Checkmarx Developer Assist
About Developer Assist
Overview
Checkmarx Developer Assist delivers context-aware security guidance directly within your IDE, helping prevent vulnerabilities before they reach the pipeline. As developers write or refine AI-generated and existing code, it provides real-time detection, remediation, and actionable insights—ensuring security is built in from the start.
Checkmarx Developer Assist comprises two main elements:
Realtime Scanning - Identify vulnerabilities in realtime during IDE development of both human-generated and AI-generated code. Our super-fast scanners run in the background whenever you edit a relevant file. Our scanners identify vulnerabilities and unmasked secrets in your code. We also identify vulnerable or malicious container images and open source packages used in your project. Results are marked as Problems which are highlighted in the code and annotated with identifying icons.
Agentic-AI Remediation – Initiate an Agentic-AI session to receive remediation suggestions. Checkmarx feeds all relevant info to the AI agent which accesses our Model Context Protocol (MCP) server to gather data from our proprietary databases and customized AI models. The AI assistant then uses this data to generate remediated code for your project. You can accept the suggested changes or you can chat with the AI agent to learn more about the vulnerability and fine-tune the remediation suggestion.
In order to help you focus on actionable risks, Checkmarx Developer Assist enables marking risks as Ignore, so that the risks will no longer be shown in your IDE. You can Revive a risk at any time to resume showing that risk.
Key Features
An advanced security agent that delivers real-time context-aware prevention, remediation, and guidance to developers from the IDE.
Realtime scanners identify risks as you code.
AI Secure Coding Assistant (ASCA), a lightweight source code scanner, enables developers to identify secure coding best practice violations in the file that they are working on as they code.
Specialized realtime scanners identify vulnerable open source packages and container images, as well as exposed secrets and IaC risks.
MCP-based agentic AI remediation.
AI powered explanation of risk details.
Reduce noise by marking false positives as ignored.
About Model Context Protocol (MCP) Server
The Checkmarx MCP Server is a secure gateway that bridges AI-powered development assistants with the Checkmarx security platform. It defines the tools and APIs that allow AI agents — such as GitHub Copilot, Cursor AI, or Windsurf AI — to interact safely with Checkmarx’s cloud services directly from within the IDE.
Once the developer successfully authenticates in the IDE, the MCP Service is automatically installed. It can also be installed manually if required. For installation and configuration instructions, see below.
What is MCP?
Model Context Protocol (MCP) is an emerging open standard that enables communication between AI agents and external systems in a structured, secure, and context-aware way. By adopting MCP, Checkmarx ensures that any IDE-integrated AI assistant can securely access Checkmarx engines and services — including SAST, SCA, IaC, and API Security — through a unified interface.
Why Checkmarx Chose MCP
Checkmarx selected the MCP standard as the foundation for our agentic architecture because it provides:
Interoperability: MCP is vendor-neutral and supported by a growing ecosystem of AI tools. It allows Checkmarx to connect seamlessly with multiple AI assistants and IDEs using a consistent communication layer.
Security and Governance: MCP enforces strict access control and contextual awareness, ensuring that only the right data is exposed to the AI agent under the right conditions. This aligns with enterprise-grade compliance and governance models.
Scalability: The protocol supports multi-agent environments where different AI assistants operate across complex enterprise setups, making it ideal for large-scale deployments.
Future-readiness: As new IDEs and AI tools adopt MCP, Checkmarx can easily integrate without changing the underlying architecture — ensuring long-term compatibility and innovation flexibility.
How it Works
Once enabled, the Checkmarx MCP Server:
Authenticates the developer’s IDE session with Checkmarx.
Exposes the available Checkmarx tools and capabilities (e.g., code scanning, remediation, policy enforcement) as AI-accessible functions.
Allows the AI assistant to invoke these tools securely, analyze code, and propose context-aware fixes directly in the IDE.
This creates a secure, AI-augmented development experience — where Checkmarx intelligence powers real-time risk identification and remediation during coding.
See below for additional details as well as instructions for installing and using the MCP server as part of Checkmarx Dev Assist.
Recommended Models for Code Remediation
Based on a combination of internal evaluation and publicly available coding benchmarks, we have determined that the following models currently provide the most reliable results when performing complex remediation tasks.
Caution
Even the most advanced models currently struggle to consistently generate fully secure and production-ready backend code. Research benchmarks show that a large proportion of generated solutions still contain vulnerabilities or functional issues.
Also, keep in mind that these recommendations are based on current performance of available models. However, since this is a constantly fluctuating market, the list of preferred models is likely to change over time.
Recomendation Methodolgoy
These recommendations are based on a combination of internal evaluation and publicly available coding benchmarks. Internally, we assess models in secure code remediation scenarios, evaluating their ability to:
generate correct code fixes
perform safe refactoring across multiple files
maintain compilation integrity
preserve existing tests and generate additional tests when necessary
In addition to internal testing, we review results from industry and academic benchmarks that evaluate LLM performance on code generation, reasoning, and secure backend development. These include benchmarks such as BaxBench, which evaluates the ability of LLMs to generate secure and correct backend applications across multiple frameworks and programming languages.
BaxBench results highlight that even state-of-the-art models still struggle to consistently produce both correct and secure code, with many generated solutions containing vulnerabilities or functional errors. By combining insights from these benchmarks with internal testing, we identify models that currently provide the most reliable outcomes for code remediation and security-aware refactoring workflows.
Developer Assist Data Security FAQ
Realtime Scanning
Realtime scans run automatically as you work in your IDE. The following is a list of scan triggers:
As soon as you open the workspace, the SCA scanner scans the manifest files.
When you open any artifact that is supported for real-time scanners it is scanned by the relevant scanner.
When you edit any supported artifact.
When you save a supported file to an external location.
When you use an AI assistant (e.g. Copilot), to make changes to a supported file.
The following sections describe the various realtime scanners that are included in Checkmarx Dev Assist.
Checkmarx AI Secure Coding Assistant (ASCA) Realtime Scanner
The ASCA is a lightweight source code scanner that enables developers to identify secure coding best practice violations in the file that they are working on as they code. The ASCA scanner runs in the background as you work in your IDE. Unlike SAST engines that scan entire projects and analyze complex source code flows, ASCA focuses on individual files and short code snippets, including AI-generated code.
Whenever you edit a file in VS Code the ASCA scanner automatically scans that file. The ASCA scan runs on your local machine as a running process and returns results within milliseconds.
Notice
Editing a file triggers new detection after 1 second of inactivity.
Supported Languages
ASCA currently supports Java, JavaScript (Node.js), C#, Go and Python.
IaC Realtime Scanner
The IaC Realtime scanner (based on the KICS opens source project powered by Checkmarx) examines configuration definitions and scripts used to instantiate infrastructure to ensure the resulting resources are secure.
A scan runs automatically whenever you edit an infrastructure file of a supported type.
Notice
Editing a file triggers new detection after 1 second of inactivity.
Prerequisites
You must have a supported container engine (e.g., Docker, Podman etc.) installed and running in your environment.
Open Source Realtime Scanner (OSS-Realtime)
Checkmarx’s OSS-Realtime scanner is a lightweight version of our SCA scanner that analyzes your manifest files and quickly identifies risks associated with your open source dependencies. This includes vulnerable packages as well as packages that we have identified as malicious.
Caution
The OSS realtime scanner is less comprehensive than the full Checkmarx One SCA scanner, see Supported Manifest Files and Known Limitations below.
Scans are triggered when the developer opens a project in the IDE that includes a manifest file (e.g., package.json, requirements.txt). In addition, whenever the developer adds, moves or edits a manifest file within the IDE the project is re-scanned.
Notice
Editing a file triggers new detection after 1 second of inactivity.
Supported Manifest Files
In the initial phase, the plugin supports the following popular manifest files:
Dotnet:
csproj,directory.packages.props,packages.configMaven:
pom.xmlnpm:
package.jsonPip:
requirements.txt(limited support, see Known Limitations below)Go:
go.mod
Known Limitations
Identifies vulnerabilities only in direct packages not in transitive dependencies.
For Python
requirements.txtfiles, only tradional, manually created files are supported (i.e., package==version format). Auto-gnereated formats such as those generated by pip freeze, pip-tools, Poetry etc. are not supported.Many package managers use custom version specifiers (e.g., ^, ~, *, etc.) to indicate which version to use. OSS scanner does not support these characters. Asside from the cases listed below, when it encounters these characters the scanner defaults to analyzing the "latest" version of the package. Similarly, when no version is provided, the scanner defaults to "latest".
Exceptions:
NPM - If a
package-lock.jsonfile is provided, we get the actual version from that file. If thepackage-lock.jsondoes not exist, you runnpm install, to generate apackage-lock.json.Python - If the version includes a comment after it, the comment will be removed and only the specific version will be used. For example: requests==2.25.1 # my comment
Maven -
If the version is defined via a property, it will be retrieved from the
properties.If the version is empty, the resolved version from
<dependencyManagement>will be used.
Containers Realtime Scanner
Checkmarx’s Containers Realtime scanner is a lightweight version of our Container Security scanner that analyzes your container images and quickly identifies risks associated with your images and associated packages. This includes images that use vulnerable packages or packages that we have identified as malicious.
Scans are triggered when the developer edits a project in the IDE that includes a container image file (e.g., Dockerfile). In addition, whenever the developer adds, moves or edits an image file within the IDE the project is re-scanned.
Notice
Editing a file triggers new detection after 1 second of inactivity.
Supported File Types
In the initial phase, the plugin supports the following popular image files:
Dockerfile
DockerCompose
Helm chart (limited support)
Known Limitations
Only images from the past 2 years are covered in our database.
Images with build tags, "alpha", "beta" or "nightly" are not covered in our database.
We collect data for many of the most commonly used repositories. However, we don't guarentee coverage for all repositories.
Checkmarx Secret Detection Realtime Scanner
Checkmarx Secret Detection reduces risk by quickly identifying sensitive credentials that are exposed in your code, enabling your development and security teams to remove and change the discovered secrets. Checkmarx identifies more than 210 different types of login credentials, access tokens, encryption keys, API keys, SSH keys, webhook URLs, and other unsecured sensitive information.
Whenever you edit a file in the IDE, Secret Detection is run on that file.
Notice
Editing a file triggers new detection after 1 second of inactivity.
Secret Detection Rules
The following table shows the list of rules that are used to detect various types of secrets.
Note
If you need to customize or extend secret scanning beyond the default rules, use the Secret Detection Query Editor.
Checkmarx Dev Assist Agentic-AI Remediation
When the user initiates a remediation action for a risk, a session is opened with the IDE’s AI assistant (GitHub Copilot for VS Code or the local AI in Cursor). Checkmarx gathers all relevant data about the risk and submits it to the AI assistant. For supported risk types, the AI assistant sends a request to our MCP which applies the relevant tools and returns a response with suggested remediation steps. The AI assistant implements the changes and offers the user the option to accept the changes or continue a chat session to refine the remediation.
Notice
If for some reason the Checkmarx MCP connection is unavailable, the remediation agent automatically falls back to the IDE's LLM to provide remediation suggestions. In this case, a notification is displayed indicating that the recommendations are not based on Checkmarx's specialized security models.
In addition, this tool enables use of AI to better understand the precise nature of a risk in the context of your code.
Remediating Vulnerable or Malicious Images and Packages
Remediation for OSS and Container risks is done by identifying the best non-vulnerable package that provides the same functionality as the vulnerable package. When our proprietary databases indicate that a remediated version of the current package is available, the remediated version that is closest to the current version is used. When no remediated version is available, our MCP server uses a dedicated AI tool to identify alternative packages that provide equivalent functionality.
Notice
Our MCP tool for identifying non-vulnerable versions is supported both for OSS and Containers. However, the MCP tool for finding alternative packages is not supported for containers.
When Checkmarx Dev Assist recommends updating a package version, our Safe Refactor feature searches your entire project for additional usage of that package and determines where and how the code needs to be refactored to accommodate the package update.
Remediation Logic
The following tables describe the logic of the remediation response for various cases.
Notice
When suggesting a non-vulnerable version or a more secure version, the MCP always recommends the smallest effective upgrade, rather than jumping to a higher version.
Remediating Exposed Secrets
Remediation is done by removing the hard coded secret from the code and replacing it with an Environment Variable that can be used to store the secret in a secure manner.
Remediating ASCA and IaC Vulnerabilities
For vulnerabilities in your code that were identified by the ASCA or IaC Realtime scanners, remediation is done by sending a customized prompt including all relevant data about the vulnerability instance to your IDEs AI assistant (Copilot or Cursor). The AI assistant then provides a remediated snippet that can be used in your code.
Initial Setup and Configuration
Warning
The Checkmarx VS Code extension includes the Checkmarx One Assist feature as part of the Checkmarx One platform experience and should be used by Checkmarx One customers with a Checkmarx One Assist license. The Checkmarx and Checkmarx Developer Assist VS Code extensions are mutually exclusive. To use the Checkmarx extension, ensure that the Checkmarx Developer Assist extension is uninstalled before installation.
Prerequisites
A Checkmarx One account with a Checkmarx One Assist license. For Checkmarx One accounts, the Checkmarx MCP must be activated for your tenant account in the Checkmarx One UI under Settings > Plugins page. This must be done by an account admin.
Checkmarx One users will need to provide:
an API Key (see Generating an API Key), OR
login credentials (Base URL, Tenant name, Username and Password)
For VS Code: supported for version 1.100.0 or above (supports both
settings.json(v1.100–1.101) andmcp.json( v1.102+))For VS Code and JetBrains, you must have GitHub Copilot installed
Installing and Configuring the Plugin
Install and setup the Checkmarx One extension in your IDE, as described in the following articles:
Notice
Make sure that you install version 2.35.0 or above.
AI Remediation
How to Remediate Risks Using AI
The following procedure explains how to remediate risks by clicking on the Fix button for a particular risk. Alternatively, you can request remediation via chat with your AI Agent, as decribed below.
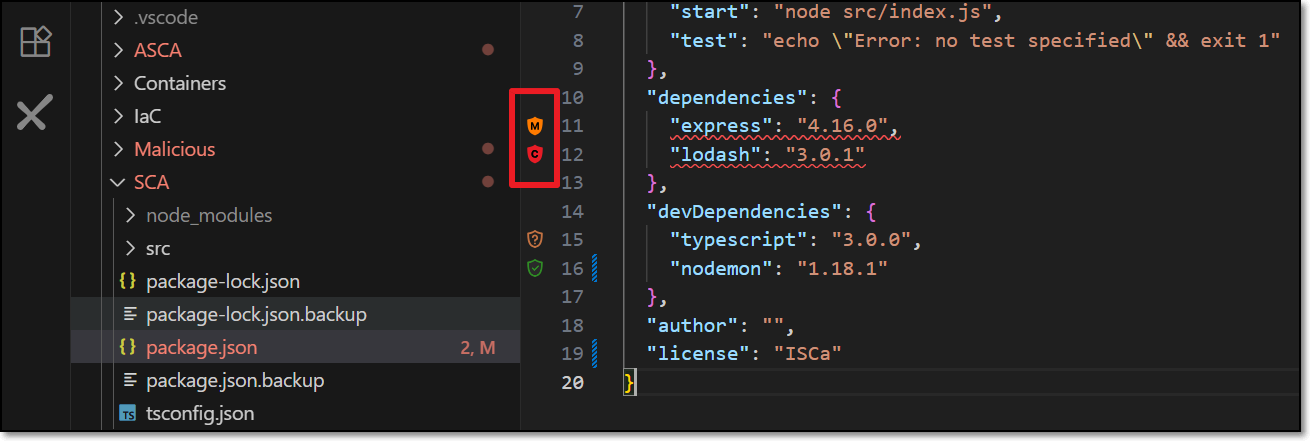
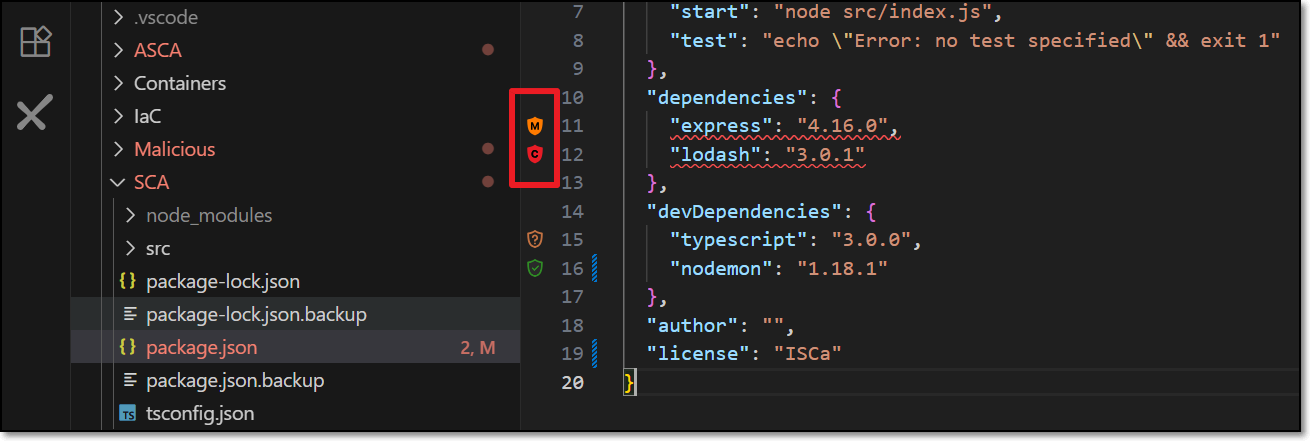
When Checkmarx realtime scanners identify a risk, it is flagged as a Problem, which is marked in the code with a squiggly underline and annotated in the margin with an icon that indicates the type of risk.
Hover over the vulnerable line of code.
The Checkmarx dialog opens.
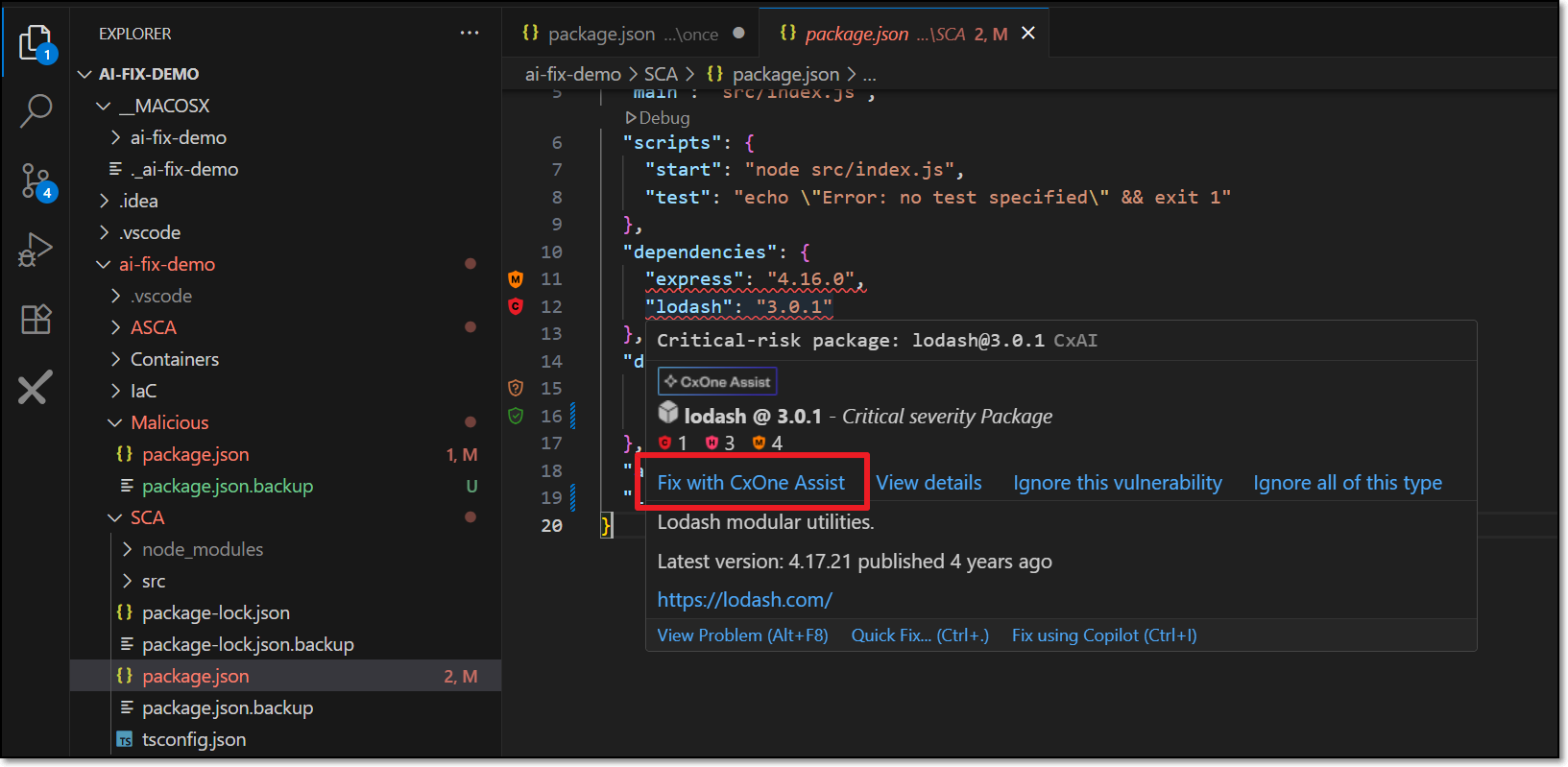
Click on Fix with CxOne Assist.
A Copilot session opens in the side panel and all relevant info is sent for analysis.
Notice
Depending on your IDE configuration, you may need to click Continue several times in order to complete the process.
Copilot automatically makes the necessary changes in the code in order to remediate the risk.
If you approve the change, click Accept.
The change is made and the code is rescanned to verify that the risk is no longer present.
If you want to improve on the suggestion, click Undo. You can then chat with Copilot to determine the best way of remediating the code.
Remediation via Chat
You can submit a request for CxOne Dev Assist remediation via natural language chat with your AI Agent. Just say that you want to fix a security risk and indicate which risk or risks you want to fix. Your AI will automatically route the request to the Checkmarx MCP and send all relevant data for analysis in order to generate the suggested remediation. The following are some examples of valid requests:
"Fix the vulnerability in line 26"
"Fix all critical vulnerabilities"
"Fix all SQL Injection risks"
"Remediate all vulnerable packages"
"Correct all critical issues in my JavaFile.java"
Things to Know About Dev Assist Chat
No need to mention "Checkmarx" explicitly; once Dev Assist is installed and running all remediation requests are handled via Checkmarx MCP
Support for multi-language prompts
Effective in single message context. Improved accuracy in context of an existing thread or finding.
By default, requests are interpreted in the context of the current open file (e.g., line 26 of the open file). You can specify a different file in your workspace.
How to Understand Risks Using AI
When Checkmarx realtime scanners identify a risk, it is flagged as a Problem, which is marked in the code with a squiggly underline and annotated in the margin with an icon that indicates the type of risk.
Hover over the vulnerable line of code.
The Checkmarx dialog opens.
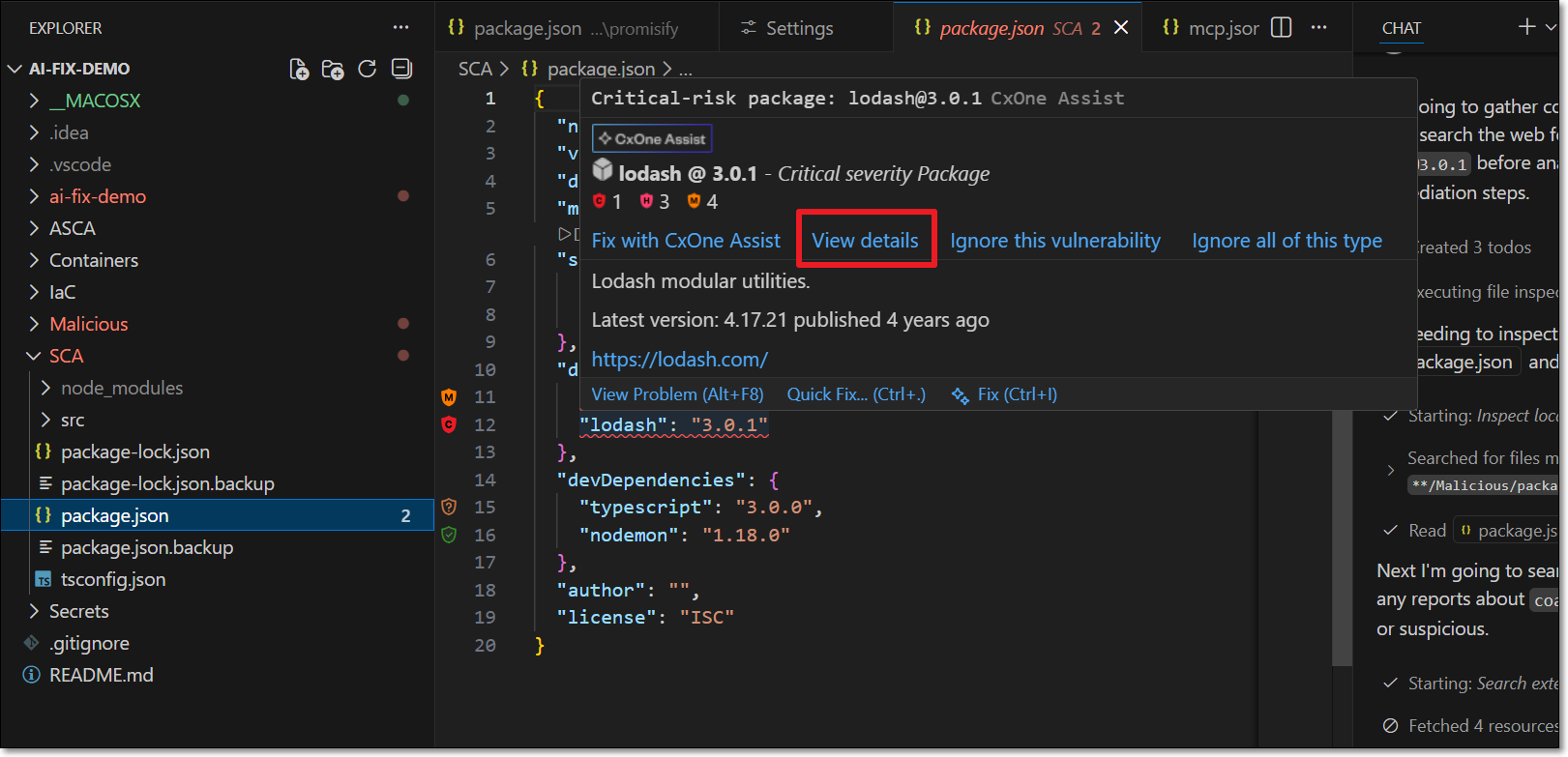
Click on View details.
A Copilot session opens in the side panel and all relevant info is sent for analysis.
Notice
Depending on your IDE configuration, you may need to click Continue several times in order to complete the process.
Copilot explains the precise nature of the risk in the context of your code. You can chat with Copilot to ask for further clarification.
Ignoring Risks
In order to help you focus on actionable risks, Checkmarx Dev Assist enables marking risks as Ignore, so that the risks will no longer be shown in your IDE. You can Revive a risk at any time to resume showing that risk. This can be applied to a specific instance of a risk or it can be applied to all instances of that risk in your project. You can revive the risk at any time to resume showing risks for that package.
Notice
For risks identified in open source packages, a risk instance refers to the entire package that the vulnerability is associated with.
To Ignore a risk
When Checkmarx realtime scanners identify a risk, it is flagged as a Problem, which is marked in the code with a squiggly underline and annotated in the margin with an icon that indicates the type of risk.
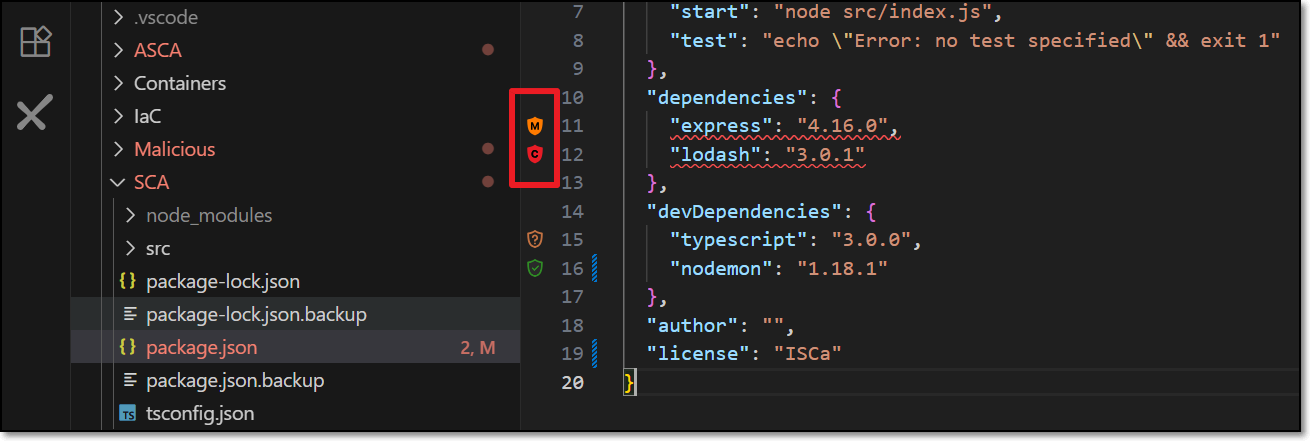
Hover over the vulnerable line of code.
The Checkmarx dialog opens.
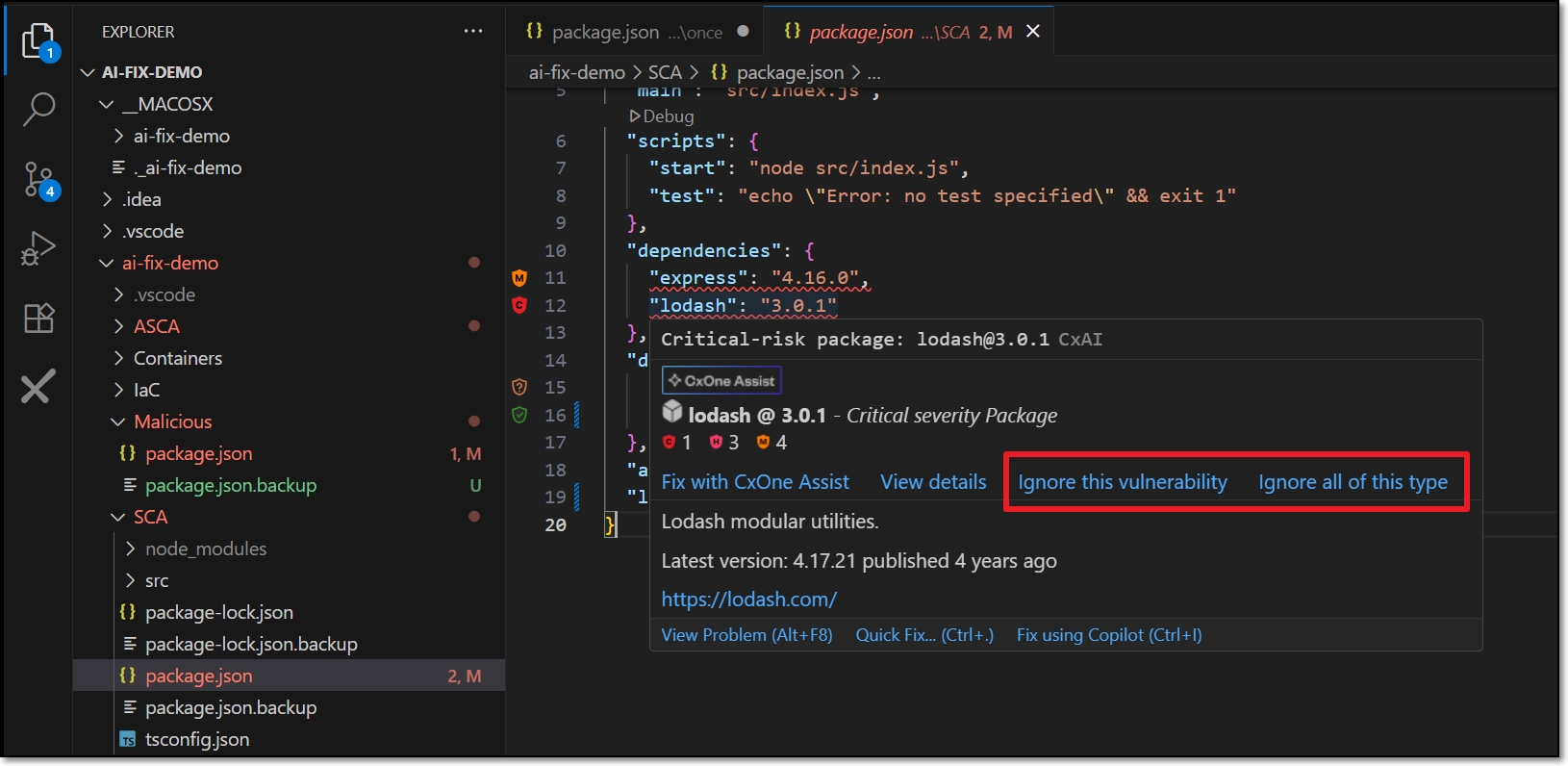
To ignore the risk in this particular instance, click on Ignore this vulnerability.
To ignore all instances of the risk, click on Ignore all of this type.
To revive a package:
Click on the Ignore icon in the bottom bar.
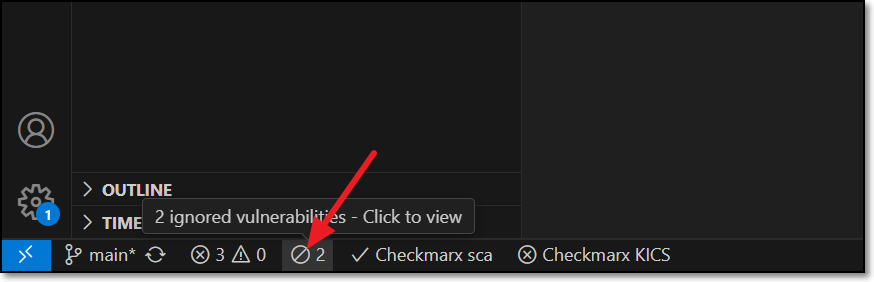
The Ignored Vulnerabilities tab opens.
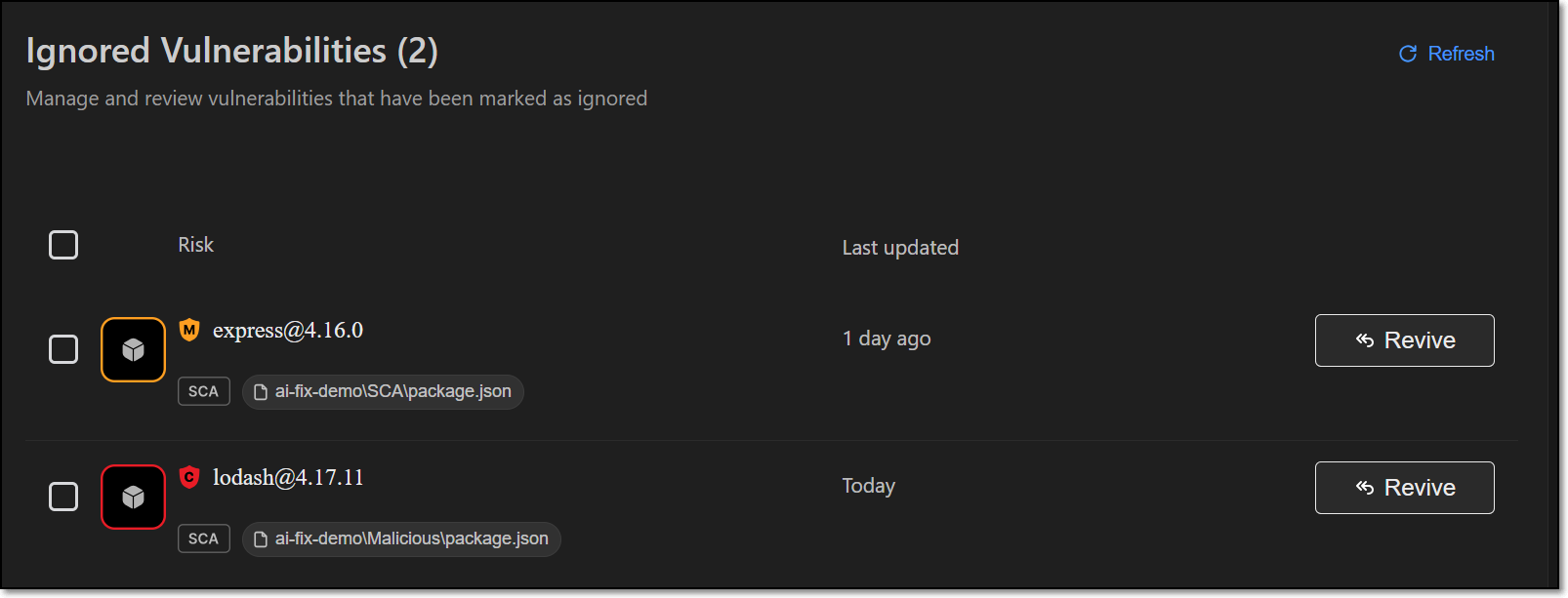
For the desired vulnerability click on the Revive button.
Notice
This can also be done as a bulk action for all selected items.
Troubleshooting - Manually Configuring the MCP Server
In case the automatic procedure fails. You can manually configure access to the Checkmarx MCP server using the appropriate procedure below, according to your IDE.
Installing MCP in VS Code
In case the automatic installation procedure fails. You can manually configure access to the Checkmarx MCP server using the following procedure.
If it does not already exist, create an mcp.json file at the following location:
${homeDir}\AppData\Roaming\Code\User\mcp.jsonAdd the "checkmarx" mcp using the following snippet, replacing the placeholders as follows:
Checkmarx_one_base_url - The base URL of your Checkmarx One environment.
Checkmarx_one_API_key - An API Key for your Checkmarx One account.
{ "servers":{ "checkmarx":{ "url":"<Checkmarx_one_base_url>/api/security-mcp/mcp", "headers":{ "cx-origin":"VSCode", "Authorization":"<Checkmarx_one_API_key>" } } }
Start running the MCP server as follows:
For the IaC Realtime scanner, select the Containers Management Tool used in your environment. Options are docker or podman.
Click View > Command Pallete and enter MCP:List Servers.
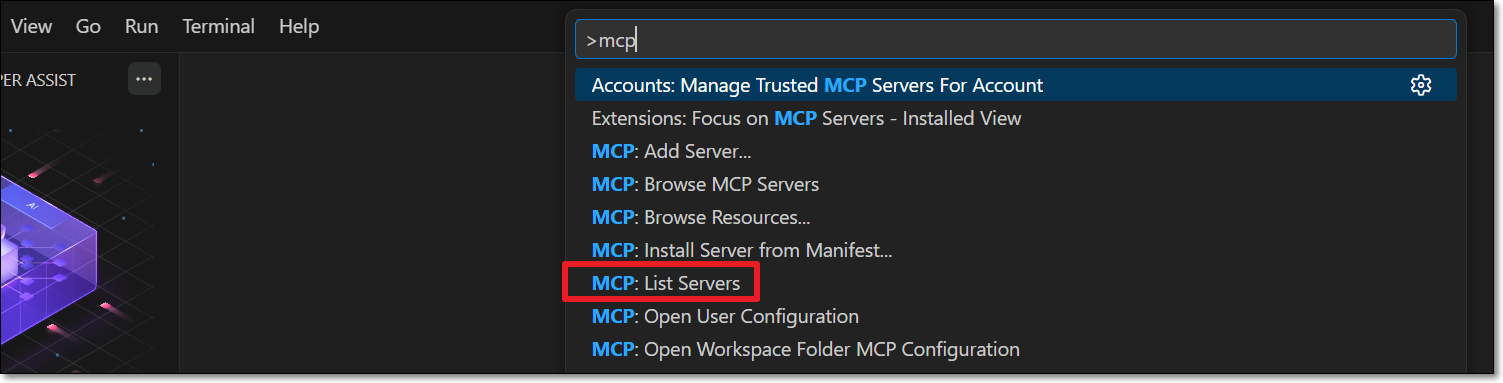
In the MCP servers list, select Checkmarx.
Click on Start Server.
Installing MCP in Cursor
In case the automatic installation procedure fails. You can manually configure access to the Checkmarx MCP server using the following procedure.
If it does not already exist, create an mcp.json file at the following location:
${homeDir}\.cursor\mcp.jsonAdd the "checkmarx" mcp using the following snippet, replacing the placeholders as follows:
Checkmarx_one_base_url - The base URL of your Checkmarx One environment.
Checkmarx_one_API_key - An API Key for your Checkmarx One account.
{ "mcpServers":{ "checkmarx":{ "url":"<Checkmarx_one_base_url>/api/security-mcp/mcp", "headers":{ "cx-origin":"Cursor", "Authorization":"<Checkmarx_one_API_key>" } } } }
Verify that your MCP server is running by opening Cursor Settings and under Tools & MCP > Installed MCP Servers, confirm that the Checkmarx toggle is enabled.
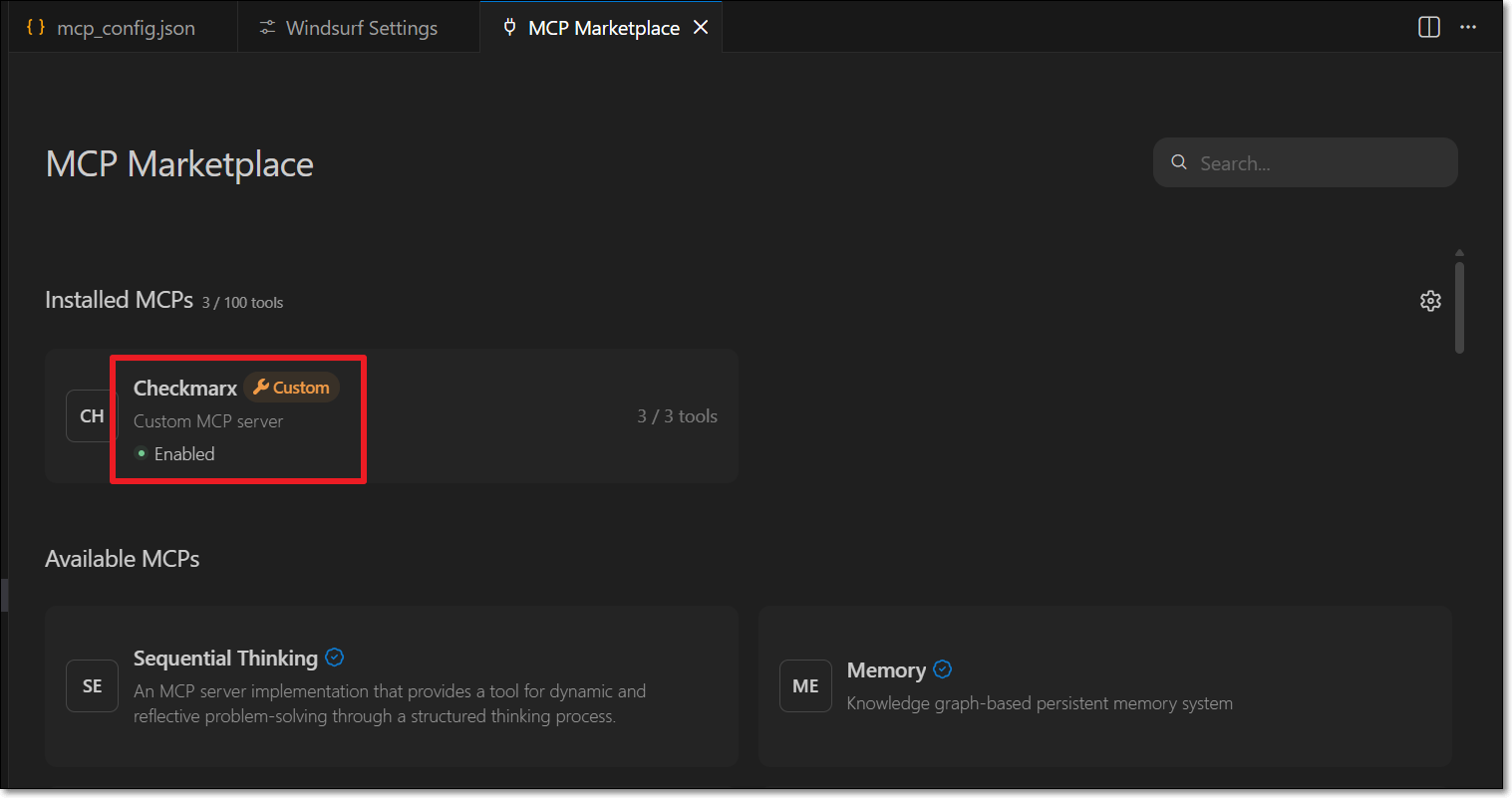
Installing MCP in Windsurf
In case the automatic installation procedure fails. You can manually configure access to the Checkmarx MCP server using the following procedure.
If it does not already exist, create an mcp_config.json file at the following location:
${homeDir}\.codeium\windsurf\mcp_config.jsonNotice
If you are using windsurf-next, then the file location should be
${homeDir}\.codeium\windsurf-next\mcp_config.jsonAdd the "checkmarx" mcp using the following snippet, replacing the placeholders as follows:
Checkmarx_one_base_url - The base URL of your Checkmarx One environment.
Checkmarx_one_API_key - An API Key for your Checkmarx One account.
{ "mcpServers":{ "checkmarx":{ "url":"<Checkmarx_one_base_url>/api/security-mcp/mcp", "headers":{ "cx-origin":"Windsurf", "Authorization":"<Checkmarx_one_API_key>" } } } }
Go to Settings > Windsurf Settings, and under Cascade, click Open MCP Marketplace. Make sure that the Checkmarx MCP is installed and enabled.
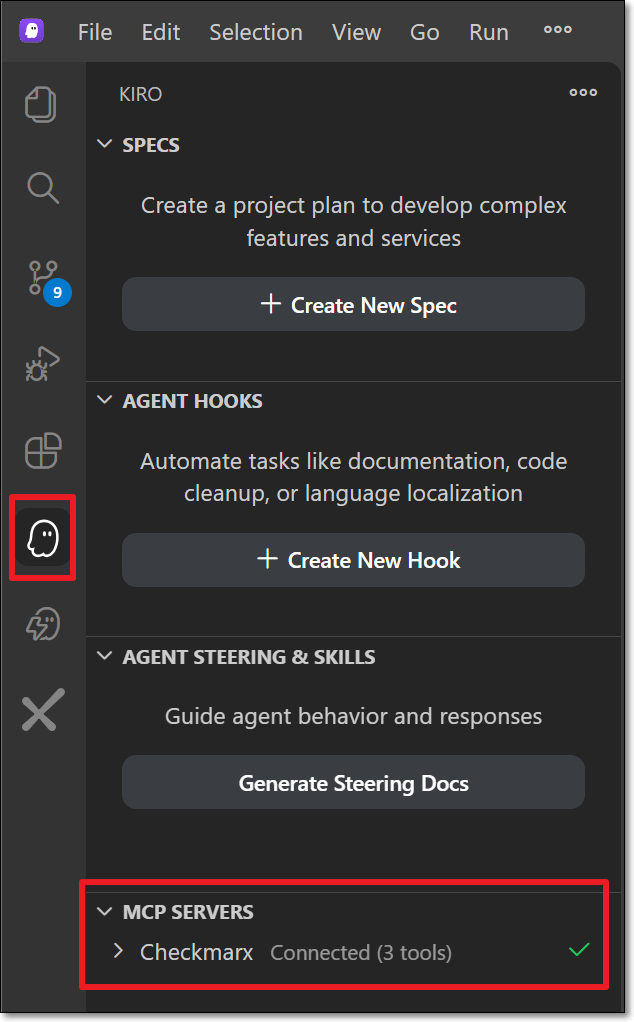
Installing MCP in Kiro
In case the automatic installation procedure fails. You can manually configure access to the Checkmarx MCP server using the following procedure.
If it does not already exist, create an mcp.json file at the following location:
${homeDir}\.kiro\settings\mcp.jsonAdd the "checkmarx" mcp using the following snippet, replacing the placeholders as follows:
Checkmarx_one_base_url - The base URL of your Checkmarx One environment.
Checkmarx_one_API_key - An API Key for your Checkmarx One account.
{ "mcpServers":{ "checkmarx":{ "url":"<Checkmarx_one_base_url>/api/security-mcp/mcp", "headers":{ "cx-origin":"Kiro", "Authorization":"<Checkmarx_one_API_key>" } } } }
Click on theKiro icon in the left-side navigation, and under MCP servers, confirm that Checkmarx is connected.
Installing MCP in JetBrains
In case the automatic installation procedure fails. You can manually configure access to the Checkmarx MCP server using the following procedure.
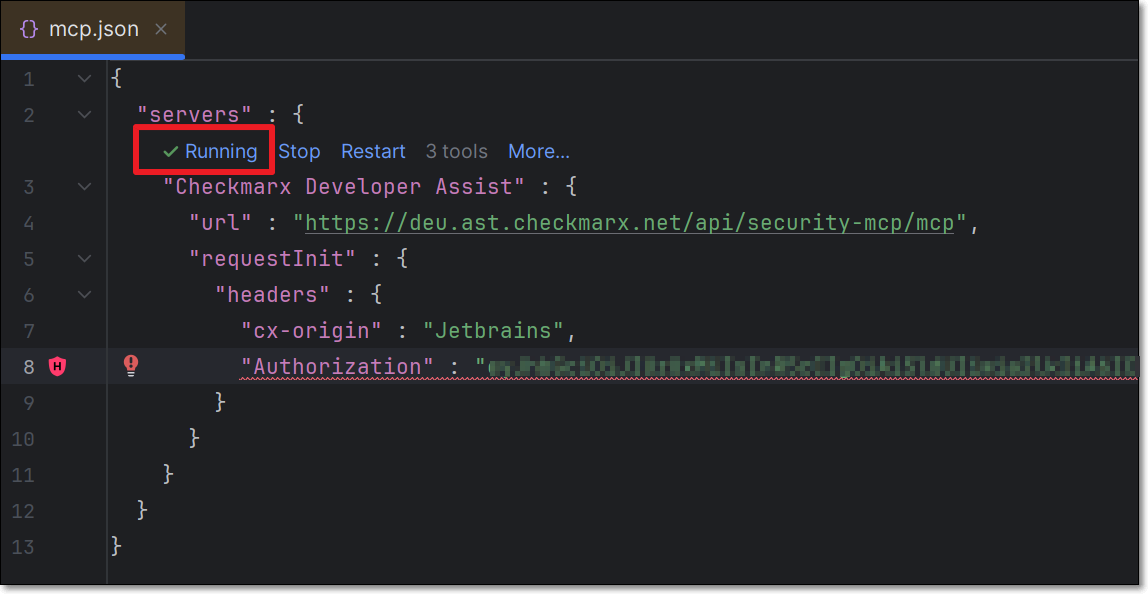
If it does not already exist, create an mcp.json file at the following location:
${homeDir}\AppData\Local\github-copilot\intellij\mcp.jsonAdd the "checkmarx" mcp using the following snippet, replacing the placeholders as follows:
Checkmarx_one_base_url - The base URL of your Checkmarx One environment.
Checkmarx_one_API_key - An API Key for your Checkmarx One account.
{ "servers":{ "Checkmarx":{ "url":"<Checkmarx_one_base_url>/api/security-mcp/mcp", "requestInit":{ "headers":{ "cx-origin":"Jetbrains", "Authorization":"<Checkmarx_one_API_key>" } } } } }
Confirm that the MCP is Running.