- Checkmarx Documentation
- Checkmarx One
- Checkmarx One User Guide
- Checkmarx One Reports
- SCA (Package) Reports
- SBOM Reports
SBOM Reports
SBOM Overview
Software Bill of Materials (SBOM), in simple words, is a list of all ingredients (i.e., components) of a software product. Just like you would check the ingredients of a food product before eating it, so too you should know what’s in your software before using it.
“On May 12, 2021, the President issued Executive Order 14028, “Improving the Nation's Cybersecurity.” [1] An initial step towards the Executive Order's goal of “enhancing software supply chain security” is transparency.
(Quote: federalregister.gov)
Generating an SBOM report may sound like a relatively simple task, but in most cases it’s not. Modern software projects make use of a long list of 3rd party software packages, each of which often calls on many other dependencies. This can create a very extensive tree of dependencies being used by your software.
SBOM reports follow a standard format that includes detailed information about each involved component. At a minimum, for each component, it must give the component’s name, supplier name, version, hashes and other unique identifiers, dependency relationship, author of SBOM data and timestamp.
It also needs to cover every software modification and update in order to reflect the current status of the project. This is best accomplished using an automated process that is integrated into your CI/CD pipeline.
Checkmarx SCA SBOM Reports
The first and most fundamental task in generating an SBOM is analyzing the software dependencies, which is a very natural task for a Software Composition Analysis platform such as Checkmarx SCA. But the ultimate purpose of SBOM is not just providing a list of materials, rather it is to identify potential risks. A standard SBOM doesn’t provide a simple way to detect risks associated with the 3rd party dependencies.
Checkmarx SCA leverages our existing infrastructure for identifying vulnerabilities as well as license and suspected malware risks to supplement the standard SBOM info. This creates an SBOM that provides real insight into the risks associated with your 3rd party components.
Our reports can be generated in CycloneDX and SPDX formats, with additional “property” fields showing supplemental risk data. The reports can be exported in XML or JSON format. You can generate SBOM reports for Checkmarx SCA Projects on which a scan has already run using the following methods:
Checkmarx SCA web portal (UI) - supports CycloneDX v1.6 and SPDX v2.2 formats.
Checkmarx One web portal (UI) - supports CycloneDX v1.6 and SPDX v2.2 formats.
Checkmarx One CLI - supports CycloneDX v1.6 and SPDX v2.2 formats.
SCA Resolver - supports CycloneDX v1.3 format.
Reports API - supports CycloneDX v1.3 format.
Export Service API - supports CycloneDX v1.6 and SPDX v2.2 formats.
Notice
For best results generating reports that are compliant with SBOM formatting specifications, we recommend using the Export Service API as opposed to the Reports API.
Viewing CycloneDx SBOM Reports
Checkmarx CycloneDx SCA SBOM Reports can be generated in XML or JSON format and can be viewed in standard XML and JSON viewers.
The report follows the CycloneDX v1.6 format, which includes standard SBOM fields such as: Id (Purl), Component name, Version, License and Hashes, all those will be included in every SBOM as a required fields list.
In addition, Checkmarx SCA adds a “properties” section with extended information for each library. This section contains key information about the risks associated with the library.
Sample XML:
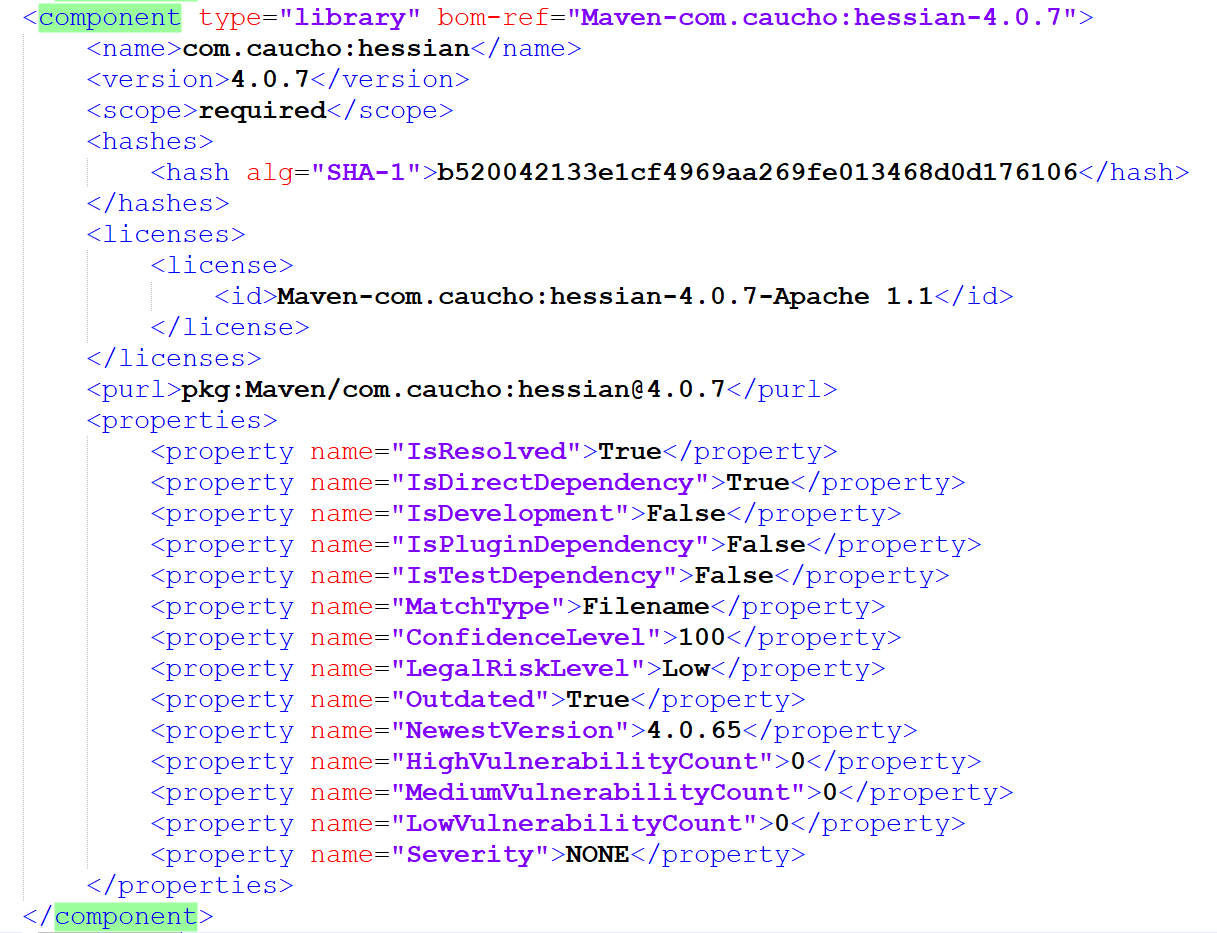 |
SBOM Component Dependencies
Each component contains its dependent components, and each dependency section contains a set of required fields and a properties section.
Sample Components Section (XML):
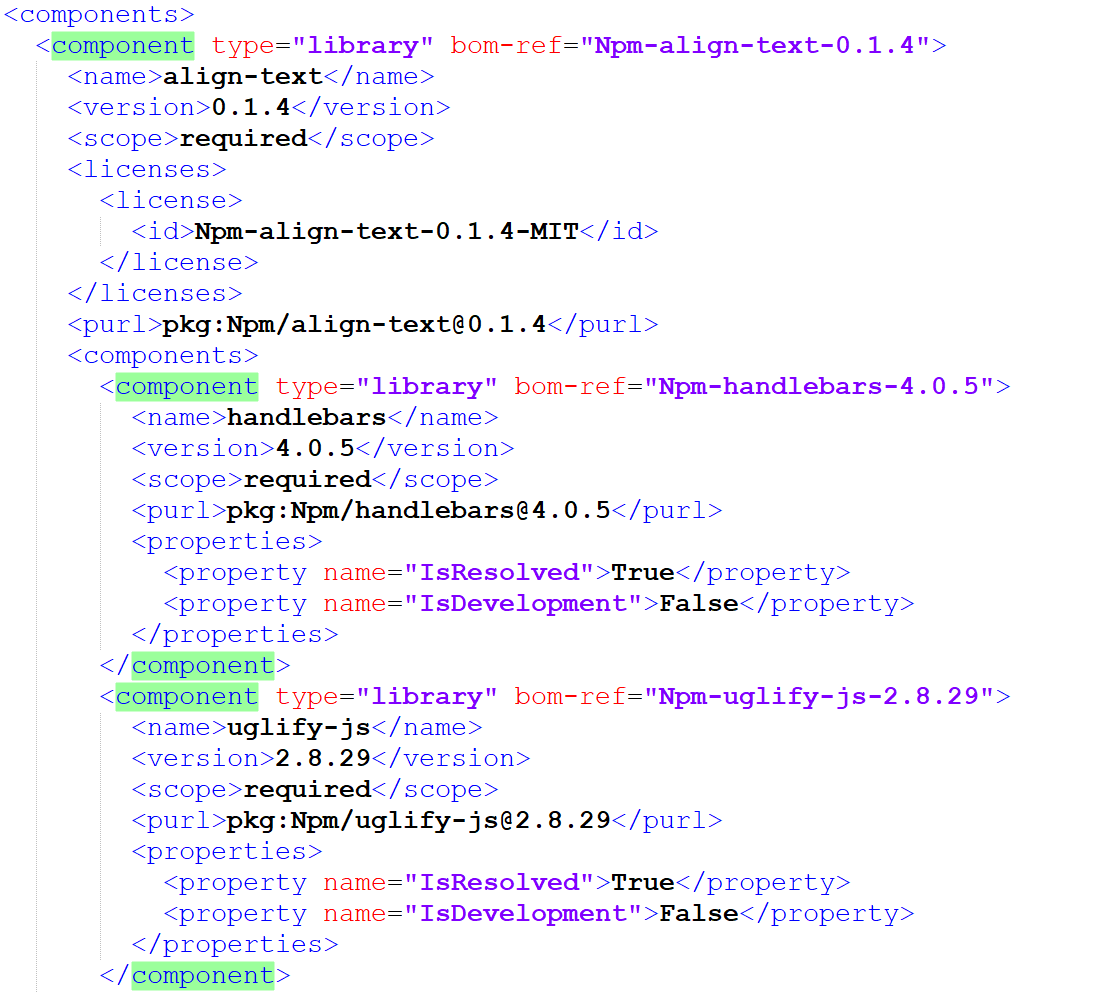 |