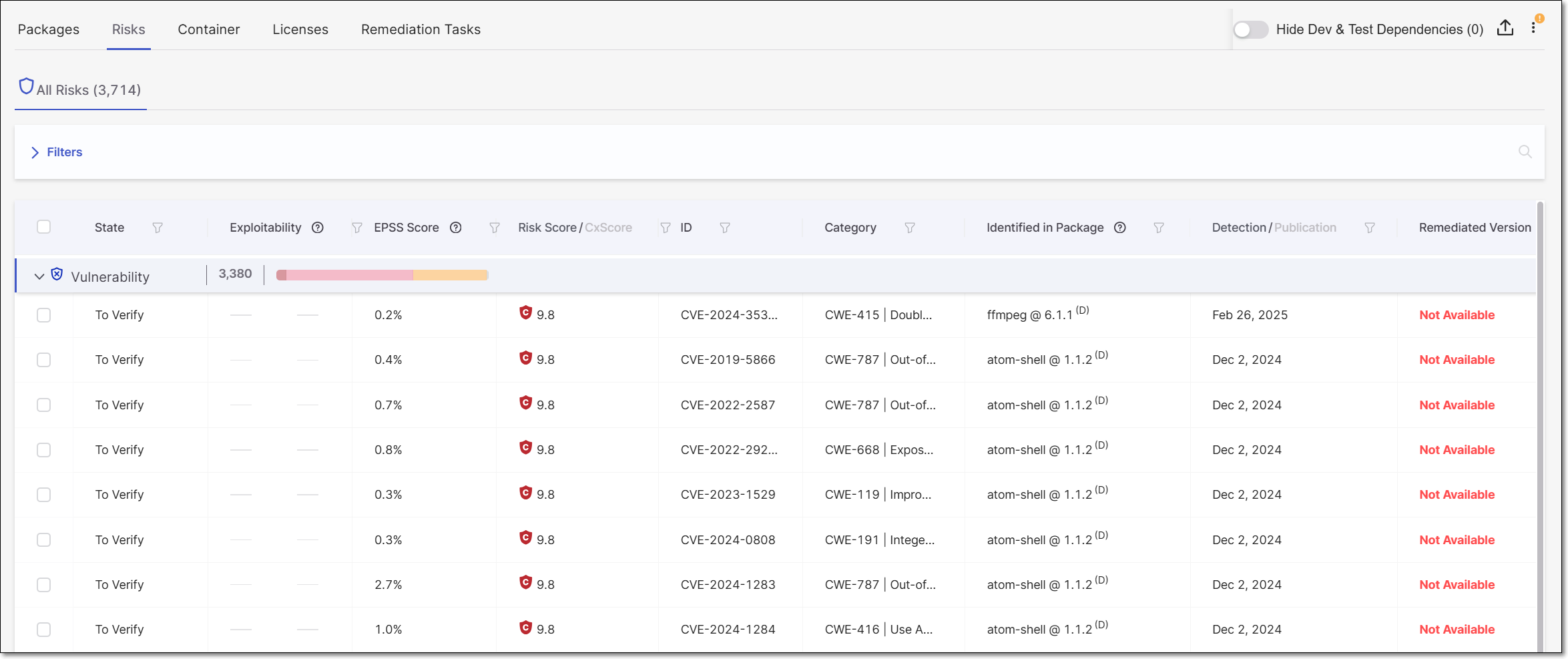 |
The Risks tab contains sub-tabs that show two types of pages:
All Risks – shows a list of all Risks identified by this scan. This tab is accessed by clicking on the Show All button on the Project page and then selecting the Risks tab. The results on the All Risks tabs are divided into the following tabs:
Vulnerability - shows a list of vulnerabilities in your open source packages that can be exploited by an attacker. This includes vulnerabilities that have been published as CVEs as well as vulnerabilities identified by the Checkmarx Vulnerability Research Team (i.e., Cx). The summary graph shows the total number of vulnerabilities and a breakdown by severity level.
Suspected Malware - shows various types of suspected malware risks that affect the packages in your project, such as packages that are Malicious by design and packages that are vulnerable to ChainJacking attacks etc. The summary graph shows the total number of suspected malware risks and a breakdown by severity level.
Legal Risk - shows all of the Legal Risks relating to the licensing of the packages used in your project. The summary graph shows the total number of legal risks and a breakdown by severity level. Learn more about Legal Risks in the section below.
Outdated - shows a list of all packages that have vulnerabilities or suspected malware risks, for which a more recent package version is available. The summary graph shows the total number of vulnerable outdated packages as well as a breakdown by severity level (i.e., highest severity vulnerability in the package).
Risk Details – shows detailed info about a specific Risk. Click on a row in the All Risks tab to access this page.
Notice
Alternatively, you can access this page by clicking on a Risk in the Global Inventory & Risks > Risks page.
Notice
Clicking on a Legal Risk opens the Licenses tab filtered for the relevant license.
The packages listed in the Outdated section aren’t clickable and don’t have a Risk Details page associated with them.
You can navigate between the various tabs that you have opened.
Legal Risks
Overview
Checkmarx identifies all of the licenses associated with the open source packages used in your project. The complete list of licenses is shown in the Scan Results > Licenses tab.
Notice
The License Score represents the level of risk associated with using a package under that license. However, the license doesn't pose an actual risk to your project unless you are actually using the package under that license (i.e., it is your Effective license).
In addition, Checkmarx identifies actual risks to your project based on legal issues related to improper usage of open source packages. These risks are shown in the Scan Results > Risks tab in the Legal Risk section.
Marking Licenses as Effective or Not Effective
Packages often have several different licenses associated with them. This gives users the option to choose which license to consider "effective" for that package, i.e., which set of license restrictions they would like to follow. As long as you are abiding by the terms of the effective license, the other licenses don't constitute a legal risk.
Initially, the state of most licenses is set as To Verify. However, when there is a sole license for a package and it was identified in a reliable source, that license is automatically marked as Effective. You can then review the licenses and mark each license as Effective or Not Effective based on your assessment of the package usage. Changing the state of a license is done via the Checkmarx One web application, on the Risk Details page.
Whether or not a license is marked as Effective impacts on the determination of whether it constitutes a Legal Risk, as described in the following section.
Types of Legal Risks
We currently identify the following types of legal risks.
Risky effective license - A license has a high severity License Score and is also marked as Effective for this package.
Package with no effective license - There is an open source package in your project for which no license has been marked as Effective.
Package with no license - Checkmarx didn't identify any licenses associated with this package.
Recommended Workflow
The following E2E workflow explains how you can leverage the legal risk functionality provided by Checkmarx to get results that accurately reflect the security posture of your project from a legal perspective.
Create a project and run a scan.
Go to the Risks tab > Legal Risks and check for packages with no license associated.
If you aware of the relevant licenses for these packages, add them via API, using POST /management-of-risk/package-licenses.
Go to the Scan Results > Licenses tab. Review each license and mark whether or not it is the Effective license for the specified package (via the web application).
On the Scan Results page, click on
 > Recalculate Last Scan.
> Recalculate Last Scan.After the recalculation is complete, go to the Risks tab > Legal Risks and check what Legal Risks were identified in your project.
Take the required steps to remediate these risks.
All Risks Page
The All Risks sub-tab shows separate tabs for the different types of Risks (Vulnerability, Suspected Malware, Legal Risk and Outdated). Each tab shows the overall number of Risks for this type and the number of Risks for each risk level. Clicking on the arrow on the left of the tab expands a list below it to show all Risks of this type identified by this scan of your Project. For each Risk, info is shown about the nature of the Risk. You can search for specific Risks using the search box.
Notice
If a risk affects several packages in your Project, a separate record is listed for each instance of the risk.
You can also sort by column headers and set filters for each column.
 |
Clicking on the arrow on the left of the tab expands a list showing all of the risks of that type.
Notice
Risks that have been marked as Not Exploitable are shown with a strikethrough line and they aren't counted towards the total number of risks. However, changes to the summary counters only take effect when a subsequent scan or scan recalculation is run.
The following table describes the info shown for each vulnerability identified by this scan.
Item | Description | Possible Values |
|---|---|---|
State | Indicates the state of this vulnerability for this project. | For vulnerability or suspected malware risks:
TipWhen the state is set as Not Exploitable, the risk is marked with a strikethrough line and the Risk Details page is grayed out. NoticeThe states mentioned above are pre-configured for all Checkmarx One accounts. In addition, you can create custom states in your account. Once they are created, you can assign those custom states to results. Custom states is currently supported for SAST, SCA, IaC Security and Container Security results. It is not yet available for all tenant accounts. For more info, see Custom States.
|
Exploitability | Shows which exploitability indicators apply to this vulnerability. |
|
EPSS Score | The EPSS (Exploit Prediction Scoring System) is a risk score provided by First, indicating the likelihood of a vulnerability being exploited. The score is presented as a percentage, representing the likelihood of this vulnerability to be exploited within the next 30 days. Hovering over the score will display a percentile indicating the ranking of this risk relative to other vulnerabilities. | e.g., 1.6%, 87th percentile |
Risk Score | Shows the the severity level of the vulnerability based on its CVSS score in the NVD, as well as the precise CVSS score. TipThe Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. |
For more info about SCA risk severity, see here. |
CxScore | A composite risk metric that combines vulnerability severity with real-world exploitability to prioritize remediation. For more information, see CxScore. |
|
ID | The ID of the CVE listing. The ID consists of the CVE prefix followed by the year that the CVE was discovered and the serial counter for that year's CVE listings. TipVulnerabilities discovered by the Checkmarx Vulnerability Research Team which are net cataloged as CVEs, are indicated by the “Cx” prefix. | e.g., CVE-2020-9488 |
Category | The category of the vulnerability. For CWEs, the CWE is given as well as a brief description of the vulnerability. | e.g., CWE-89|SQL Injection, Malicious, ChainJacking etc. |
Identified in Package | The name and version of the package in which the vulnerability was identified. In addition, an indication is shown for the type of dependency:
Results can be filtered by dependency type. | e.g., loadash @ 4.13.1 (T) |
Publication Date | Shows the date that this vulnerability was first officially published on a supported public Security Advisory. | e.g., Nov 16, 2020 |
Secure Version | Indicates whether or not a remediated version of the package where this vulnerability was identified exists. TipIn the context of the Risks tab, a version is considered secure as long as this particular vulnerability is remediated, even if the package has other vulnerabilities. |
|
Explore in AppSec Knowledge Center | Click on the |  |
Risk Details Page
The Risk Details sub-tab shows detailed info about a specific Risk. The top info pane gives general info about the vulnerability, and the separate cards below it show detailed info about various aspects of the risks posed by the vulnerability.
The different risk types are:
Vulnerability - a vulnerability that can be exploited by an attacker. This includes vulnerabilities that have been published as CVEs as well as vulnerabilities identified by Checkmarx AppSec experts (i.e., Cx).
Suspected Malware - shows various types of Suspected Malware risks that affect the packages in your project, such as packages that are Malicious by design and packages that are vulnerable to ChainJacking attacks.
Notice
There are no Risk Details pages associated with Legal Risks or Outdated packages. Clicking on a Legal Risk opens the Licenses tab filtered for the relevant license. Outdated packages aren’t clickable.
Each type of risk shows different cards on the details page. The different cards are described in the tables below.
Vulnerability Details
Vulnerabilities are risks that can be exploited by an attacker. This includes vulnerabilities that have been published as CVEs as well as vulnerabilities identified by the Checkmarx Vulnerability Research Team (i.e., Cx).
Info Pane
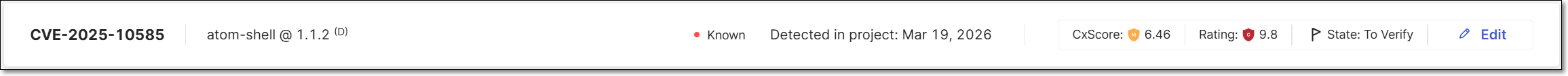 |
Item | Description | Possible Values |
|---|---|---|
ID | The ID of the CVE listing. The ID consists of the CVE prefix followed by the year that the CVE was discovered and the serial counter for that year's CVE listings. TipVulnerabilities discovered by the Checkmarx Vulnerability Research Team which are net yet catalogued as CVEs, are indicated by the “Cx” prefix. | e.g., CVE-2019-12384 |
Package | The name of the package in which the vulnerability was identified. | e.g., com.fasterxml.jackson.core:jackson-databind 2.9.8 |
Version | The version of the package where the vulnerability was identified. | e.g., 5.1.26 |
Exploitability | Shows which exploitability indicators apply to this vulnerability. |
|
Detected in Project | The date that the vulnerability was first identified in this project. | e.g., May 12, 2024 |
CxScore | A composite risk metric that combines vulnerability severity with real-world exploitability to prioritize remediation. For more information, see CxScore. |
|
Rating | Shows the severity level of the vulnerability based on its CVSS score in the NVD, as well as the precise CVSS score. |
For more info about SCA risk severity, see here. |
Risk State | This indicates the current state of the vulnerability as determined by your AppSec team. All new risks are initially marked as To Verify. A user with |
TipWhen the state is set as Not Exploitable, the page is grayed out and the risk is marked with a strikethrough line on the All Risks tab. |
Vulnerability Details Sections
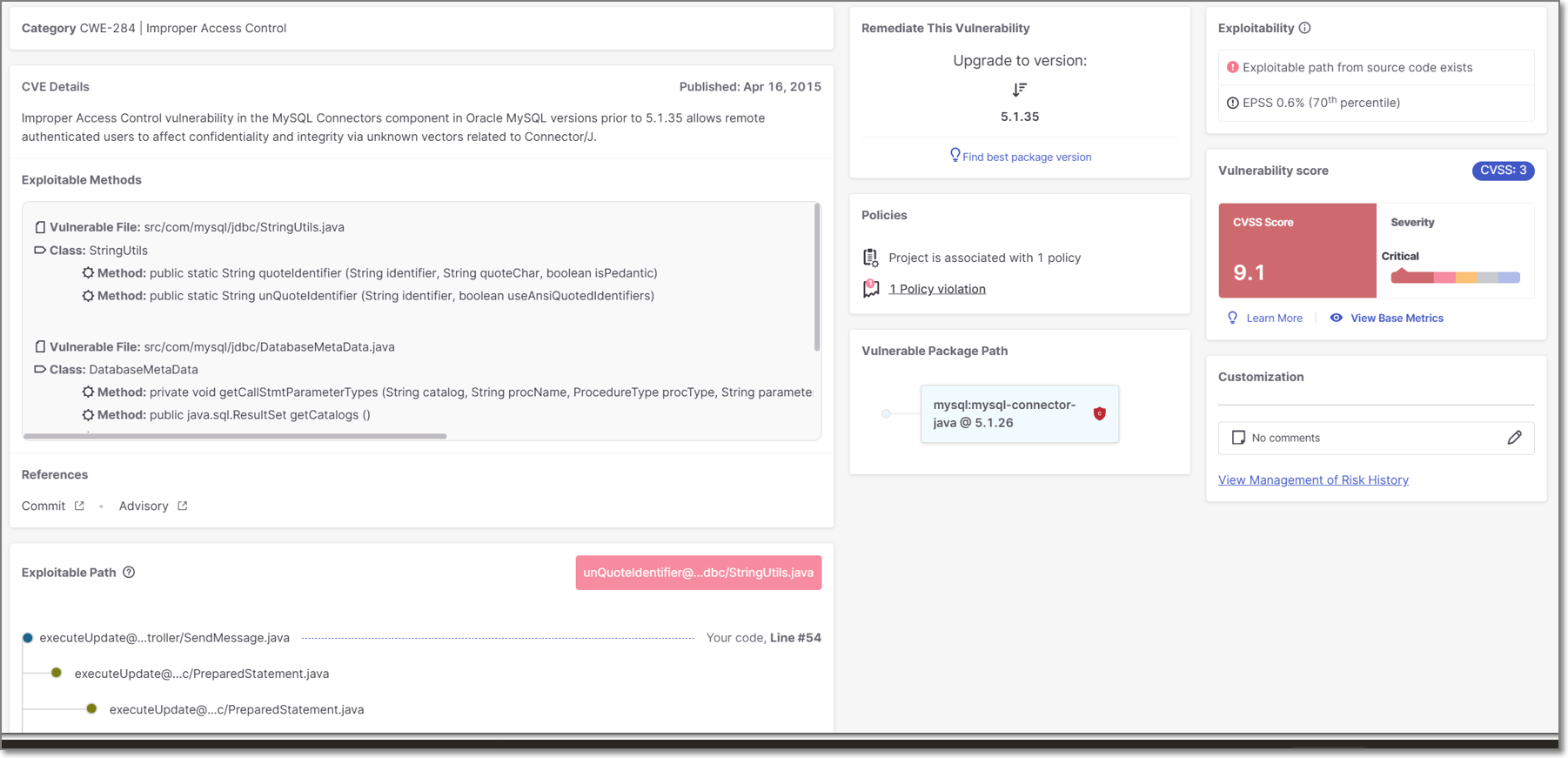 |
Item | Description |
|---|---|
Category | The ID and description of the CWE (Common Weakness Enumeration) listing. The ID consists of the CWE prefix followed by the serial counter. |
CVE Details | A description of the nature of the threat posed by the vulnerability and the date the vulnerabiliity was published in the NVD. |
Exploitable Methods | Details about the vulnerable methods that expose the vulnerability to exploitation. When the relevant details are available, we show the vulnerable file path, class, and method. This visibility increases transparency into how we evaluate exploitable paths, and provides actionable data for cases where full exploitable path analysis is not possible. |
References | Links to external resources about the vulnerability. Links are given for topics such as: Advisory, Commit, Release Notes, Issue etc. |
Exploitable Path | If a path was detected from your source code to the vulnerable method in the package, a map of the path is displayed. |
Remediate this Vulnerability | Recommended steps that should be taken to remediate this vulnerability. If available, a remediated version of the package is recommended for upgrade. Otherwise, the AI Package Finder button is shown that enables you to get AI generated suggestions for non-vulnerable replacement packages. TipThe recommended package version, is the minimum version that does not contain this particular vulnerability. To find the minimum version that doesn’t contain any vulnerabilities, click on Find best package version. |
Policies | The number of Policies the Project is assigned to and the number of Policy violations. |
Vulnerable Package Path | The vulnerable package is displayed in blue. If this is a transient dependency (i.e., it is accessed via other packages), then the full path by which the package is accessed is shown above it. You can click on any package shown in the path in order to open a new tab showing details for that package. TipFrequently, you can fix the vulnerabilities by updating the transient packages with their latest versions. |
Exploitability | Shows which exploitability indicators apply to this vulnerability. (KEV, POC, EPSS and Exploitable Path) |
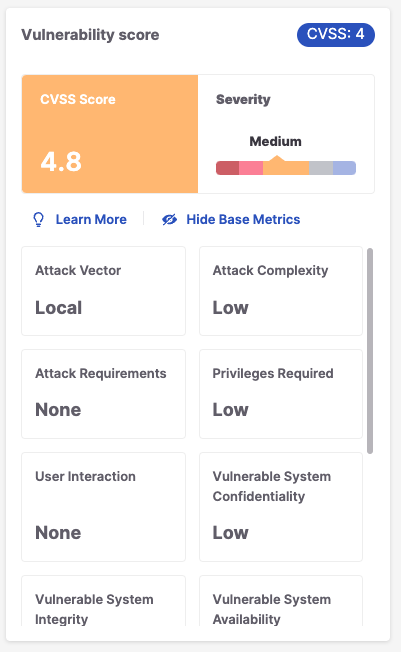
Vulnerability Score | Shows the CVSS Version, Score, and Severity, as well as the components that make up the CVSS score including: Attack Vector, Confidentiality Impact, Attack Complexity, Integrity Impact, Authentication, and Availability Impact. For a full explanation of the metrics that make up the CVSS score, see CVSS Score Details. |
Customization | Displays comments regarding this vulnerability and a link to view the risk management history. |
CVSS Score Details
The metrics that are used for calculating the CVSS score are different for each version. Therefore, the metrics shown when you click on View Base Metrics on the Risk page differ according to the version. Additional information about CVSS score calculation is available here.
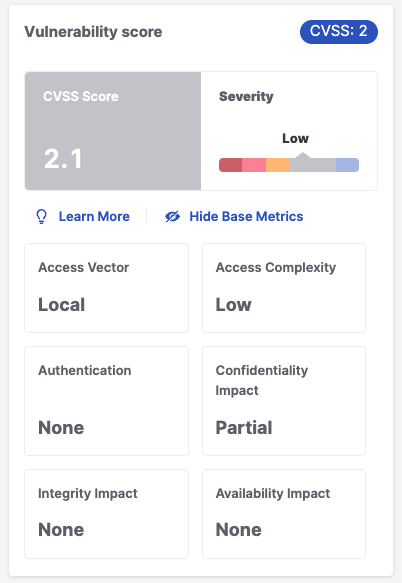
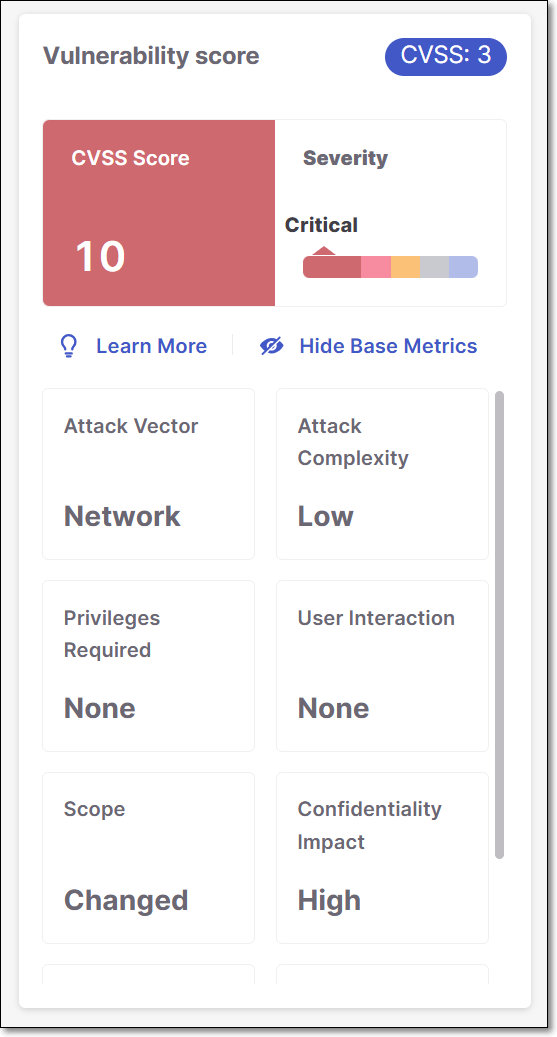
Detailed results for SCA vulnerabilities can be returned using the GET /results API. The results for each SCA vulnerability include a vulnerabilitiesDetails object. The attributes returned for this object differ depending on the CVSS version that is used for that vulnerability. You may need to adjust some of your workflows to accommodate the schema of the new type of results.
CVSS 2.0 | CVSS 3.1 | CVSS 4.0 |
|---|---|---|
"vulnerabilityDetails": { "cvssScore": 2.1, "cveName": "CVE-2015-3010", "cweId": "CWE-200", "cvss": { "score": 2.1, "version": 2, "severity": ["INFO", "NONE", "LOW", "MEDIUM", "HIGH"], "integrity": ["NONE", "PARTIAL", "COMPLETE"], "attackVector": ["LOCAL", "ADJACENT NETWORK", "NETWORK"], "availability": ["NONE", "PARTIAL", "COMPLETE"], "authentication": ["NONE", "SINGLE", "MULTIPLE"], "confidentiality": ["NONE", "PARTIAL", "COMPLETE"], "attackComplexity": ["LOW", "MEDIUM", "HIGH"], "exploitCodeMaturity": "3.9" } } | "vulnerabilityDetails": { "cvssScore": 5.5, "cveName": "CVE-2023-50120", "cweId": "CWE-835", "cvss": { "scope": ["CHANGED", "UNCHANGED"], "score": 5.5, "version": 3, "severity": ["INFO", "NONE", "LOW", "MEDIUM", "HIGH", "CRITICAL"], "integrity": ["NONE", "LOW", "HIGH"], "attackVector": ["NETWORK", "ADJACENT", "LOCAL", "PHYSICAL"], "availability": ["NONE", "LOW", "HIGH"], "confidentiality":["NONE", "LOW", "HIGH"], "userInteraction": ["NONE", "REQUIRED"], "attackComplexity": ["LOW", "HIGH"], "privilegesRequired": ["NONE", "LOW", "HIGH"], "exploitCodeMaturity": "3.9" } } | "vulnerabilityDetails": { "cvssScore": 4.800000190734863, "cveName": "CVE-2024-6064", "cweId": "CWE-416", "cvss": { "score": 4.8, "version": 4, "severity": ["INFO", "NONE", "LOW", "MEDIUM", "HIGH", "CRITICAL"], "attackVector": ["NETWORK", "ADJACENT", "LOCAL", "PHYSICAL"], "userInteraction": ["NONE", "PASSIVE", "REQUIRED"], "attackComplexity": ["LOW", "HIGH"], "attackRequirements": ["NONE", "PRESENT"] "privilegesRequired": ["NONE", "LOW", "HIGH"], "subsequentSystemIntegrity": ["NONE", "LOW", "HIGH"], "vulnerableSystemIntegrity": ["NONE", "LOW", "HIGH"], "subsequentSystemAvailability": ["NONE", "LOW", "HIGH"], "vulnerableSystemAvailability": ["NONE", "LOW", "HIGH"], "subsequentSystemConfidentiality": ["NONE", "LOW", "HIGH"], "vulnerableSystemConfidentiality": ["NONE", "LOW", "HIGH"] } } |
Examples of vulnerabilitiesDetails object for each CVSS version.
CVSS 2.0
"vulnerabilityDetails": {
"cvssScore" : 2.0999999046325684,
"cveName" : "CVE-2015-3010",
"cweId" : "CWE-200",
"cvss" : {
"score" : 2.1,
"version" : 2,
"severity" : "Low",
"integrity" : "NONE",
"attackVector" : "LOCAL",
"availability" : "NONE",
"authentication" : "NONE",
"confidentiality" : "PARTIAL",
"attackComplexity" : "LOW",
"exploitCodeMaturity" : "3.9"
}
}
CVSS 3.1
"vulnerabilityDetails": {
"cvssScore" : 7.5,
"cveName" : "CVE-2024-24265",
"cweId" : "CWE-401",
"cvss" : {
"scope" : "UNCHANGED",
"score" : 7.5,
"version" : 3,
"severity" : "High",
"integrity" : "NONE",
"attackVector" : "NETWORK",
"availability" : "HIGH",
"confidentiality" : "NONE",
"userInteraction" : "NONE",
"attackComplexity" : "LOW",
"privilegesRequired" : "NONE"
}
} CVSSS 4.0
"vulnerabilityDetails": {
"cvssScore" : 4.800000190734863,
"cveName" : "CVE-2024-6064",
"cweId" : "CWE-416",
"cvss" : {
"score" : 4.8,
"version" : 4,
"severity" : "Medium",
"attackVector" : "LOCAL",
"userInteraction" : "NONE",
"attackComplexity" : "LOW",
"attackRequirements" : "NONE",
"privilegesRequired" : "LOW",
"subsequentSystemIntegrity" : "NONE",
"vulnerableSystemIntegrity" : "LOW",
"subsequentSystemAvailability" : "NONE",
"vulnerableSystemAvailability" : "LOW",
"subsequentSystemConfidentiality" : "NONE",
"vulnerableSystemConfidentiality" : "LOW"
}
}Suspected Malware Details
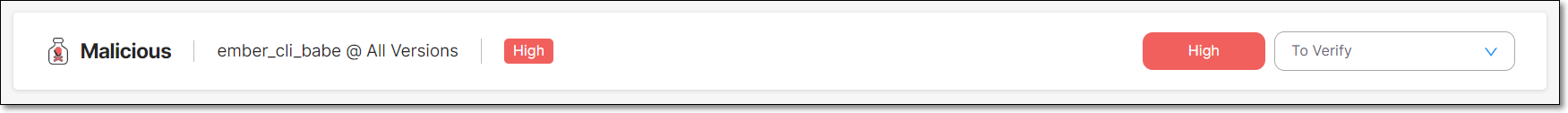
Suspected Malware includes various types of risks that affect the packages in your project, such as packages that are Malicious by design and packages that are vulnerable to ChainJacking attacks.
The Checkmarx One SCA scanner identifies packages with a wide range of known or suspected malware risks, and lists those risks in the scan results. Checkmarx SCA identifies suspected malware vulnerabilities of the following types:
Reputation - There is reason to suspect the credibility of the owner or contributors of the package, e.g., a newly created user is registered as the package owner.
Reliability - There are irregularities in the naming or maintenance patterns of the package, e.g., Typeosquatting, or Chainjacking.
Behavior - The behaviors of the package are unsafe. The package may be malicious by design or it may inadvertently introduce risks into your project. This category includes packages that exfiltrate info about OSs, user credentials etc.
The following table shows some examples of suspected malware risks of each type that are identified by Checkmarx SCA.
Title | Description |
|---|---|
Reputation | |
New User | The owner of this package is a newly created user. |
Protestware | Software that includes functionality which aims to protest or raise an issue - learn more |
Repojacking | Taking over the repository of a legitimate package - learn more |
Account takeover | The compromise of a good maintainers account by an attacker which is then used to spread malicious packages - learn more |
Reliability | |
Typosquatting | This package mimics the name of a popular package, inducing users to inadvertently call this package. learn more |
StarJacking | There is a weak link between the package metadata and the referenced Git repository. learn more |
This package is stored in a renamed GitHub repository, making it vulnerable to an attacker taking control of the repo and serving malicious code through the package. | |
Behavior | |
Harmful File Download | This package downloads a harmful file. |
This package was manually inspected by a security researcher and flagged as being malicious by design. | |
Data Exfiltration | This package exfiltrates sensitive information such as stored credentials or computer and operating system details. |
Network Anomaly | This package initiates one of the following anomalous network behaviors:
|
Crypto Miner | This package executes crypto mining software. |
Info Pane
 |
Item | Description | Possible Values |
|---|---|---|
ID | An internal ID starting with the “Cx” prefix that was assigned to this risk by the Checkmarx Vulnerability Research Team. | e.g., Cx27b685d0-978d |
Package | The name of the package in which the vulnerability was identified. | e.g., com.fasterxml.jackson.core:jackson-databind 2.9.8 |
Version | The version of the package where the vulnerability was identified. | e.g., 5.1.26 |
Risk Level | The severity level of the vulnerability, based on its CVSS score in the CVE database. Malicious (suspected malware) packages are labeled Malicious and the |
For more info see Severity Levels. |
Risk State | This indicates the current state of the suspected malware Risk as determined by your AppSec team. All new risks are initially marked as To Verify. A user with |
TipWhen the state is set as Not exploitable, the page is grayed out and the risk is marked with a strikethrough line on the All Risks tab. |
Suspected Malware Details Sections
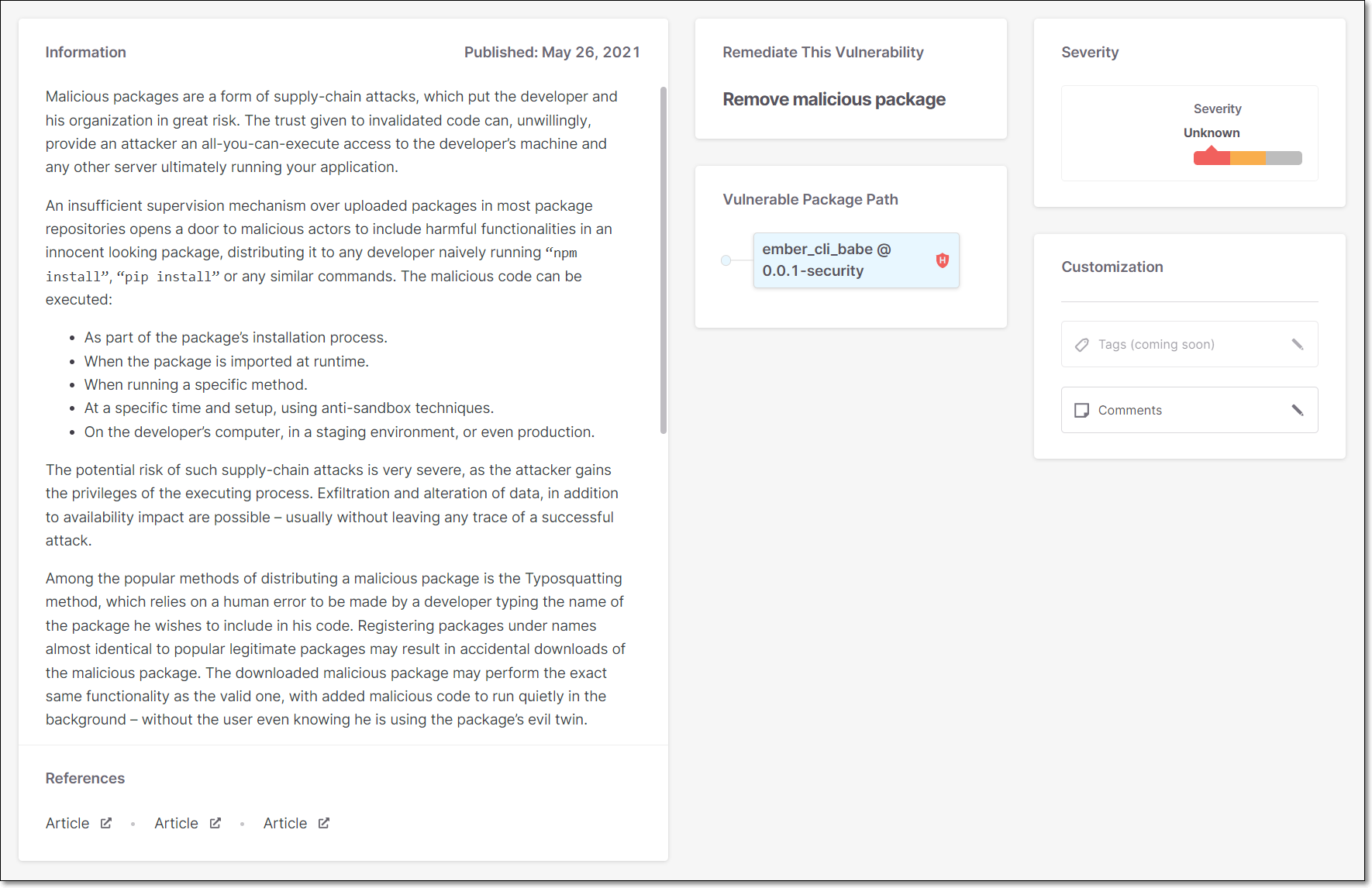 |
Item | Description |
|---|---|
Information | A description of the nature of the threat posed by the suspected malware and the date the suspected malware was published on the NVD. |
References | Links to external resources about the risk. Links are given for topics such as: Article, etc. |
Remediate this Vulnerability | Recommended steps that should be taken to remediate this vulnerability. |
Policies | The number of Policies the Project is assigned to and the number of Policy violations. |
Vulnerable Package Path | The vulnerable package is displayed in blue. If this is a transient dependency (i.e., it is accessed via other packages), then the full path by which the package is accessed is shown above it. You can click on any package shown in the path in order to open a new tab showing details for that package. TipFrequently, you can fix the vulnerabilities by updating the transient packages with their latest versions. |
CVSS/Risk Score | Shows the CVSS Version, Score, and Severity. For a full explanation of the metrics that make up the CVSS score, see section 2 of this article. |
License Details Page
This tab shows detailed information about a specific license, including the Legal Risks relating to the license.
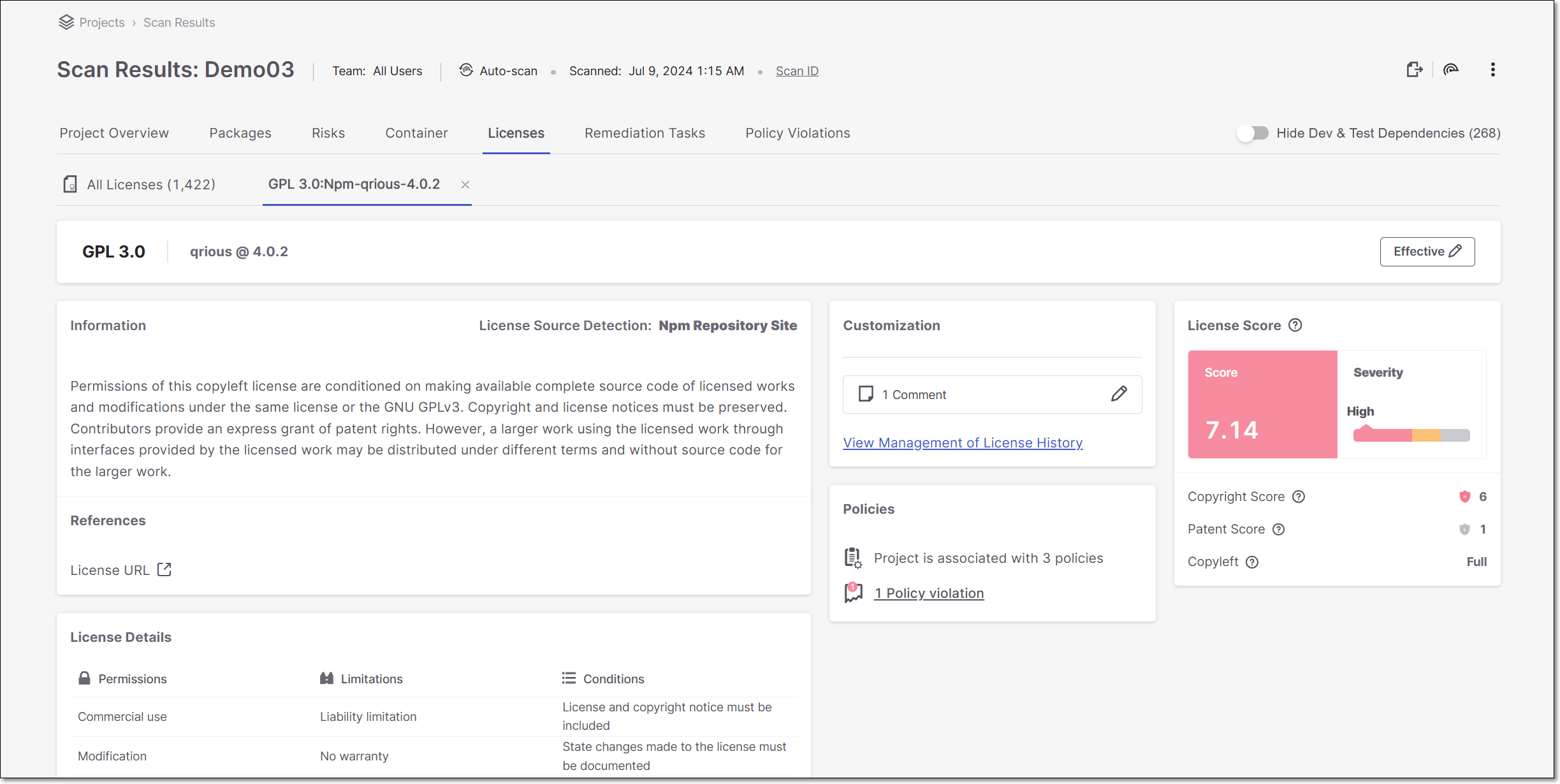
Info Pane
 |
Item | Description | Possible Values |
|---|---|---|
ID | The name of the License. | e.g., MIT |
Package | The name and version of the package that the license is associated with. | e.g., Fuzzball@1.4.0 |
State | The current state of the license. |
|
Legal Risk Details Sections
Item | Description |
|---|---|
Information | The source of the license detection followed by a description of the nature of the threat posed by the legal risk. |
References | Links to external resources about the vulnerability. Links are given for topics such as: License URL, etc. |
Customization | View state changes and comments for this license. An admin user can mark a license as “Effective” for this package (i.e., if they intend to consume this package in accordance with the licensing restrictions of this license.). |
Policies | The number of Policies the Project is assigned to and the number of Policy violations. |
Legal Score | Shows the License Score and Severity, as well as the components that make up the License score including: Copyright Risk, Patent Risk and Copyleft. For an explanation on the calculation of these scores, see below. |
License Details | Additional details about the terms of use of the license. This is divided into sections for Permissions, Limitations and Conditions. |
Understanding the License Score Section
The License Score pane shows the overall License Score and severity as well as information about specific license risk characteristics. The following table explains these items:
Notice
The License Score represents the level of risk associated with using a package under that license. However, the license doesn't pose an actual risk to your project unless you are actually using the package under that license (i.e., it is your Effective license).
Field | Value type and range | Details |
|---|---|---|
Copyright Risk Score | A number between 1 and 7 | The score is defined as follows:
TipThe Legal Risk calculation is based on the copyright risk score, where Level 1-3 is considered as a low risk, Level 4-5 as a medium risk, and Level 6-7 as a high risk. |
Patent Risk Score | A number between 1 and 4 Sometimes represented as multiplications of 20, since in CxOSA is presented on a scale of 1-100 | Ranks the license based on
|
Copyleft | One of the following: Full, Partial, No | Copyleft is a property of the license that means that the package is free to use, but it is forbidden to make it proprietary. A copyleft license is also viral since any work containing a package that has a copyleft-license must also retain this property. The valid values are described as follows:
|
Container Tab
Warning
This tab, which is part of SCA results viewer, is only in use for accounts that are still using the original Container scanner. For accounts that use the new Container Security scanner, the results are shown in the separate Container Security Results Viewer.
In addition to scanning the packages in your source code itself, Checkmarx SCA also scans the containers (i.e., Docker image files) on which your source code runs. Checkmarx SCA identifies each of the Docker files being used, extracts all layers of each Image file and identifies the packages used by each layer.
The Container tab shows the container packages identified in your project and the vulnerabilities associated with them.
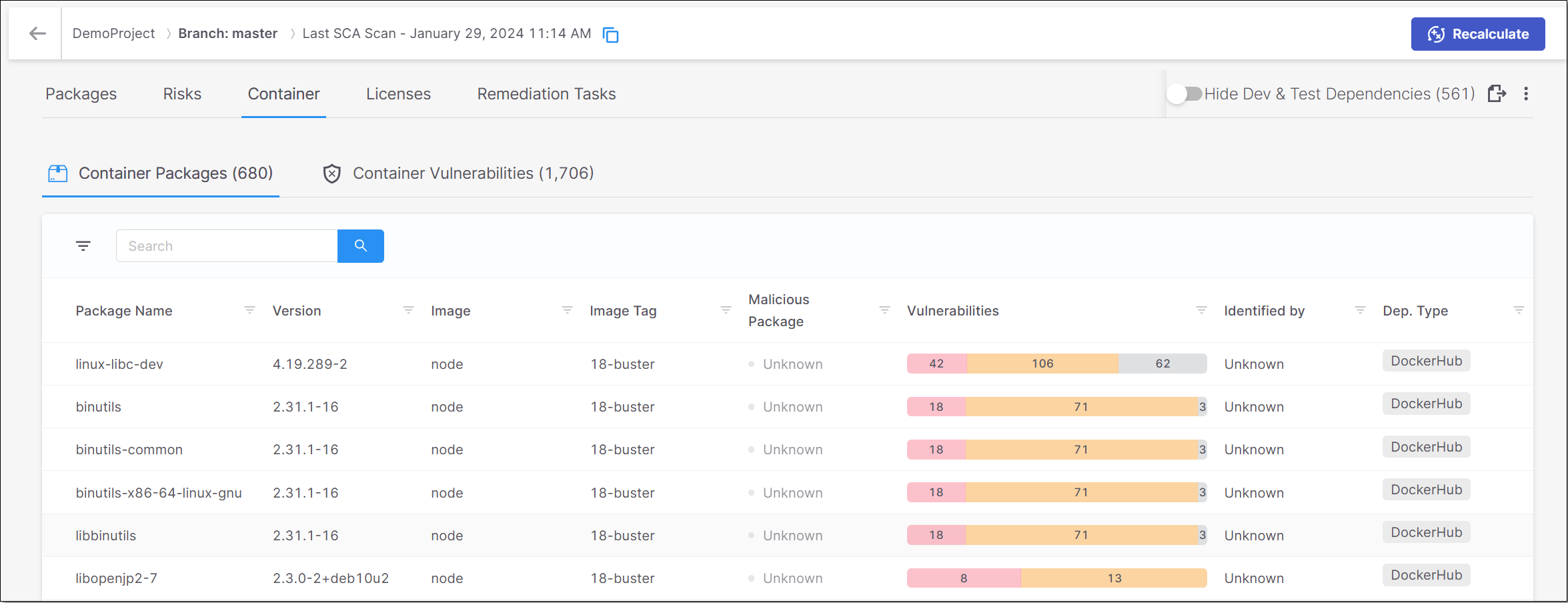
The Container tab contains two sub-tabs:
Container Packages – shows a list of all of the packages identified in the container images.
Container Vulnerabilities – shows a list of all of the vulnerabilities associated with the container packages.
The Container Packages sub-tab shows a list of all of the packages identified in the container images. For each container package, info is shown about the risks related to that package. You can search for specific packages and images using the search box.
You can also sort by column headers and set filters for each column.
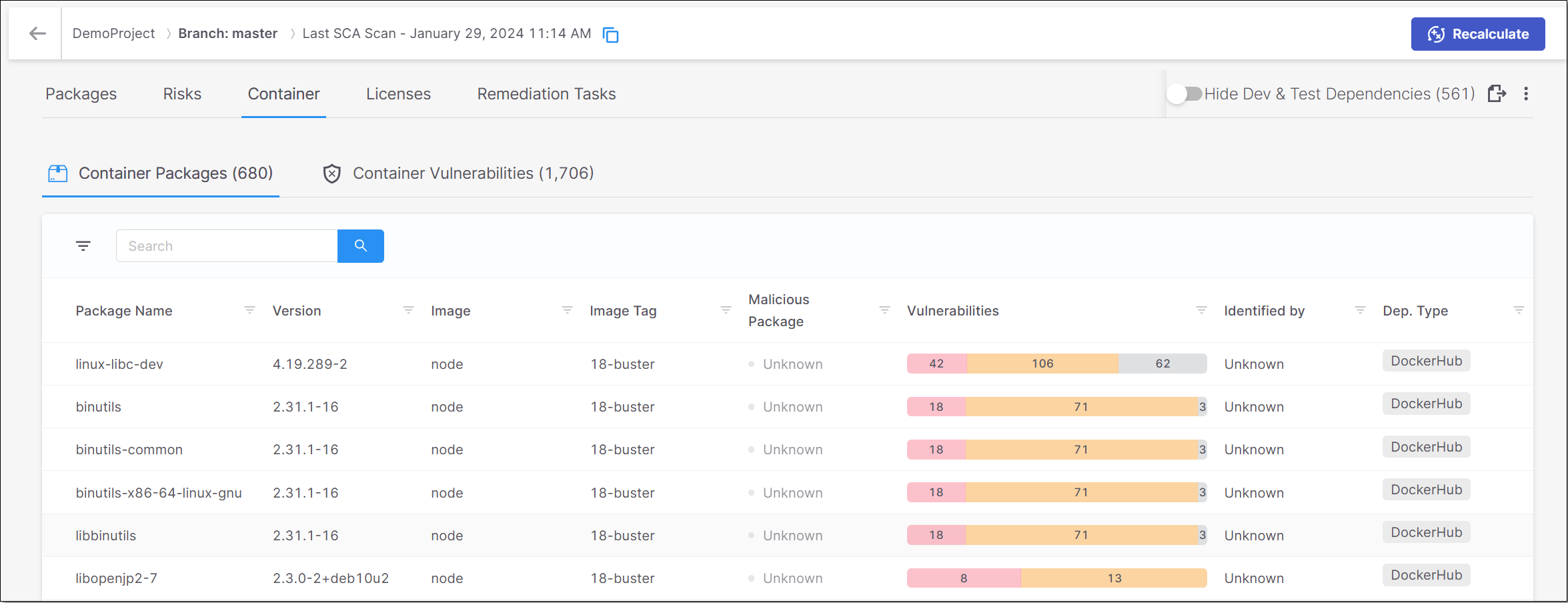
The following table describes the info shown for each package identified in the containers.
Item | Description | Possible Values | |
|---|---|---|---|
Package Name | The name of the package. | e.g., musl | |
Version | The version of the package. | e.g., 1.2.2-r1 | |
Image | The name of the image that was scanned. | e.g., python | |
Image Tag | The version of the image. | e.g., rc-alpine3.13 | |
Vulnerabilities | A color coded bar graph indicating the number of vulnerabilities of each severity level. | e.g.,
| |
Identified By | The path to the Docker file in which the specific image is found. (Hover to view the entire path.) | e.g., Joao4/JavaVulnerableLab-dockerfile/JavaVulnerableLab-master/dockerfile1/Dockerfile | |
Dep. Type | The repository in which the image is located. | e.g., Docker Hub |
The Container Vulnerabilities sub-tab shows a list of all of the vulnerabilities associated with the container packages. Detailed information is shown for each vulnerability. You can search for specific vulnerabilities and packages using the search box.
You can also sort by column headers and set filters for each column.
You can click on a vulnerability to open a new tab showing additional info about the vulnerability.
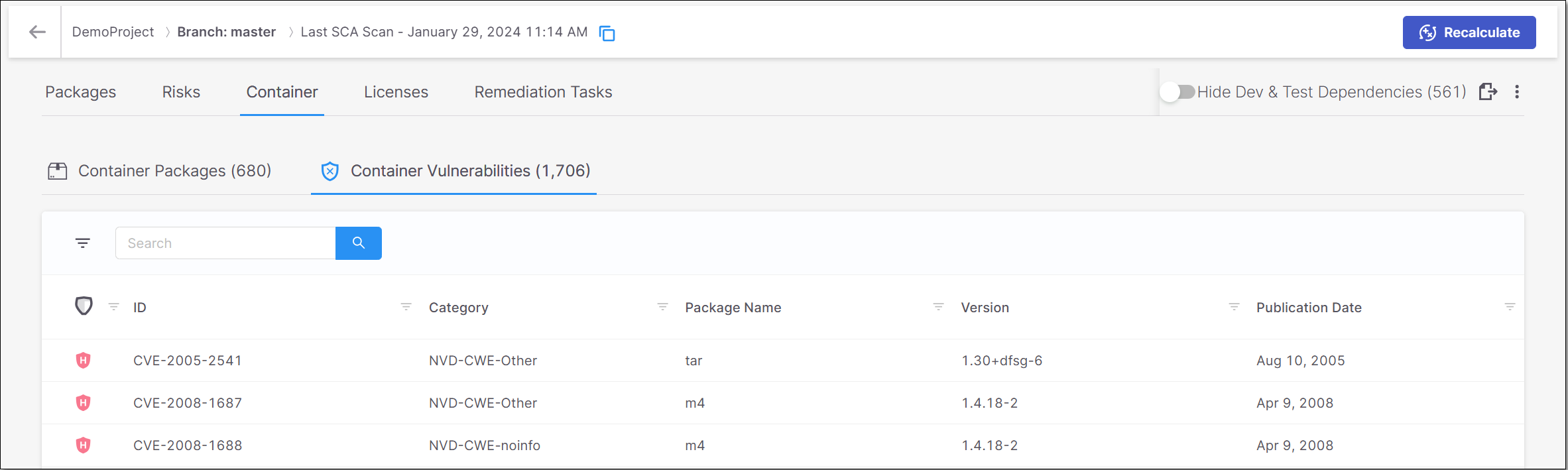
Notice
Container vulnerabilities for which the Category is "unknown" are marked as Low severity. Also, these vulnerabilities are only shown in the summary table, but you can't drill down to view the details page, since there are no details that we can provide.
The following table describes the info shown for each vulnerability that was identified in the containers.
Item | Description | Possible Values |
|---|---|---|
Risk Level | The severity level of the vulnerability. |
For more info see Severity Levels. |
ID | The ID of the CVE listing. The ID consists of the CVE prefix followed by the year that the CVE was discovered and the serial counter for that year's CVE listings. | e.g., CVE-2020-9488 |
Category | The category of the vulnerability. | e.g., CWE-20 |
Package Name | The name of the package in which the vulnerability was identified. | e.g., musl |
Version | The version of the package in which the vulnerability was identified. | e.g., 1.2.2-r1 |
Publication Date | The date that this vulnerability was first officially published on a supported public Security Advisory. | e.g., Nov 16, 2020 |
Licenses Tab
The Licenses tab shows info about all of the licenses that are associated with the open source packages used by your project.
Notice
This page shows all licenses, even those that don't pose any particular legal risk. All license that pose a specific legal risk are shown in the Legal Risks section on the Risks tab.
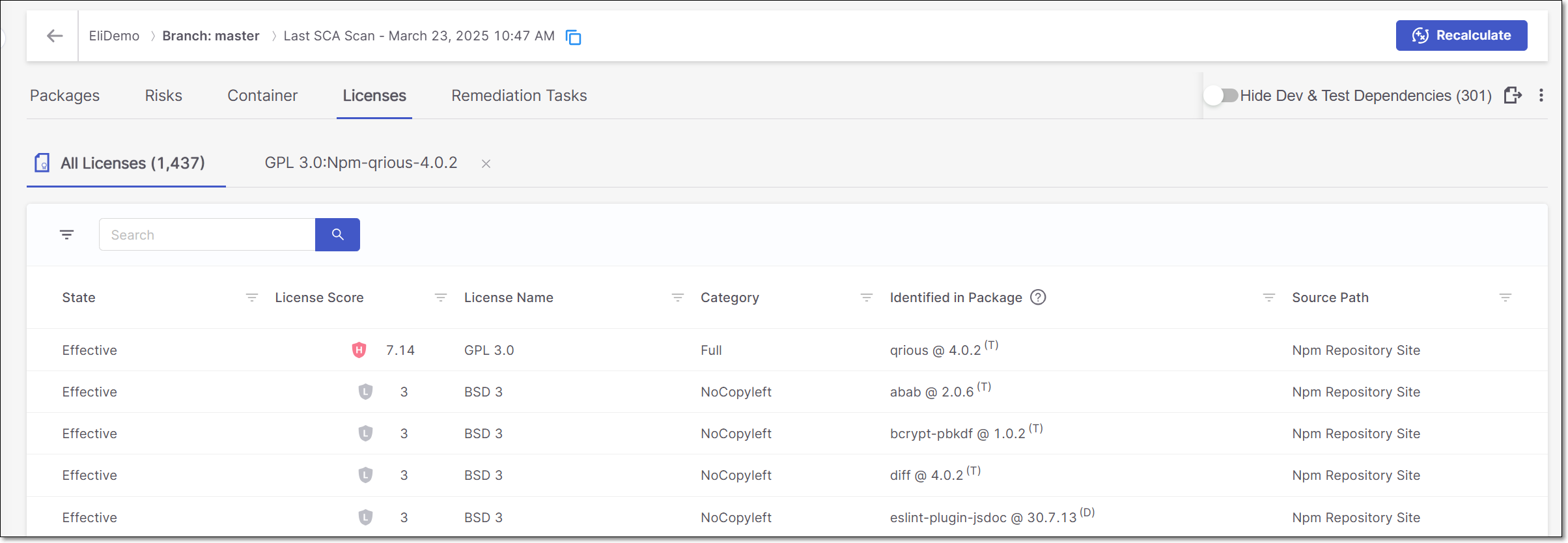
The Licenses tab contains sub-tabs that show two types of pages:
All Licenses – shows a list of all licenses associated with the open source packages identified in this scan.
License Details – shows detailed info about a specific license. Click on a row in the All Licenses tab to access this page.
You can navigate between the various tabs that you have opened.
All Licenses Page
The All Licenses sub-tab shows a list of all licenses associated with the open source packages identified in this scan. A separate row is shown for each license that applies to a particular package version. Therefore, if a license applies to multiple packages or package versions, then a separate row will be shown for each instance.
You can also sort by column headers and set filters for each column.
The following table describes the info shown for each license identified by this scan.
Item | Description | Possible Values |
|---|---|---|
State | Indicates whether or not this license is the "effective" license for your organization's use of this package. Also, if the package to which the license applies has been muted or snoozed, this is indicated in the State column. TipA license that was identified from a reliable source and is the sole license for the package is automatically marked as Effective. Otherwise it is marked as Not Effective by default and it can be manually changed to Effective. |
|
License Severity and Score | Shows the severity level and score indicating the overall risk level associated with this license. TipIf this isn't the effective license for this package, then a high license score doesn't necessarily pose a legal risk. |
|
License Name | The name of the license. | e.g., GPL 3.0, MIT etc. |
Category | The category of the license. |
|
Identified in Package | The name and version of the package that the license is associated with. In addition, an indication is shown for whether this is a direct. transitive or mixed (i.e., both direct and transitive) dependency (D, T or M). Results can be filtered by Direct/Transitive/Mixed. | e.g., loadash @ 4.13.1 (T) |
Source Path | The source from which the license was identified. | e.g., Manifest File, Npm Repository Site, Official Website, Statically Observed etc. TipThe category "Statically Observed" indicates that the license was identified in the source code (e.g., README files) using regex and other identification methods. |
License Details Page
The tab shows detailed information about a specific license, including the Legal Risks relating to the license.
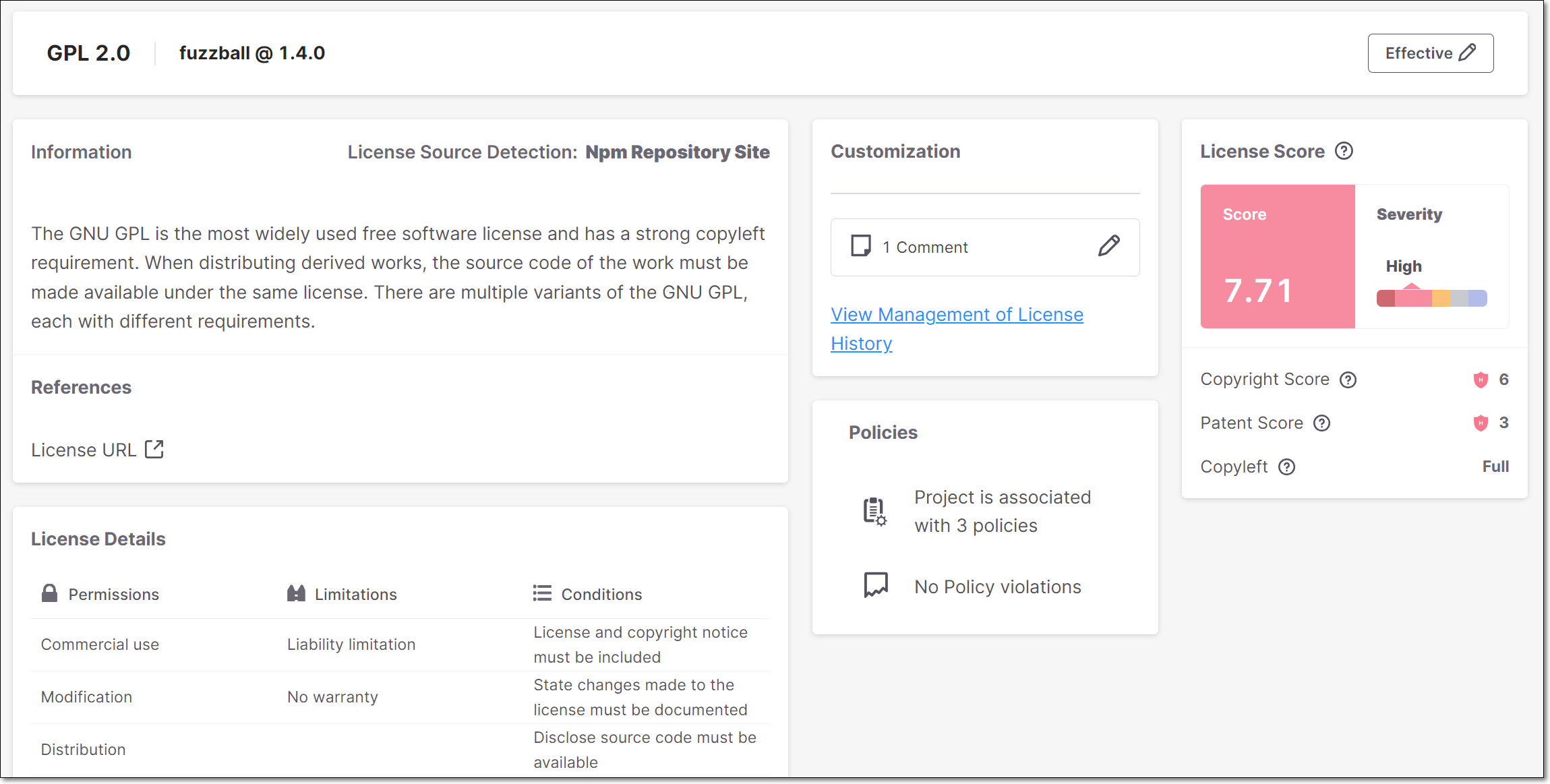 |
Info Pane
 |
Item | Description | Possible Values |
|---|---|---|
Name | The name of the License. | e.g., GPL 2.0 |
Package | The name and version of the package that the license is associated with. | e.g., Fuzzball@1.4.0 |
State | The current state of the license. |
|
License Info Sections
Item | Description |
|---|---|
Information | The source of the license detection followed by a description of the nature of the threat posed by the legal risk. |
References | Links to external resources about the vulnerability. Links are given for topics such as: License URL, etc. |
Customization | View state changes and comments for this license. An admin user can mark a license as “Effective” for this package (i.e., if they intend to consume this package in accordance with the licensing restrictions of this license.). |
Policies | The number of Policies the Project is assigned to and the number of Policy violations. |
License Score | Shows the License Score and Severity, as well as specific characteristics of the license, including: Copyright Risk, Patent Risk and Copyleft. For an explanation of these items, see below. |
License Details | Additional details about the terms of use of the license. This is divided into sections for Permissions, Limitations and Conditions. |
Understanding the License Score Section
The License Score pane shows the overall License Score and severity as well as information about specific license risk characteristics. The following table explains these items:
Notice
The License Score represents the level of risk associated with using a package under that license. However, the license doesn't pose an actual risk to your project unless you are actually using the package under that license (i.e., it is your Effective license).
Field | Value type and range | Details |
|---|---|---|
Copyright Risk Score | A number between 1 and 7 | The score is defined as follows:
TipThe Legal Risk calculation is based on the copyright risk score, where Level 1-3 is considered as a low risk, Level 4-5 as a medium risk, and Level 6-7 as a high risk. |
Patent Risk Score | A number between 1 and 4 Sometimes represented as multiplications of 20, since in CxOSA is presented on a scale of 1-100 | Ranks the license based on
|
Copyleft | One of the following: Full, Partial, No | Copyleft is a property of the license that means that the package is free to use, but it is forbidden to make it proprietary. A copyleft license is also viral since any work containing a package that has a copyleft-license must also retain this property. The valid values are described as follows:
|
Remediation Tasks Tab
Overview
The Remediation Tasks tab shows detailed information about specific remediation tasks that Checkmarx recommends implementing for your Project. These tasks involve replacing vulnerable packages in your project with non-vulnerable versions of those packages.
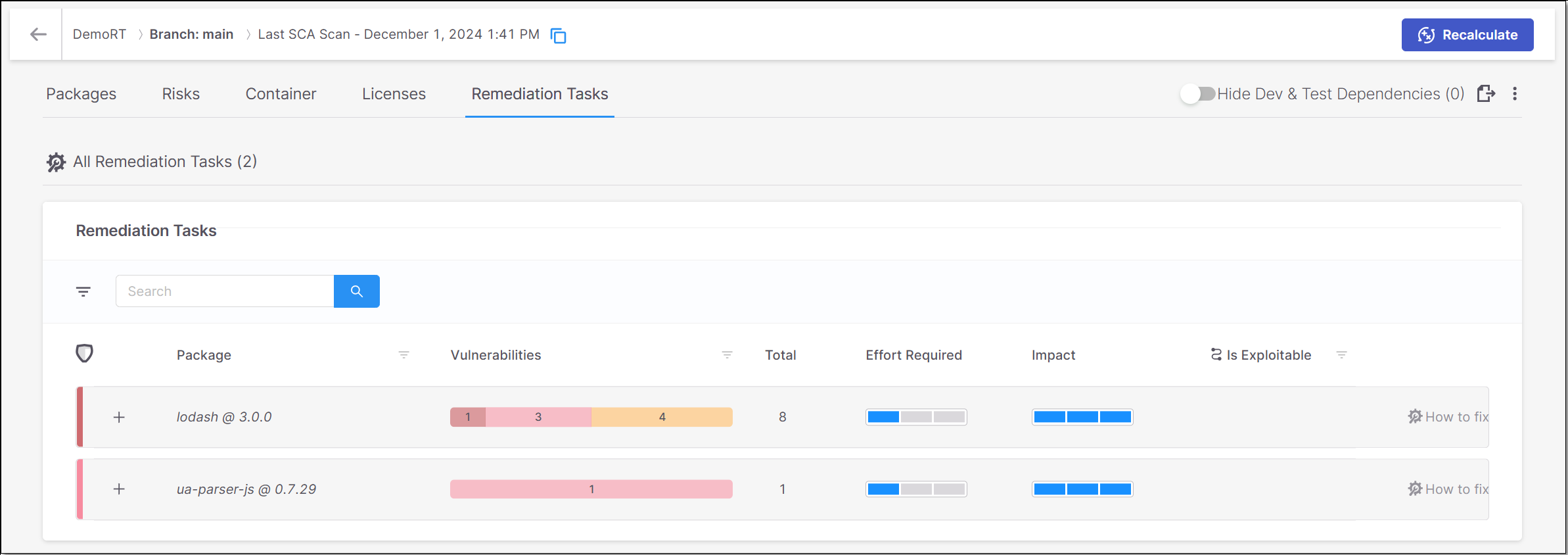 |
The Remediation Tasks tab contains sub-tabs that show two types of pages:
All Remediation Tasks – shows a list of remediation tasks that are recommended for this Project, with general info about each task.
Task Details – shows detailed info about a specific task. The task details tab is opened by clicking on the How to fix button in a task row in the All Remediation Tasks sub-tab.
You can navigate between the various tabs that you have opened.
Limitations
Remediation tasks are currently supported only for JavaSript npm packages and for Nuget packages with .csproj manifest files, otherwise this tab isn't shown.
We only show tasks for direct packages that have vulnerabilities in the package itself or in the transitive packages that it uses. Similarly, sub-tasks are only shown for transitive packages that have vulnerabilities.
Note
For example, if a direct package doesn't have any vulnerabilities itself but it uses 5 transitive packages of which 3 have vulnerabilities, then the direct package will be shown as well as the 3 vulnerable transitive packages.
We only show remediation tasks when there is an available version of the package in which all of the vulnerabilities have been remediated.
Notice
There are some circumstances in which the remediated package does have vulnerabilities. This occurs when all exisiting vulnerabilities were remediated, but some new vulnerabilities were introduced in the remediated version.
All Remediation Tasks
The All Remediation Tasks sub-tab shows a list of remediation tasks that are recommended for this Project.
Notice
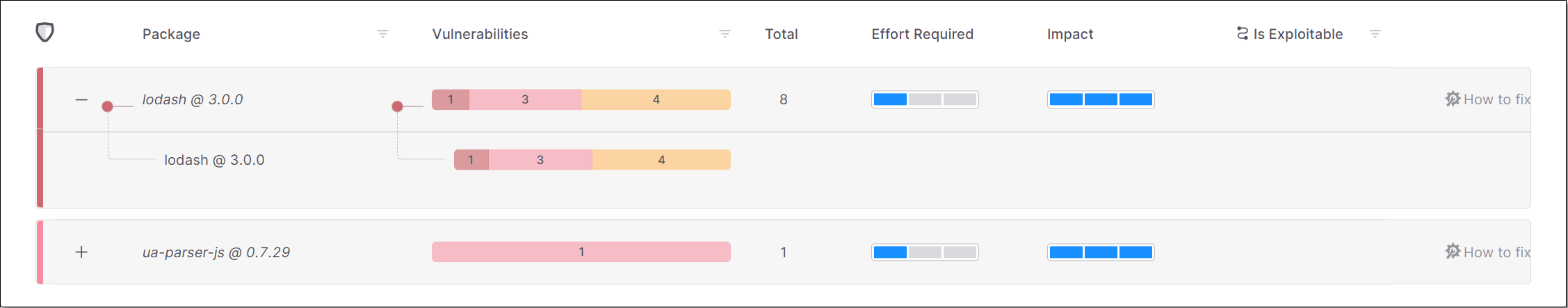
Each task relates to a specific direct package in your project.
The data shown for each task relates to the vulnerabilities identified in the direct package as well as in the transitive dependencies associated with it. You can click on the “+” button for a task to expand the view of that task to show the transitive dependencies called by the package. The number of vulnerabilities of each severity level is shown for each transitive package.
 |
The following table describes the info shown for each task:
Parameter | Description |
|---|---|
+/- Button | Expand the display to show the transitive packages or collapse the display to show only the direct package. |
Package | The name of the package and its version number. |
Vulnerabilities | The number of vulnerabilities of each severity level in the package. |
Total | The total number of vulnerabilities in the package. |
Effort Required | An assessment of the degree of effort required to implement the recommended remediation task, e.g., if it requires fixing broken API methods. |
Impact | An assessment of the impact that the remediation task will have on your Project, i.e., the extent to which the procedure will remove risks from your Project. |
Is Exploitable | Indicates whether the vulnerabilities in this package are exploitable in the context of your Project. TipThis data is only shown for scans which ran using the Exploitable Path feature. |
“How to fix” button | Click on this button to open a new sub-tab showing details about this remediation task. |
Remediation Task Details
The Remediation Task Details sub-tab shows detailed info about a specific remediation task.
Notice
Each task relates to a specific direct package in your project.
The info on this screen is shown in the following panes.
Overview - shows key metrics for the remediation task.
Summary - shows general info about the remediation task.
Remediation Impact - shows a comparison between the current vulnerabilities and the vulnerabilities that will remain after remediation.
Developer Walkthrough - shows a breakdown of the steps that need to be taken to remediate this package.
Overview
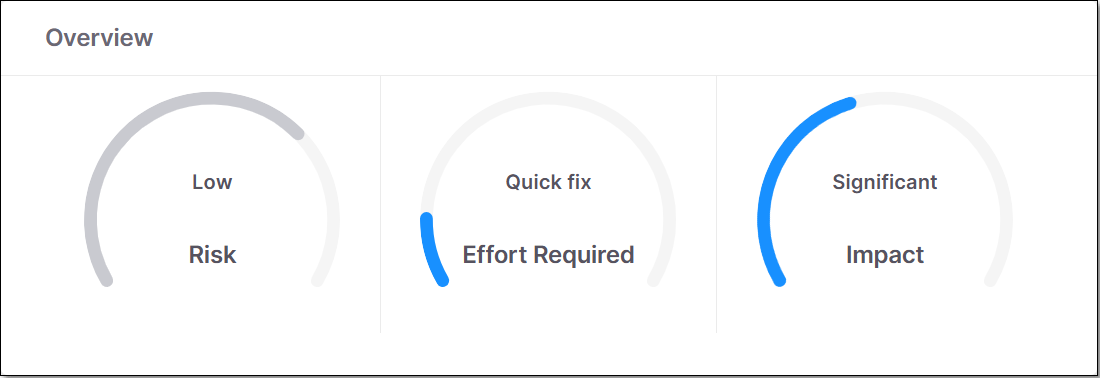 |
This pane shows gauge widgets indicating the overall risk level for the specified package, the effort required to implement the suggested remediation procedure and the impact of remediation.
Summary
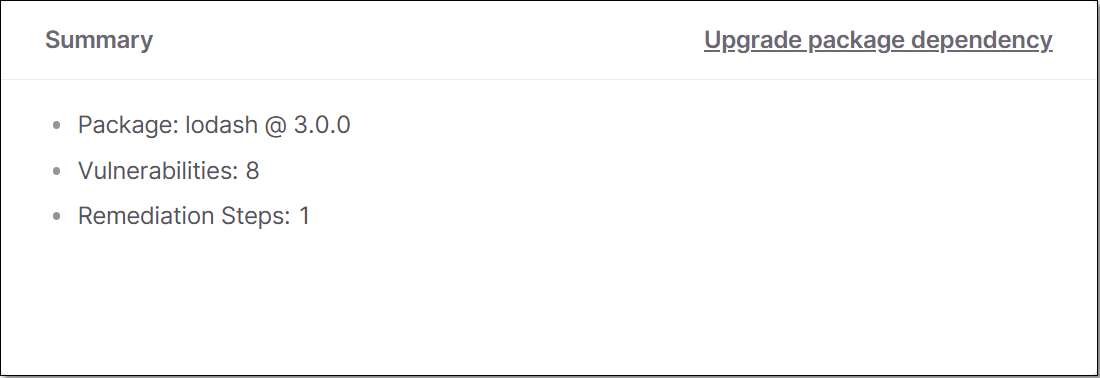 |
This pane shows a summary of the remediation task, including the package name, number of vulnerabilities and total number of remediation steps.
Remediation Impact
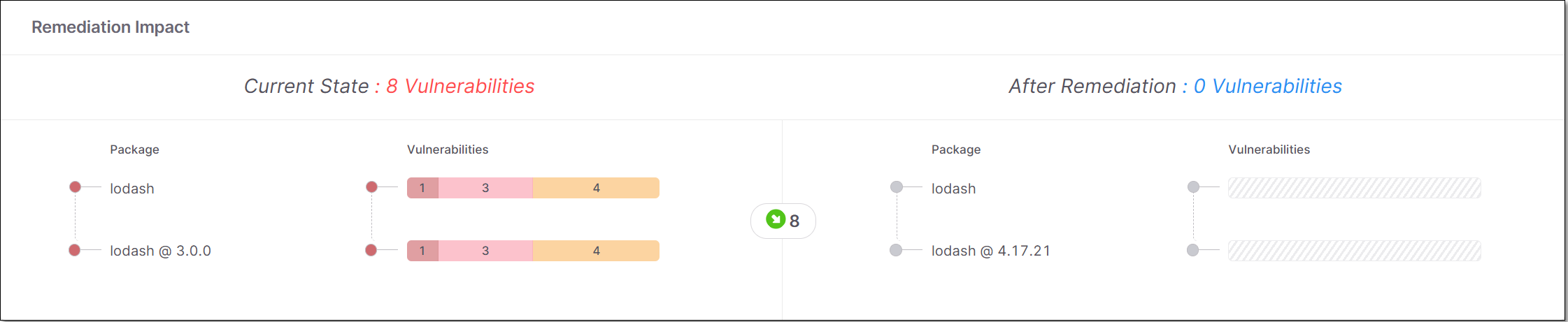 |
This pane shows a side-by-side comparison between the vulnerabilities currently in the direct and transitive dependencies and the vulnerabilities that will remain after remediation.
Developer Walkthrough
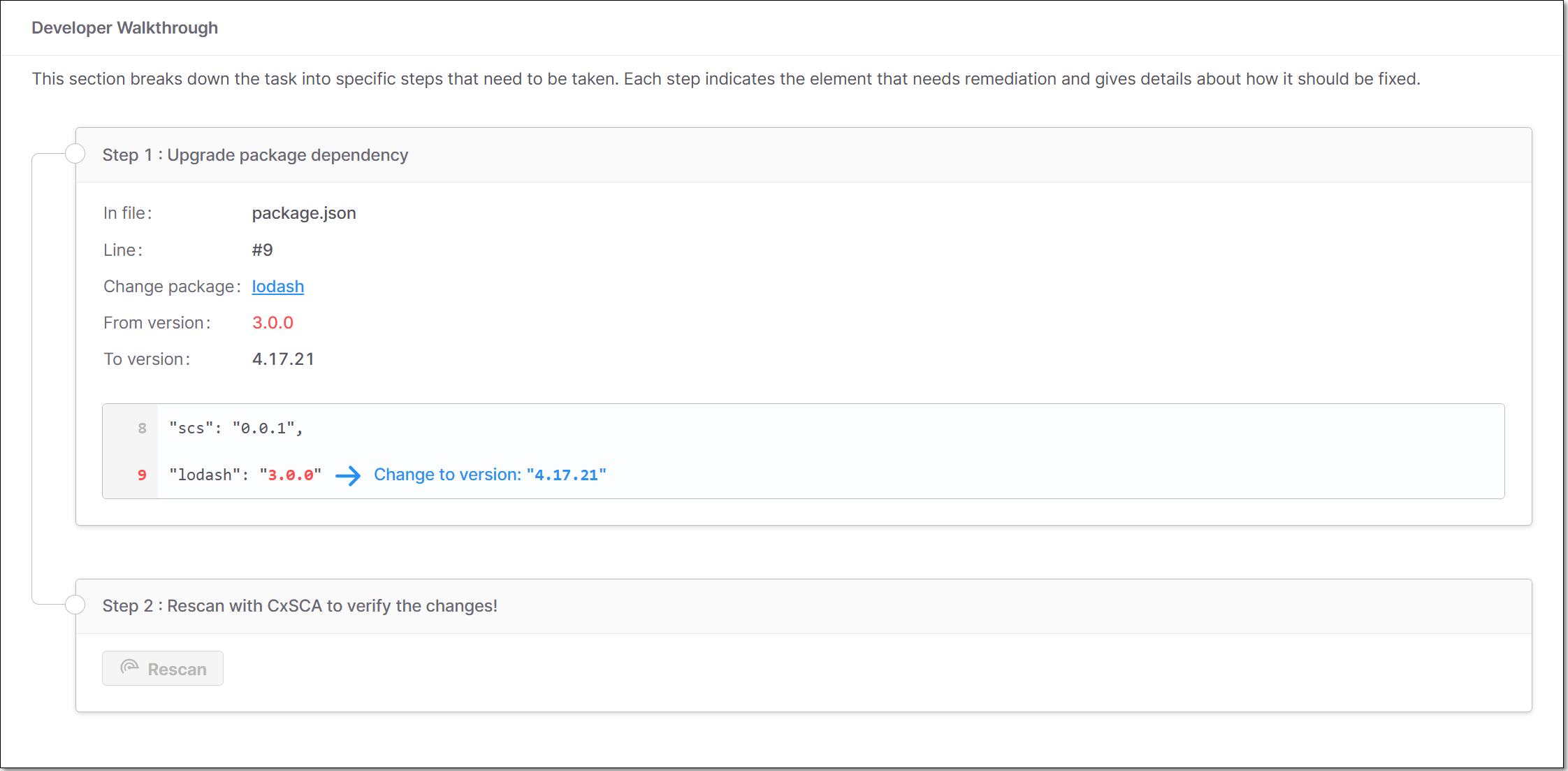 |
This section breaks down the task into specific steps that need to be taken. Each step indicates the element that needs remediation and gives details about how it should be fixed. There are three types of steps:
Upgrade package dependency - indicates the direct package that needs to be upgraded, where it appears in your code, and which version it should be upgraded to.
Add package dependency - indicates a specific version of a package that needs to be added to your manifest file (for transitive dependencies).
Notice
Recommended steps for remediating transitive vulnerabilities are given for each package independently. We recommend a secure version of the package that can be added to the manifest file in order to ensure that only that version will be used.
In some cases it may be possible to remediate transitive dependencies by upgrading the direct dependency to a version that references a newer, secure version. For Maven packages, the Maven repository shows the transitive package versions referenced by each package.
Fix broken API methods - shows each of the API methods that was broken and which upgrade caused the API to break. Fix broken API methods is shown as a sub-step under the “Upgrade package dependency” step that causes the broken method.
Note
Broken methods are only identified in scans for which the Exploitable Path feature is run.
We identify broken API methods by comparing the number of parameters used in the public method for the new package with the number of parameters used for the original package. If the number of parameters is different, then we notify of the need to fix the API method.